Researchers have disclosed a number of vulnerabilities impacting Ultra-wideband (UWB) Authentic-time Finding Units (RTLS), enabling menace actors to launch adversary-in-the-middle (AitM) attacks and tamper with site details.
“The zero-days located exclusively pose a security risk for workers in industrial environments,” cybersecurity agency Nozomi Networks disclosed in a complex write-up previous week. “If a danger actor exploits these vulnerabilities, they have the means to tamper with safety zones designated by RTLS to secure personnel in dangerous places.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
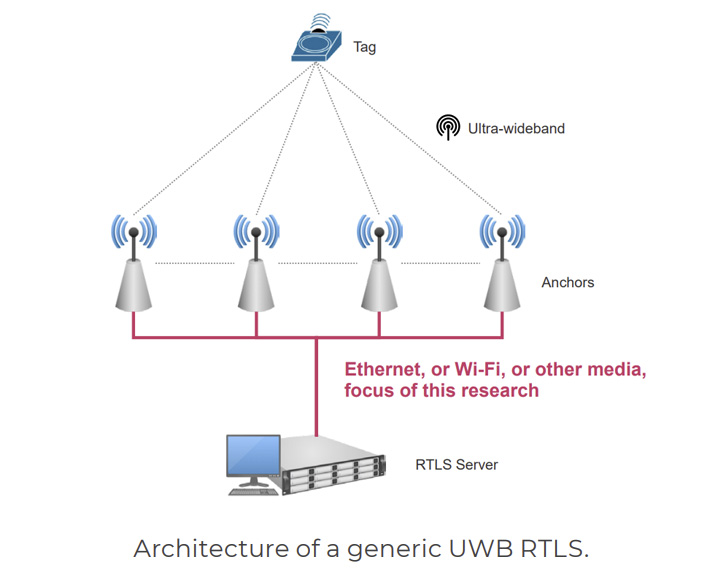
RTLS is made use of to immediately detect and track the location of objects or men and women in real-time, generally inside a confined indoor region. This is attained by creating use of tags that are hooked up to assets, which broadcast USB signals to set reference details named anchors that then decide their site.
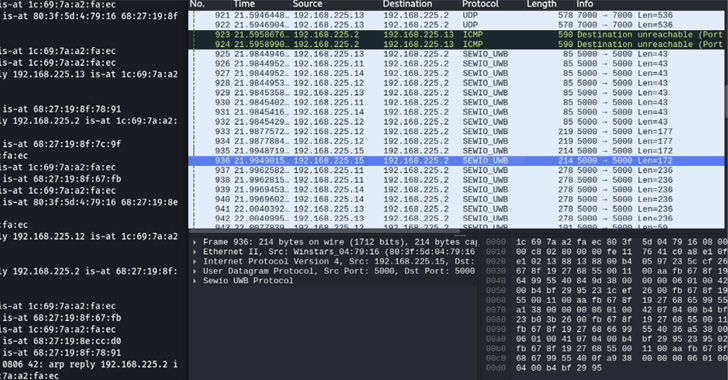
But flaws identified in RTLS options – Sewio Indoor Monitoring RTLS UWB Wi-Fi Kita and Avalue Renity Artemis Organization Package – meant that they could be weaponized to intercept network packets exchanged in between anchors and the central server and stage traffic manipulation attacks.
Set simply, the thought is to estimate the anchor coordinates and use it to manipulate the geofencing rules of the RTLS method, proficiently tricking the software program into granting access to limited spots and even causing disruption to creation environments.
“If an attacker is able to change the posture of a tag by modifying the positioning packet linked to that tag, it may perhaps become probable to enter limited zones or steal useful merchandise with out the operators staying able to detect that a destructive exercise is ongoing.”

Even even worse, by altering the posture of tags and inserting them within parts monitored by geofencing policies, an adversary can result in the stoppage of entire creation traces by exhibiting that a employee is nearby even when no a person is actually about.
In an alternate circumstance, the area facts could be tampered to spot a employee outside of a geofencing zone so that hazardous machinery would restart while a employee is in near proximity, posing extreme safety dangers.
But it is worth pointing out that performing so necessitates that an attacker both compromises a laptop connected to that network, or surreptitiously provides a rogue machine to acquire unauthorized entry to the network.
To remediate this sort of attacks, it’s proposed to implement network segregation and incorporate a visitors encryption layer on major of the existing communications to avoid AitM attacks.
“Weak security specifications in critical computer software can lead to protection issues that are not able to be disregarded,” scientists Andrea Palanca, Luca Cremona, and Roya Gordon explained. “Exploiting secondary communications in UWB RTLS can be tough, but it is doable.”
Discovered this post exciting? Observe THN on Fb, Twitter and LinkedIn to examine additional unique articles we publish.
Some sections of this write-up are sourced from:
thehackernews.com

 Car Dealership Hit by Major Ransomware Attack
Car Dealership Hit by Major Ransomware Attack