The decentralized file technique resolution identified as IPFS is turning out to be the new “hotbed” for hosting phishing internet sites, scientists have warned.
Cybersecurity agency Trustwave SpiderLabs, which disclosed specifics of the attack strategies, said it identified no much less than 3,000 e-mail made up of IPFS phishing URLs as an attack vector in the past a few months.
IPFS, small for InterPlanetary File Process, is a peer-to-peer (P2P) network to retailer and share files and data utilizing cryptographic hashes, rather of URLs or filenames, as is noticed in a traditional client-server solution. Each individual hash types the basis for a unique content material identifier (CID).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The concept is to generate a resilient distributed file program that allows knowledge to be stored throughout numerous desktops. This would permit facts to be accessed without having getting to rely on 3rd events such as cloud storage providers, proficiently producing it resistant to censorship.

“Taking down phishing content saved on IPFS can be complicated due to the fact even if it is taken off in 1 node, it may possibly still be accessible on other nodes,” Trustwave researchers Karla Agregado and Katrina Udquin reported in a report.
Complicating issues further more is the absence of a static Uniform Resource Identifier (URI) that can be utilized to find and block a solitary piece of malware-laden articles. This also implies it could be much more challenging to take down phishing web-sites hosted on IPFS.
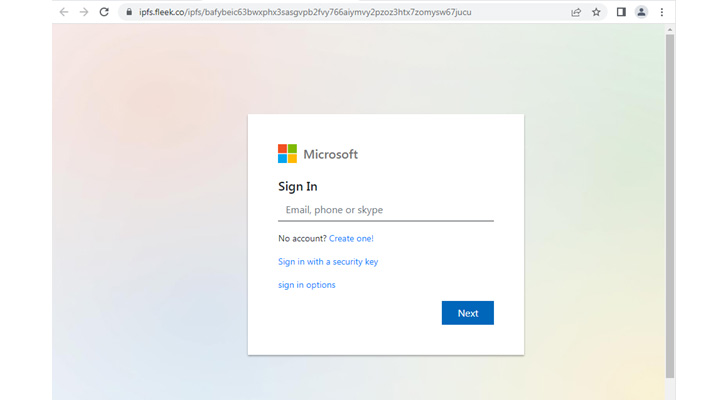
The attacks observed by Have faith in commonly entail some sort of social engineering to decreased the guard of targets in get to coax them to click fraudulent IPFS hyperlinks and activate the an infection chains.
These domains prompt probable victims to enter their qualifications to look at a document, monitor a package deal on DHL, or renew their Azure subscription, only to siphon the email addresses and passwords to a distant server.
“With info persistence, strong network, and small regulation, IPFS is possibly an suitable platform for attackers to host and share malicious articles,” the researcher reported.
The results occur amid a more substantial change in the email danger landscape, with Microsoft’s plans to block macros triggering threat actors to adapt their tactics to distribute executables that can guide to observe-on reconnaissance, information theft, and ransomware.
Seen in that mild, the use of IPFS marks yet another evolution in phishing, giving attackers an additional worthwhile playground to experiment with.
“Phishing techniques have taken a leap by making use of the thought of decentralized cloud solutions utilizing IPFS,” the researchers concluded.

“The spammers can very easily camouflage their actions by hosting their written content in legit web hosting providers or use multiple URL redirection procedures to assistance thwart scanners using URL reputation or automated URL examination.”
What is actually far more, these modifications have also been accompanied by the use of off-the-shelf phishing kits – a trend identified as phishing-as-a-provider (PhaaS) – that offer a brief and uncomplicated indicates for danger actors to mount attacks via email and SMS.
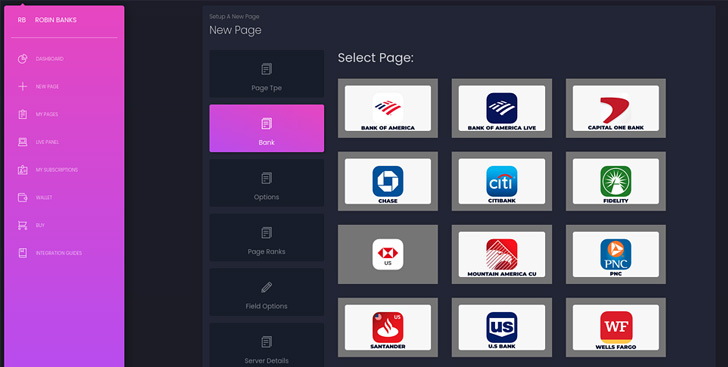
In fact, researchers from IronNet took the wraps off a large-scale campaign making use of a 4-month-outdated PhaaS system dubbed Robin Banks to plunder credentials and steal fiscal information and facts from customers of perfectly-recognized banking companies in Australia, Canada, the U.K., and the U.S.
“Whilst the principal commitment for scammers applying this kit seems to be financial, the kit does also request victims for their Google and Microsoft credentials after they journey to the phishing landing site, indicating it could also be utilised by much more innovative menace actors wanting to get initial obtain to company networks for ransomware or other submit-intrusion actions,” the scientists stated.
Identified this post interesting? Abide by THN on Facebook, Twitter and LinkedIn to examine far more distinctive material we article.
Some parts of this article are sourced from:
thehackernews.com

 Euro Police Bust €3m Internet Fraud Gang
Euro Police Bust €3m Internet Fraud Gang