A danger cluster connected to the Russian nation-condition actor tracked as Sandworm has ongoing its focusing on of Ukraine with commodity malware by masquerading as telecom suppliers, new conclusions demonstrate.
Recorded Upcoming reported it found new infrastructure belonging to UAC-0113 that mimics operators like Datagroup and EuroTransTelecom to supply payloads such as Colibri loader and Warzone RAT.
The attacks are claimed to be an enlargement of the exact marketing campaign that previously distributed DCRat (or DarkCrystal RAT) making use of phishing emails with legal aid-themed lures against suppliers of telecommunications in Ukraine.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Sandworm is a harmful Russian threat team which is most effective recognised for carrying out attacks this kind of as the 2015 and 2016 focusing on of Ukrainian electrical grid and 2017’s NotPetya attacks. It is verified to be Unit 74455 of Russia’s GRU military intelligence agency.
The adversarial collective, also acknowledged as Voodoo Bear, sought to damage superior-voltage electrical substations, desktops and networking machines for the 3rd time in Ukraine before this April by way of a new variant of a piece of malware recognized as Industroyer.
Russia’s invasion of Ukraine has also had the group unleash several other attacks, including leveraging the Follina vulnerability (CVE-2022-30190) in the Microsoft Windows Guidance Diagnostic Tool (MSDT) to breach media entities in the Jap European country.
In addition, it was uncovered as the mastermind at the rear of a new modular botnet termed Cyclops Blink that enslaved internet-related firewall products and routers from WatchGuard and ASUS.
The U.S. govt, for its part, has declared up to $10 million in rewards for facts on six hackers associated with the APT group for collaborating in malicious cyber functions against critical infrastructure in the state.
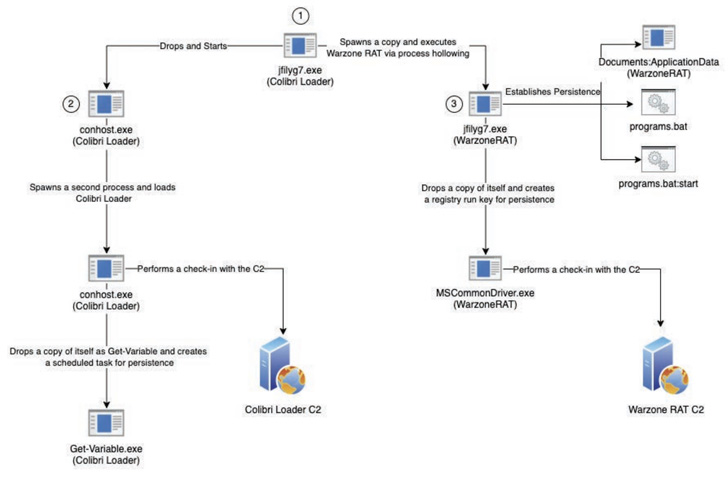
“A transition from DarkCrystal RAT to Colibri Loader and Warzone RAT demonstrates UAC-0113’s broadening but continuing use of publicly obtainable commodity malware,” Recorded Long term claimed.
The attacks entail the fraudulent domains hosting a web page purportedly about “Odesa Regional Military Administration,” while an encoded ISO picture payload is stealthily deployed through a system referred to as HTML smuggling.

HTML smuggling, as the name goes, is an evasive malware shipping method that leverages authentic HTML and JavaScript features to distribute malware and get about regular security controls.
Recorded Future also mentioned it identified factors of similarities with a different HTML dropper attachment set to use by the APT29 menace actor in a marketing campaign aimed at Western diplomatic missions between May well and June 2022.
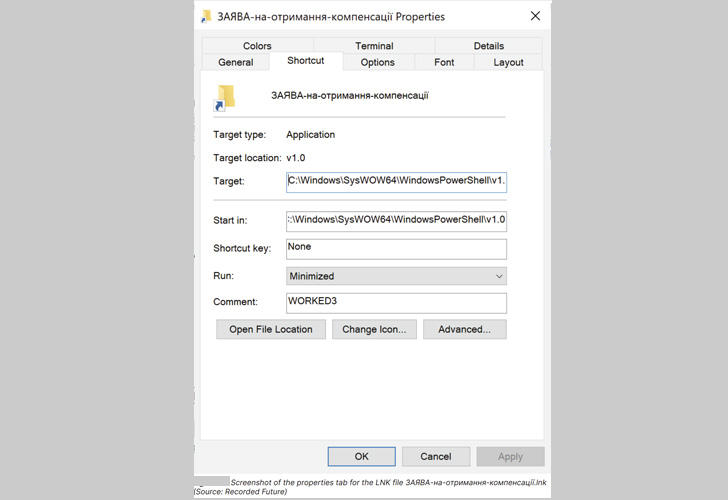
Embedded in the ISO file, which was established on August 5, 2022, are three files, such as an LNK file that methods the victim into activating the an infection sequence, ensuing in the deployment of both equally Colibri loader and Warzone RAT to the focus on equipment.
The execution of the LNK file also launches an innocuous decoy document – an application for Ukrainian citizens to request for monetary compensation and gasoline bargains – in an attempt to conceal the destructive functions.
Observed this report appealing? Adhere to THN on Fb, Twitter and LinkedIn to examine more exclusive information we write-up.
Some pieces of this article are sourced from:
thehackernews.com

 American Airlines hit by data breach
American Airlines hit by data breach