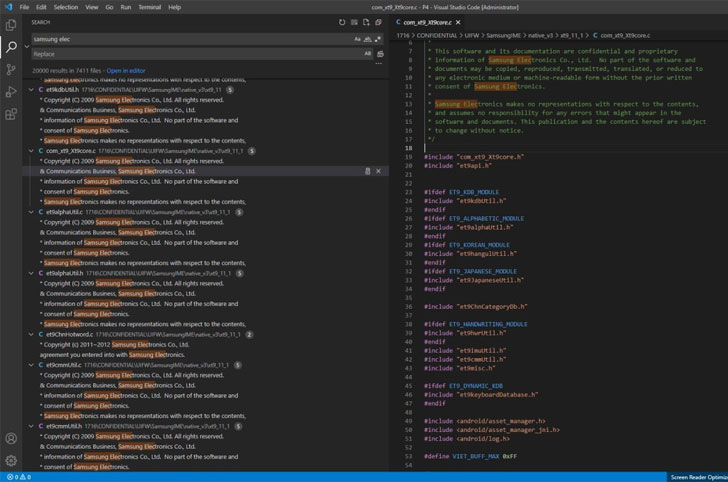
Samsung on Monday verified a security breach that resulted in the exposure of internal business info, together with the source code related to its Galaxy smartphones.
“In accordance to our first examination, the breach entails some supply code relating to the procedure of Galaxy units, but does not involve the personalized data of our shoppers or workforce,” the electronics giant instructed Bloomberg.
The South Korean chaebol also confirmed that it does not foresee any impact to its small business or its prospects as a result of the incident and that it has executed new security measures to reduce this kind of breaches in the long run.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The affirmation arrives soon after the LAPSUS$ hacking group dumped 190GB of Samsung details on its Telegram channel in direction of the finish of very last week, allegedly exposing the supply code for dependable applets put in inside TrustZone, algorithms for biometric authentication, bootloaders for current devices, and even private data from its chip supplier Qualcomm.
The information of the leak was 1st documented by Bleeping Pc on March 4, 2022.
If the identify LAPSUS$ rings familiar, it is really the identical extortionist gang that manufactured absent a 1TB trove of proprietary information from NVIDIA past month, particularly personnel credentials, schematics, driver resource code, and information pertaining to the new graphics chips
The team, which initially emerged in late December 2021, also positioned an abnormal desire urging the company to open-resource its GPU motorists for good and eliminate its Ethereum cryptocurrency mining cap from all NVIDIA 30-collection GPUs to stop additional leaks.
It is really not right away very clear if LAPSUS$ has designed any very similar calls for to Samsung before publishing the details.
The fallout from the NVIDIA leaks has also led to the release of “in excess of 70,000 worker email addresses and NTLM password hashes, quite a few of which have been subsequently cracked and circulated within just the hacking group.”
That’s not all. Two code-signing certificates involved in cache dump from NVIDIA have been utilised to indication destructive Windows motorists and other equipment typically utilized by hacking crews, specifically Cobalt Strike beacons, Mimikatz, and other remote accessibility trojans.
“Threat actors began on 1st March, a day immediately after torrent [was] posted,” security researcher Kevin Beaumont mentioned in a tweet past week.
Uncovered this posting appealing? Stick to THN on Fb, Twitter and LinkedIn to examine additional exceptional content material we submit.
Some sections of this posting are sourced from:
thehackernews.com



 Scores of US Critical Infrastructure Firms Hit by Ransomware
Scores of US Critical Infrastructure Firms Hit by Ransomware