The Pc Emergency Reaction Crew of Ukraine (CERT-UA) on Tuesday disclosed that it thwarted a cyberattack by Sandworm, a hacking team affiliated with Russia’s armed forces intelligence, to sabotage the functions of an unnamed energy supplier in the country.
“The attackers attempted to just take down many infrastructure factors of their goal, particularly: Electrical substations, Windows-operated computing techniques, Linux-operated server products, [and] energetic network products,” The Condition Assistance of Exclusive Communications and Info Safety of Ukraine (SSSCIP) mentioned in a statement.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
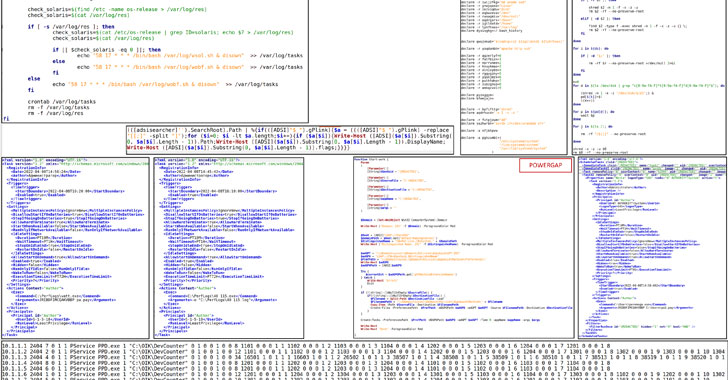
Slovak cybersecurity agency ESET, which collaborated with CERT-UA to analyze the attack, explained the attempted intrusion involved the use of ICS-capable malware and typical disk wipers, with the adversary unleashing an updated variant of the Industroyer malware, which was to start with deployed in a 2016 assault on Ukraine’s electricity grid.

“The Sandworm attackers produced an endeavor to deploy the Industroyer2 malware in opposition to substantial-voltage electrical substations in Ukraine,” ESET described. “In addition to Industroyer2, Sandworm used many destructive malware families like CaddyWiper, OrcShred, SoloShred, and AwfulShred.”
The victim’s electrical power grid network is believed to have penetrated in two waves, the preliminary compromise taking place no later than February 2022, coinciding with the Russian invasion of Ukraine, and a abide by-on infiltration in April that allowed the attackers to add Industroyer2.
Industroyer, also known as “CrashOverride” and dubbed the “most important danger to industrial manage systems since Stuxnet,” is both of those modular and capable of getting immediate management of switches and circuit breakers at an energy distribution substation.
The new edition of the advanced and really customizable malware, like its predecessor, leverages an industrial conversation protocol identified as IEC-104 to commandeer the industrial machines such as safety relays that are utilised in electrical substations.
Forensic evaluation of the artifacts left guiding by Industroyer2 has discovered a compilation timestamp of March 23, 2022, indicating that the attack experienced been prepared for at the very least two months. That mentioned, it really is even now unclear how the qualified electricity facility was at first compromised, or how the intruders moved from the IT network to the Industrial Regulate Technique (ICS) network.
ESET stated that the harmful steps from the firm’s infrastructure ended up scheduled to consider place on April 8, 2022, but ended up ultimately foiled. This was established to be followed by the execution of a data wiper known as CaddyWiper 10 minutes later on on the exact same equipment to erase traces of the Industroyer2 malware.
Along with Industroyer2 and CaddyWiper, the targeted power provider’s network is also said to have been infected by a Linux worm identified as OrcShred, which is then applied to spread two diverse wiper malware aimed at Linux and Solaris systems — AwfulShred and SoloShred — and render the devices inoperable.
The results come shut on the heels of the courtroom-authorized takedown of Cyclops Blink, an innovative modular botnet controlled by the Sandworm threat actor, previous week.
CERT-UA, for its portion, has also warned of a selection of spear-phishing campaigns mounted by Armageddon, an additional Russia-based group with ties to the Federal Security Support (FSB) that has attacked Ukrainian entities considering that at the very least 2013.
“Ukraine is when all over again at the heart of cyberattacks focusing on their critical infrastructure,” ESET reported. “This new Industroyer campaign follows a number of waves of wipers that have been focusing on numerous sectors in Ukraine.”
Discovered this short article appealing? Stick to THN on Fb, Twitter and LinkedIn to browse much more distinctive content we submit.
Some elements of this write-up are sourced from:
thehackernews.com



 Microsoft’s massive 145-vulnerability Patch Tuesday fixes ten critical exploits
Microsoft’s massive 145-vulnerability Patch Tuesday fixes ten critical exploits