A group of teachers from the College of California and Tsinghua College has uncovered a sequence of critical security flaws that could guide to a revival of DNS cache poisoning attacks.
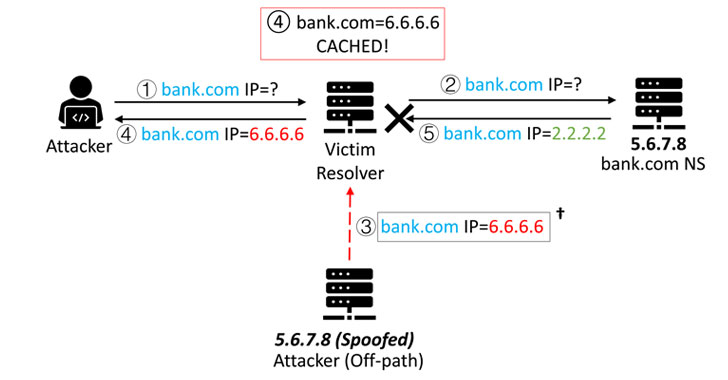
Dubbed “Unhappy DNS attack” (quick for Facet-channel AttackeD DNS), the system tends to make it possible for a malicious actor to have out an off-route attack, rerouting any site visitors at first destined to a particular area to a server below their manage, thereby letting them to eavesdrop and tamper with the communications.
“This signifies an crucial milestone — the 1st weaponizable network facet channel attack that has severe security impacts,” the researchers stated. “The attack enables an off-route attacker to inject a destructive DNS document into a DNS cache.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tracked as CVE-2020-25705, the conclusions have been introduced at the ACM Conference on Computer system, and Communications Security (CCS ’20) held this week.
The flaw impacts running systems Linux 3.18-5.10, Windows Server 2019 (edition 1809) and more recent, macOS 10.15 and newer, and FreeBSD 12.1. and more recent.
DNS Forwarders Develop into New Attack Area
DNS resolvers typically cache responses to IP address queries for a certain time period as a signifies to improve reaction functionality in a network. But this extremely system can be exploited to poison the caches by impersonating the IP tackle DNS entries for a provided internet site and redirect consumers trying to take a look at that internet site to another web site of the attacker’s preference.
Nevertheless, the effectiveness of such attacks has taken a strike in section because of to protocols these types of as DNSSEC (Domain Identify Procedure Security Extensions) that results in a secure area title method by including cryptographic signatures to present DNS records and randomization-based mostly defenses that let the DNS resolver to use a distinctive supply port and transaction ID (TxID) for each individual question.
Noting that the two mitigation measures are even now significantly from staying extensively deployed owing to “incentives and compatibility” reasons, the researchers claimed they devised a side-channel attack that can be efficiently employed from the most preferred DNS software stacks, therefore rendering community DNS resolvers like Cloudflare’s 1.1.1.1 and Google’s 8.8.8.8 susceptible.
A Novel Aspect-Channel Attack
The Sad DNS attack performs by generating use of a compromised machine in any network which is capable of triggering a ask for out of a DNS forwarder or resolver, these kinds of as a public wireless network managed by a wireless router in a espresso store, a shopping mall, or an airport.
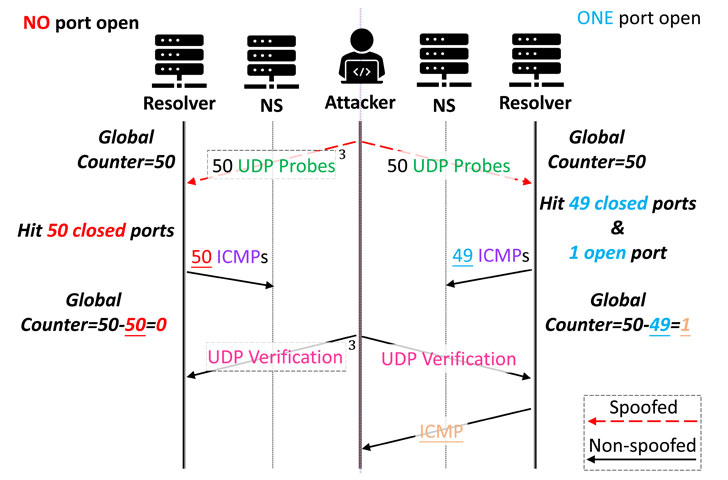
It then leverages a facet channel in the network protocol stack to scan and find which source ports are utilized to initiate a DNS question and subsequently inject a big quantity of spoofed DNS replies by brute-forcing the TxIDs.
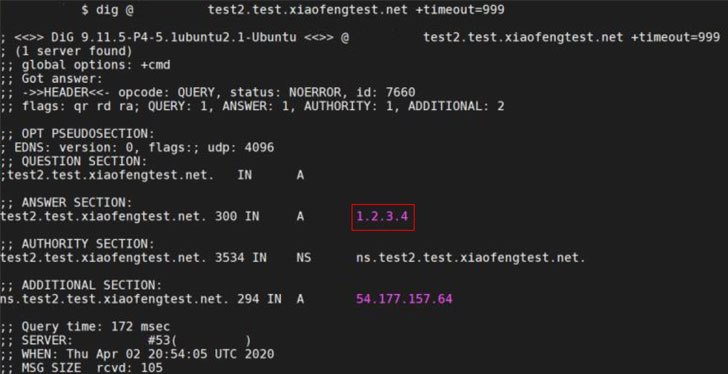
A lot more precisely, the scientists applied a channel employed in the domain name requests to slender down the specific source port variety by sending spoofed UDP packets, just about every with distinctive IP addresses, to a target server and infer regardless of whether the spoofed probes have hit the correct source port based on the ICMP responses gained (or lack thereof).
This port scan strategy achieves a scanning pace of 1,000 ports for every 2nd, cumulatively getting a minor about 60 seconds to enumerate the total port array consisting of 65536 ports. With the resource port thus derandomized, all an attacker has to do is to insert a malicious IP handle to redirect web page visitors and efficiently pull off a DNS cache poisoning attack.
Mitigating Unfortunate DNS Attacks
Apart from demonstrating means to increase the attack window that permits an attacker to scan more ports and also inject supplemental rogue data to poison the DNS cache, the research discovered that about 34% of the open up resolvers on the Internet are susceptible, 85% of which comprise of well-liked DNS solutions like Google and Cloudflare.
To counter Sad DNS, the researchers propose disabling outgoing ICMP responses and setting the timeout of DNS queries extra aggressively.
The researchers have also place collectively a resource to examine for DNS servers that are vulnerable to this attack. In addition, the team labored with the Linux kernel security crew for a patch that randomizes the ICMP world-wide level limit to introduce noises to the facet channel.
The investigation “offers a novel and normal aspect channel based on [the] world-wide ICMP fee limit, universally implemented by all contemporary working programs,” the researchers concluded. “This will allow successful scans of UDP supply ports in DNS queries. Merged with techniques to prolong the attack window, it sales opportunities to a strong revival of the DNS cache poisoning attack.”
Discovered this posting intriguing? Observe THN on Fb, Twitter and LinkedIn to browse more exclusive information we write-up.
Some elements of this posting are sourced from:
thehackernews.com

 Attackers target gaming as the latest ‘always on’ industry impacted by ransomware
Attackers target gaming as the latest ‘always on’ industry impacted by ransomware