Cybersecurity scientists have unpacked a new Golang-dependent botnet known as Kraken that’s less than energetic development and attributes an array of backdoor capabilities to siphon sensitive information and facts from compromised Windows hosts.
“Kraken previously characteristics the capability to down load and execute secondary payloads, run shell commands, and choose screenshots of the victim’s program,” risk intelligence company ZeroFox explained in a report revealed Wednesday.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
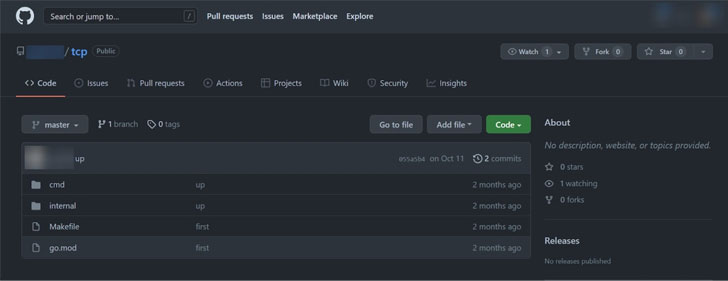
Uncovered initial in October 2021, early variants of Kraken have been discovered to be based on resource code uploaded to GitHub, despite the fact that it can be unclear if the repository in query belongs to the malware’s operators or if they only selected to get started their advancement working with the code as a foundation.
The botnet – not to be puzzled with a 2008 botnet of the same identify – is perpetuated applying SmokeLoader, which mainly functions as a loader for upcoming-stage malware, permitting it to quickly scale in dimensions and broaden its network.
Kraken’s features are explained to be continually evolving, with its authors fiddling with new factors and altering existing characteristics. Existing iterations of the botnet appear with features to manage persistence, obtain documents, operate shell instructions, and steal from diverse cryptocurrency wallets.
The wallets targeted consist of Armory, Atomic Wallet, Bytecoin, Electrum, Ethereum, Exodus, Guarda, Jaxx Liberty, and Zcash. Also continually downloaded and executed on the equipment is the RedLine Stealer, which is used to harvest saved credentials, autocomplete information, and credit card information and facts from web browsers.
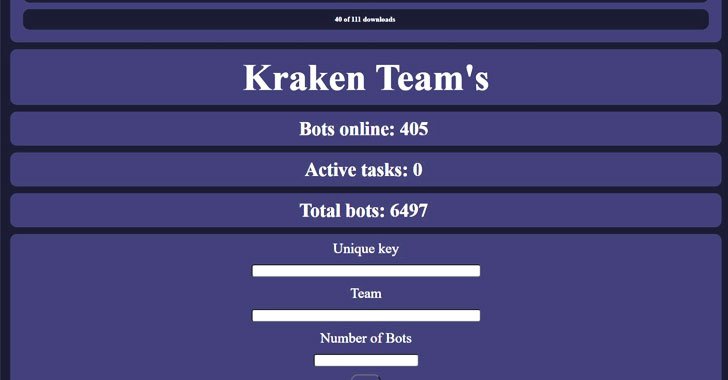
What is far more, the botnet arrives with an administration panel that allows the risk actor to upload new payloads, interact with a specific variety of bots, and perspective command heritage and info about the victims.
Above time, Kraken has also emerged as a conduit for the deployment of other generic info stealers and cryptocurrency miners, netting the botnet operators about $3,000 each individual thirty day period. “It is at the moment unidentified what the operator intends to do with the stolen credentials that have been gathered or what the conclude target is for developing this new botnet,” the scientists concluded.
Found this report fascinating? Follow THN on Facebook, Twitter and LinkedIn to study extra exclusive content we write-up.
Some sections of this report are sourced from:
thehackernews.com



 Moses Staff Hackers Targeting Israeli Organizations for Cyber Espionage
Moses Staff Hackers Targeting Israeli Organizations for Cyber Espionage