A monetarily enthusiastic marketing campaign that targets Android units and spreads mobile malware through SMS phishing strategies since at least 2018 has unfold its tentacles to strike victims positioned in France and Germany for the initial time.
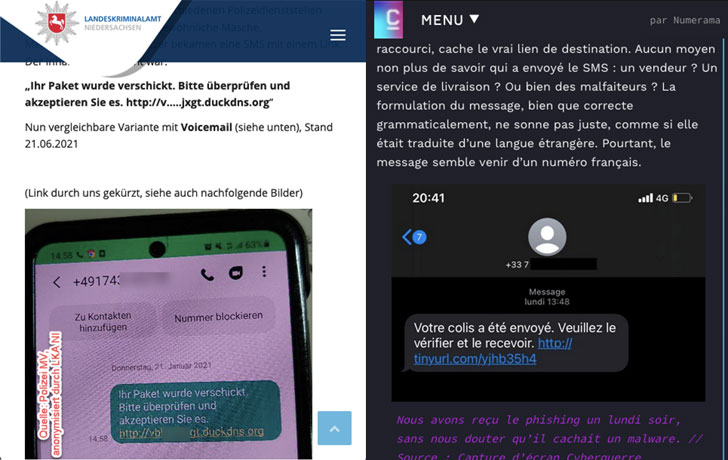
Dubbed Roaming Mantis, the newest spate of routines observed in 2021 require sending faux shipping-associated texts containing a URL to a landing website page from exactly where Android customers are contaminated with a banking trojan recognised as Wroba whereas iPhone people are redirected to a phishing webpage that masquerades as the formal Apple web page.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The best impacted countries, centered on telemetry details collected by Kaspersky amongst July 2021 and January 2022, are France, Japan, India, China, Germany, and Korea.
Also tracked below the names MoqHao and XLoader (not to be confused with the facts-stealer malware of the identical identify concentrating on Windows and macOS), the group’s activity has continued to develop geographically even as the operators broadened their attack methods to mine cryptocurrency from Apple products and evade detection.
The most important intention of the marketing campaign is to deploy Wroba, which capabilities equally as a adware and banking malware, with capabilities to replace respectable applications with destructive variations and steal qualifications related with victims’ online bank accounts.
Further more examination of the malware artifacts has uncovered the change in programming language from Java to Kotlin and the addition of two new backdoor instructions that let Wroba to exfiltrate galleries and images from infected products.
“1 feasible circumstance is that the criminals steal details from this sort of issues as driver’s licenses, health and fitness coverage playing cards or bank cards, to sign up for contracts with QR code payment products and services or cell payment services,” the researchers reported. “The criminals are also capable to use stolen shots to get funds in other ways, this sort of as blackmail or sextortion.”
Observed this report exciting? Adhere to THN on Fb, Twitter and LinkedIn to go through far more exclusive articles we publish.
Some components of this article are sourced from:
thehackernews.com




 Microsoft disables VBA macros in Office by default following years of complaints
Microsoft disables VBA macros in Office by default following years of complaints