REvil, the infamous ransomware gang guiding a string of cyberattacks in new years, seems to have gone off the radar after yet again, a little around a thirty day period right after the cybercrime group staged a shock return adhering to a two-month-very long hiatus.
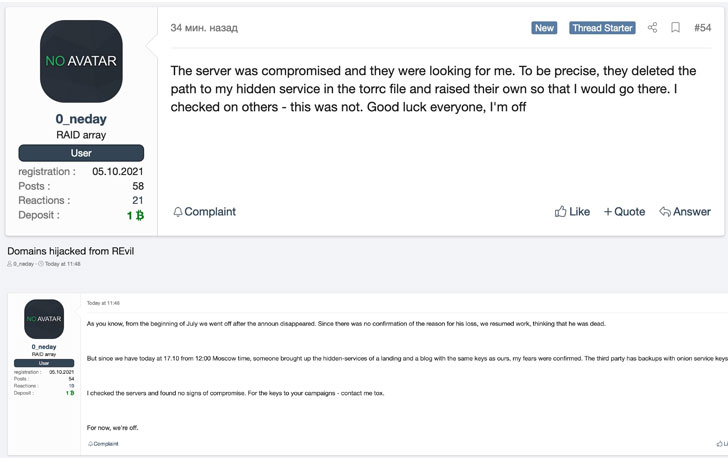
The enhancement, to start with spotted by Recorded Future’s Dmitry Smilyanets, arrives right after a member affiliated with the REvil operation posted on the XSS hacking forum that unidentified actors experienced taken regulate of the gang’s Tor payment portal and details leak site.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The server was compromised and they were being hunting for me. To be specific, they deleted the route to my hidden company in the torrc file and raised their possess so that I would (sic) go there. I checked on some others – this was not. Good luck everyone, I’m off,” consumer _neday explained in the write-up.
As of composing, it isn’t really obvious specifically who was behind the compromise of REvil’s servers, even though it would not be completely shocking if legislation enforcement companies played a role in bringing down the domains.
The Russia-linked ransomware group attracted significant scrutiny following its attacks on JBS and Kaseya previously this year, prompting it to get its darknet web-sites offline in July 2021. But on September 9, 2021, REvil created an unexpected return, resurfacing equally its knowledge leak website as properly as payment and negotiation portals back on the net.
Final thirty day period, the Washington Article claimed that the U.S. Federal Bureau of Investigation (FBI) held back again from sharing the decryptor with the victims of Kaseya ransomware attack for practically a few weeks, which it obtained from accessing the group’s servers, as part of a plan to disrupt the gang’s destructive activities. “The planned takedown by no means transpired simply because in mid-July REvil’s platform went offline — devoid of U.S. government intervention — and the hackers disappeared right before the FBI had a likelihood to execute its plan,” the report extra.

A common decryptor was at some point shared by Romanian cybersecurity organization Bitdefender in late July right after getting the key from a “regulation enforcement spouse.”
Even though it is not uncommon for ransomware groups to evolve, splinter, or reorganize less than new names, the prison field has increasingly occur under the lens for putting critical infrastructure, even as more cybercriminals are recognizing the profitability of ransomware, in part bolstered by the unregulated cryptocurrency landscape, consequently enabling danger actors to extort victims for electronic payments with impunity.
Observed this post interesting? Stick to THN on Fb, Twitter and LinkedIn to browse far more exclusive written content we publish.
Some components of this article are sourced from:
thehackernews.com

 Is Your Data Safe? Check Out Some Cybersecurity Master Classes
Is Your Data Safe? Check Out Some Cybersecurity Master Classes