Point out-sponsored hackers affiliated with Russia are powering a new collection of intrusions working with a beforehand undocumented implant to compromise devices in the U.S., Germany, and Afghanistan.
Cisco Talos attributed the attacks to the Turla innovative persistent danger (APT) group, coining the malware “TinyTurla” for its limited functionality and successful coding design and style that makes it possible for it to go undetected. Attacks incorporating the backdoor are considered to have happened because 2020.
“This simple backdoor is very likely employed as a 2nd-opportunity backdoor to maintain accessibility to the process, even if the principal malware is removed,” the scientists explained. “It could also be applied as a next-stage dropper to infect the technique with additional malware.” Also, TinyTurla can add and execute files or exfiltrate sensitive data from the contaminated device to a remote server, even though also polling the command-and-regulate (C2) station every single 5 seconds for any new instructions.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Also regarded by the monikers Snake, Venomous Bear, Uroburos, and Iron Hunter, the Russian-sponsored espionage outfit is recognized for its cyber offensives targeting government entities and embassies spanning throughout the U.S., Europe, and Jap Bloc nations. The TinyTurla campaign requires the use of a .BAT file to deploy the malware, but the precise intrusion route stays unclear as still.
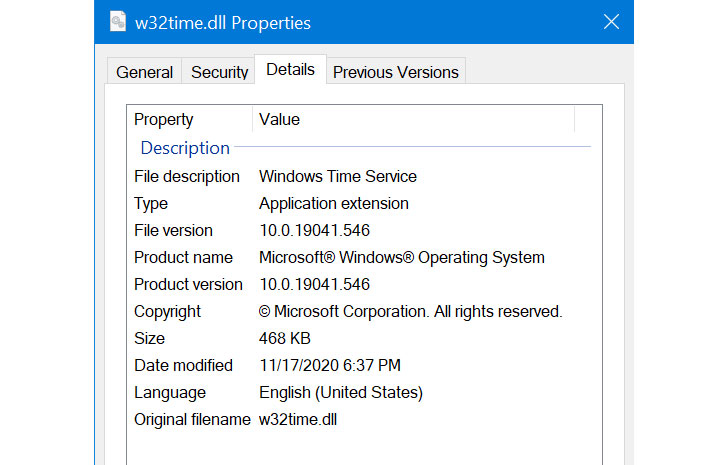
The novel backdoor — which camouflages as an innocuous but bogus Microsoft Windows Time Service (“w32time.dll”) to fly under the radar — is orchestrated to sign-up by itself and build communications with an attacker-managed server to get more guidelines that assortment from downloading and executing arbitrary procedures to uploading the effects of the instructions again to the server.
TinyTurla’s inbound links to Turla come from overlaps in the modus operandi, which has been earlier identified as the very same infrastructure utilised by the group in other campaigns in the previous. But the attacks also stand in stark contrast to the outfit’s historical covert strategies, which have provided compromised web servers and hijacked satellite connections for their C2 infrastructure, not to mention evasive malware like Crutch and Kazuar.

“This is a good case in point of how easy destructive companies can be forgotten on present day devices that are clouded by the myriad of legit services functioning in the history at all instances,” the scientists noted.
“It can be additional essential now than ever to have a multi-layered security architecture in area to detect these forms of attacks. It just isn’t not likely that the adversaries will regulate to bypass one or the other security actions, but it is a great deal more challenging for them to bypass all of them.”
Discovered this short article exciting? Observe THN on Facebook, Twitter and LinkedIn to go through much more exceptional content we write-up.
Some components of this post are sourced from:
thehackernews.com


 New Android Malware Steals Financial Data from 378 Banking and Wallet Apps
New Android Malware Steals Financial Data from 378 Banking and Wallet Apps