Print administration software package service provider PaperCut explained that it has “proof to propose that unpatched servers are being exploited in the wild,” citing two vulnerability experiences from cybersecurity company Pattern Micro.
“PaperCut has conducted assessment on all client experiences, and the earliest signature of suspicious action on a purchaser server probably joined to this vulnerability is 14th April 01:29 AEST / 13th April 15:29 UTC,” it further more extra.
The update arrives as the U.S. Cybersecurity and Infrastructure Security Company (CISA) extra a critical flaw (CVE-2023-27350, CVSS rating – 9.8) to the Identified Exploited Vulnerabilities (KEV) catalog, based on proof of active exploitation.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
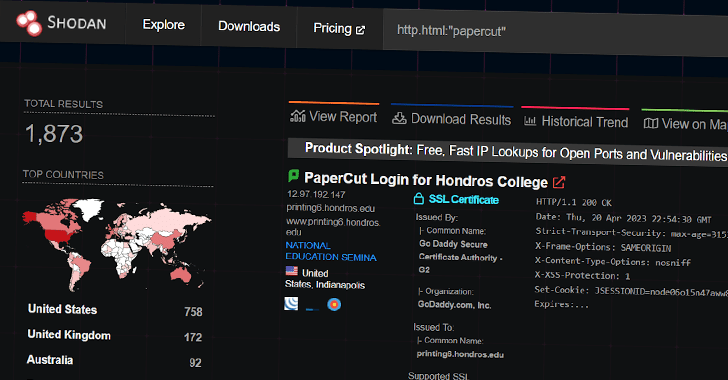
Cybersecurity organization Huntress, which observed about 1,800 publicly exposed PaperCut servers, reported it noticed PowerShell commands being spawned from PaperCut software to install distant management and maintenance (RMM) program like Atera and Syncro for persistent access and code execution on the contaminated hosts.
Supplemental infrastructure assessment has unveiled the domain hosting the tools – windowservicecemter[.]com – was registered on April 12, 2023, also hosting malware like TrueBot, even though the company explained it did not instantly detect the deployment of the downloader.
TrueBot is attributed to a Russian felony entity acknowledged as Silence, which in change has historical links with Evil Corp and its overlapping cluster TA505, the latter of which has facilitated the distribution of Cl0p ransomware in the past.
“Although the top goal of the existing exercise leveraging PaperCut’s computer software is unknown, these inbound links (albeit to some degree circumstantial) to a recognized ransomware entity are concerning,” Huntress scientists explained.
Approaching WEBINARZero Rely on + Deception: Study How to Outsmart Attackers!
Learn how Deception can detect superior threats, halt lateral motion, and boost your Zero Have faith in approach. Be part of our insightful webinar!
Preserve My Seat!
“Probably, the access gained through PaperCut exploitation could be applied as a foothold primary to abide by-on movement inside the sufferer network, and ultimately ransomware deployment.”
Buyers are recommended to upgrade to the fastened versions of PaperCut MF and NG (20.1.7, 21.2.11, and 22..9) as shortly as achievable, irrespective of no matter whether the server is “obtainable to external or interior connections,” to mitigate possible pitfalls.
Customers who are not able to improve to a security patch are encouraged to lock down network accessibility to the servers by blocking all inbound site visitors from external IPs and limiting IP addresses to only individuals belonging to verified web-site servers.
Uncovered this article interesting? Stick to us on Twitter and LinkedIn to examine additional unique written content we write-up.
Some sections of this write-up are sourced from:
thehackernews.com

 Lazarus X_TRADER Hack Impacts Critical Infrastructure Beyond 3CX Breach
Lazarus X_TRADER Hack Impacts Critical Infrastructure Beyond 3CX Breach