Pictured: Reporter Bradley Barth’s score following having a phishing quiz from GreatHorn and Encouraged eLearning.
There is a particular sum of force that comes with staying a security reporter and agreeing to get scored on a phishing exam for all to see.
Granted, in actual lifetime, you under no circumstances know when you are getting tested by real-lifetime cybercriminals striving to get you to click on a website link or open an attachment. That can happen any time. But it was yet reassuring to study that I scored a nine out of 10 soon after remaining quizzed on regardless of whether a sample email was or wasn’t a phishing endeavor.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Devised by email security enterprise GreatHorn and security awareness organization Inspired eLearning, the quiz was taken by 1,123 U.S. users in September 2020. And which is wherever the negative information comes in: Most check-takers fared a great deal even worse. In accordance to GreatHorn’s 2020 Conclude Consumer Phishing Report, the normal take a look at score was 52 p.c. “So slightly superior than a coin flip,” explained GreatHorn founder and CEO Kevin O’Brien, in an interview with SC Media.
O’Brien walked as a result of the 10 email samples, detailing what clues examination-takers should really have picked up on, including a couple of that even my have keen editorial eyes skipped. Really feel free of charge to participate in together.
According to the CEO, the phishes were lifted instantly from real illustrations. “We procedure an regular of a bit over a billion e-mails on a heavier month… so what that indicates is that we have obtain to just an great amount of true info,” claimed O’Brien. “So we did draw from actual phish, primarily based on what we have witnessed.”
Let’s get the embarrassing component out of the way and begin with the problem that tripped me up.
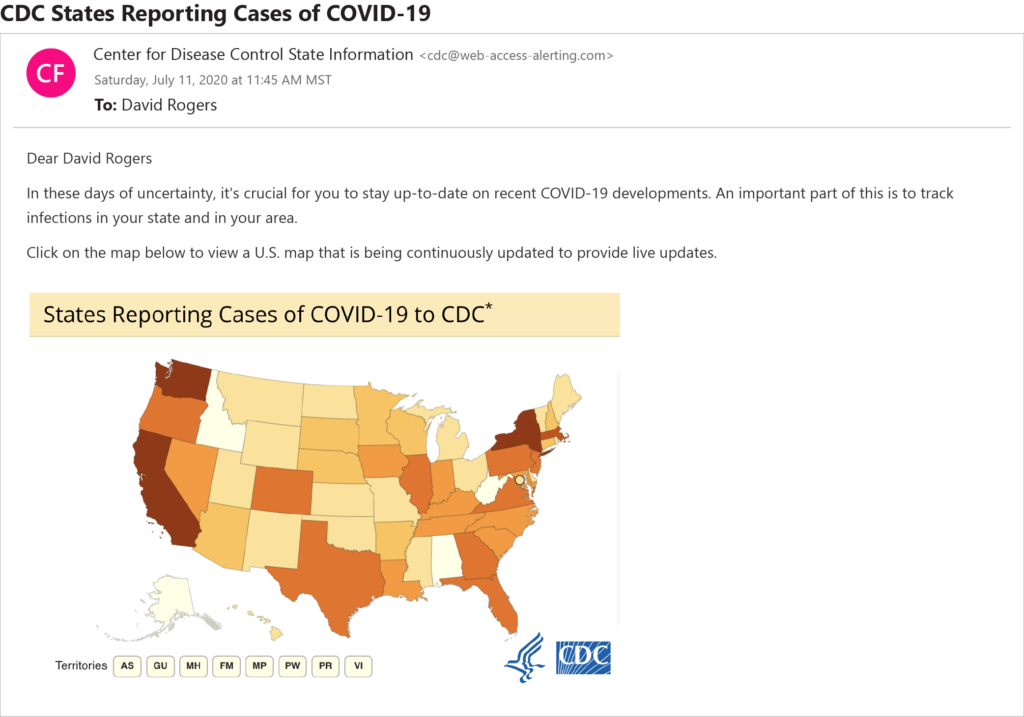
Initial, a disclaimer: I know there have been tons of COVID-19 frauds due to the fact the pandemic swept throughout the planet. And I individually would hardly ever open up an unsolicited email that supposedly comes from the CDC and encourages me to click on a map for the most modern coronavirus developments. But the above email legitimately looked as if could have come from the company, and I couldn’t obtain anything mistaken with it. I wondered if probably GreatHorn was attempting to throw me a curveball by exhibiting me a authentic CDC email.
It wasn’t. It was a fraud. And I skipped a essential, delicate clue: “The only point that should really issue out to you that it was not correct is the return route,” claimed O’Brien. In truth, the sender’s email area appeared as [email protected][.]com. “The CDC [sends] e-mail from cdc.gov,” the CEO noted.
“You’re producing for SC. You observe security. You publish about phishing, and you are having a phishing exam. So you’re previously wondering about, ‘Well could this be or couldn’t it be?’” O’Brien mentioned to me. “You experienced all the ideal concerns in brain – and you fell for it. That is not abnormal.”
In actuality, nearly 52 of respondents incorrectly guessed that this was not a phishing email.
I was kicking myself for receiving it wrong, spoiling what could have been a great rating, but O’Brien was additional forgiving. “That’s not one particular that’s riddled with spelling problems and grammatical problems. It was effectively-written. And it is extremely persuasive,” he stated.
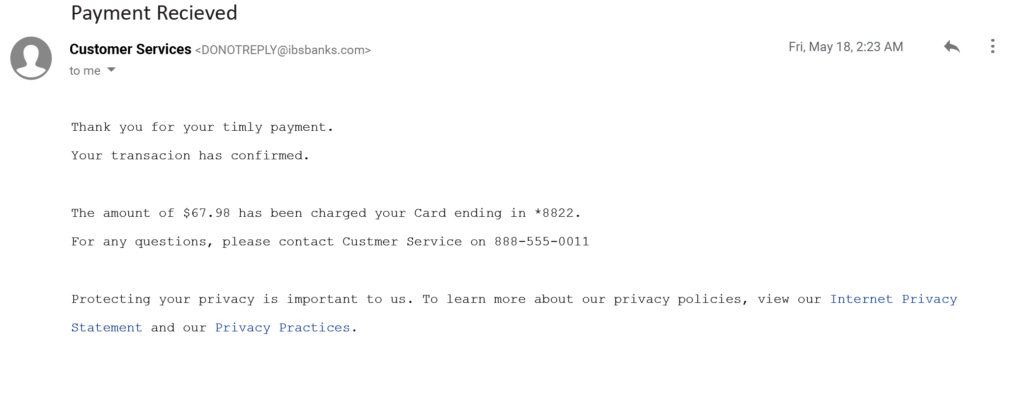
On the other hand, some phishes ended up so riddled with goofs, they were really easy to place, Like this email, purportedly from a bank, that reported “Thank you for your timly payment. Your transacion has confirmed.”
Then once again, maybe it wasn’t so uncomplicated: only about 51 p.c of examination takers labeled it a phish.
“That was a actually obvious illustration of what really should seem like phish,” claimed O’Brien. And nevertheless, “people did not do a excellent task of catching it.”
The purpose: “Our brains are wired to proper faults in the things that we see and browse,” stated O’Brien. In genuine lifestyle, perhaps even less people would have caught it, for the reason that many employees are chaotic and distracted, or see an email about economical matters, which triggers a panicked reply with out initial halting to feel.
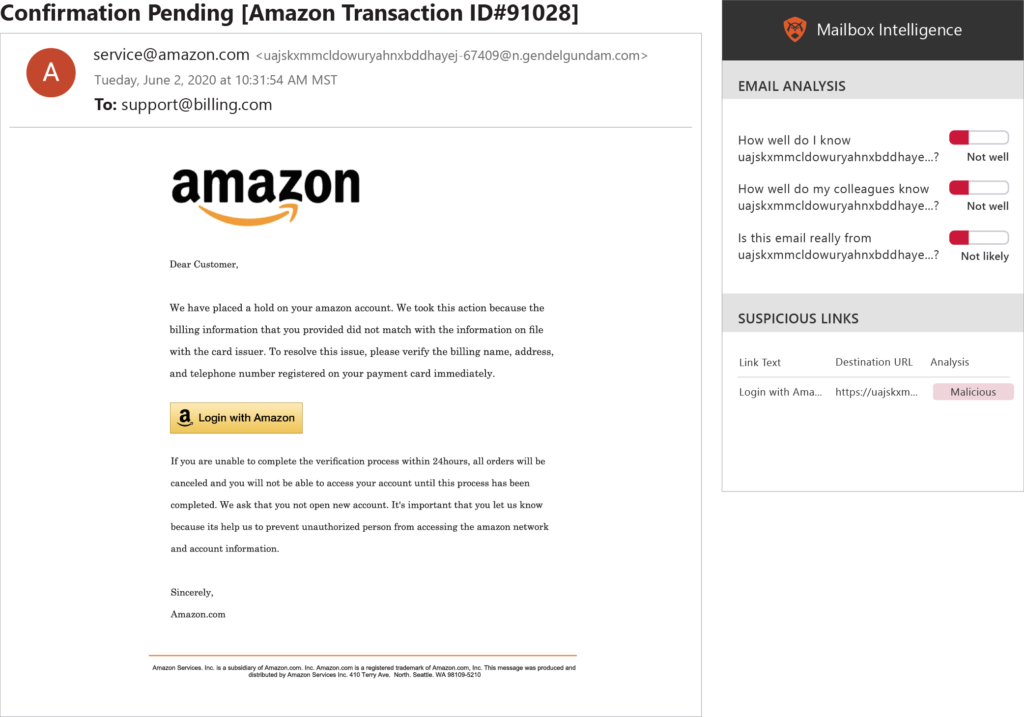
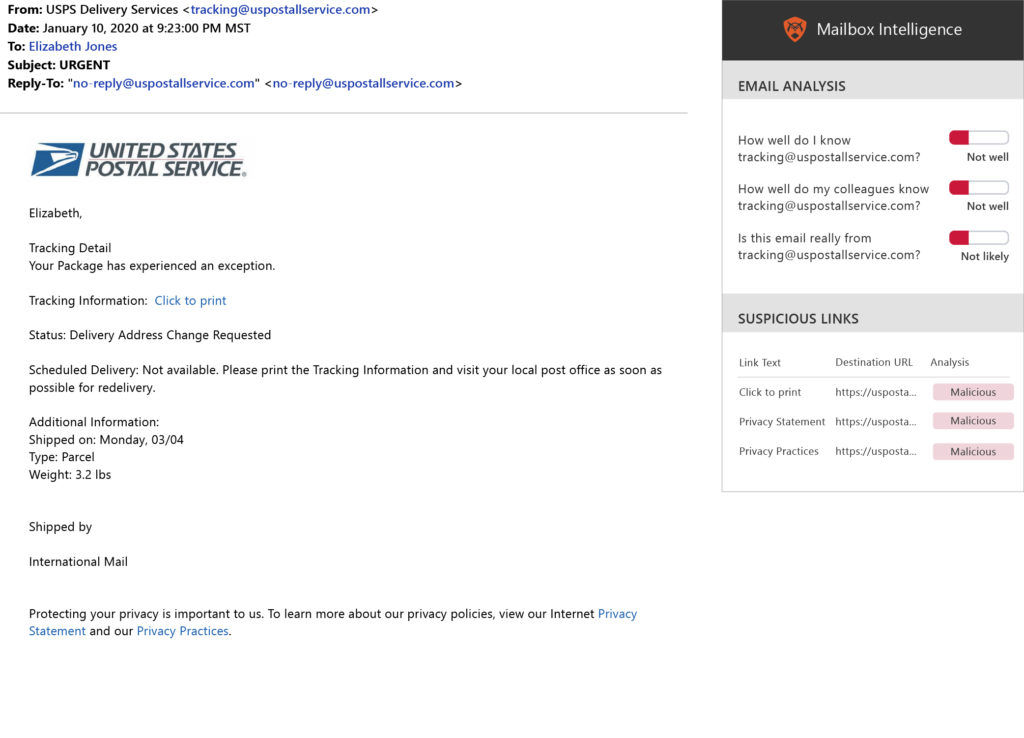
Even with whiffing on the CDC email, I was at least ready to location a several other suspicious envelope sender addresses that tipped me off to a phish, like a bogus Amazon return route that featured a nuts, long string of letters and numbers, and a U.S. postal support address that I assumed should have ended in usps.gov but was as an alternative suspiciously shown as [email protected][.]com. (I am ashamed to confess I didn’t even recognize the additional “l” in the address until O’Brien pointed it out).
The postal provider a single is specifically fascinating due to the fact it encapsulates a typical issue: cell customers are less most likely to location a phish than desktop consumers. This is owing to components like monitor size and also simply because mobile gadgets are “increasingly applied for quick actions to scroll and click on, versus the far more centered steps taken on desktop use,” the report states. In genuine-existence phishing situations, a further trouble is that email shoppers for cellular gadgets normally really don’t demonstrate the total deal with of a sender, O’Brien included.
In the USPS case, 71 p.c of desktop end users properly named it a phishing email, whilst only 58 % of mobile customers gave the appropriate answer – a 13 share point variation. On top of that, cell users scored 13 proportion points worse than desktop people across the comprehensive questionnaire.
Meanwhile, the Amazon email turned out to be a person of the less difficult concerns: 75 % of respondents identified it as a phish. “The major clue for me is you see this large Amazon symbol,” O’Brien mentioned, which is a tactic that phishing scammers normally use to make the receiver “feel cozy.” Having said that, in this instance, the symbol is abnormally substantial, not to point out the inconsistent capitalization of Amazon in the body of the textual content.
In standard faux email messages from ubiquitous and well-known makes such as Amazon had been on regular extra probable to be discovered as phishing tries in the take a look at, “showing that people are understanding to have a more critical eye toward emails from trustworthy makes,” the GreatHorn report said.
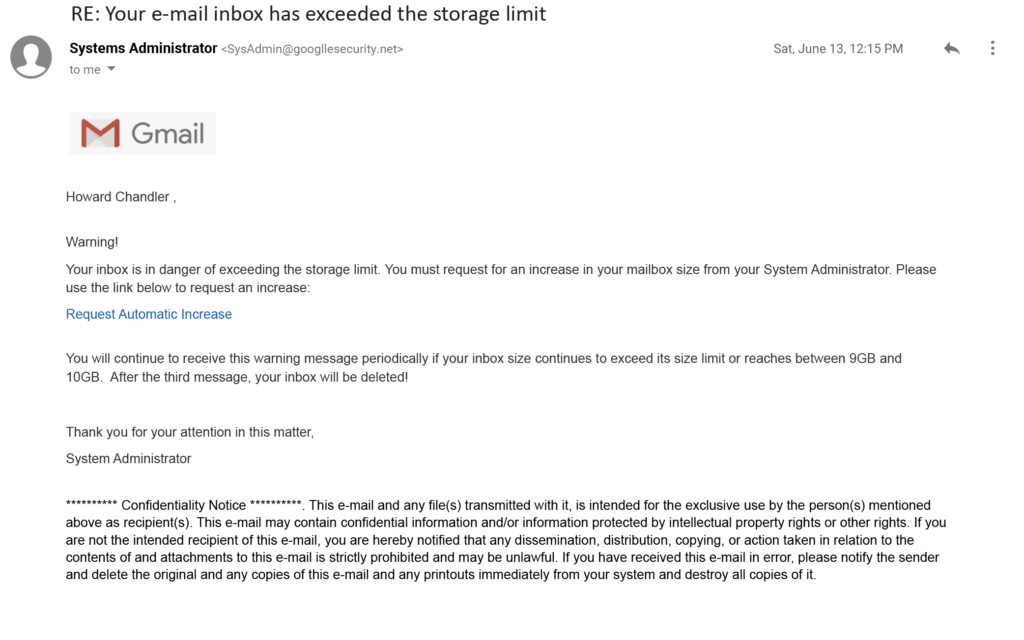
Situation in level: a little the vast majority of 66 percent discovered the earlier mentioned Google-themed email as a phish. Like the postal support email, it includes an excess “l” in the sender’s address (Googlle.com). In addition, its language was unusually alarmist and was signed, dubiously, by an nameless “systems administrator.”
“Cybercriminals frequently use ‘Systems Administrator’ or ‘Service’ in their phishing email messages, seeking to disguise their tried attacks as standard program warnings,” the report states.
“This one’s effortless mode,” stated O’Brien, also noting the incorrect spacing immediately after the salutation. “It’s an obviously, ridiculously faux information.”
And but, “people nevertheless tumble for it.” Roughly 34 % ended up fooled.
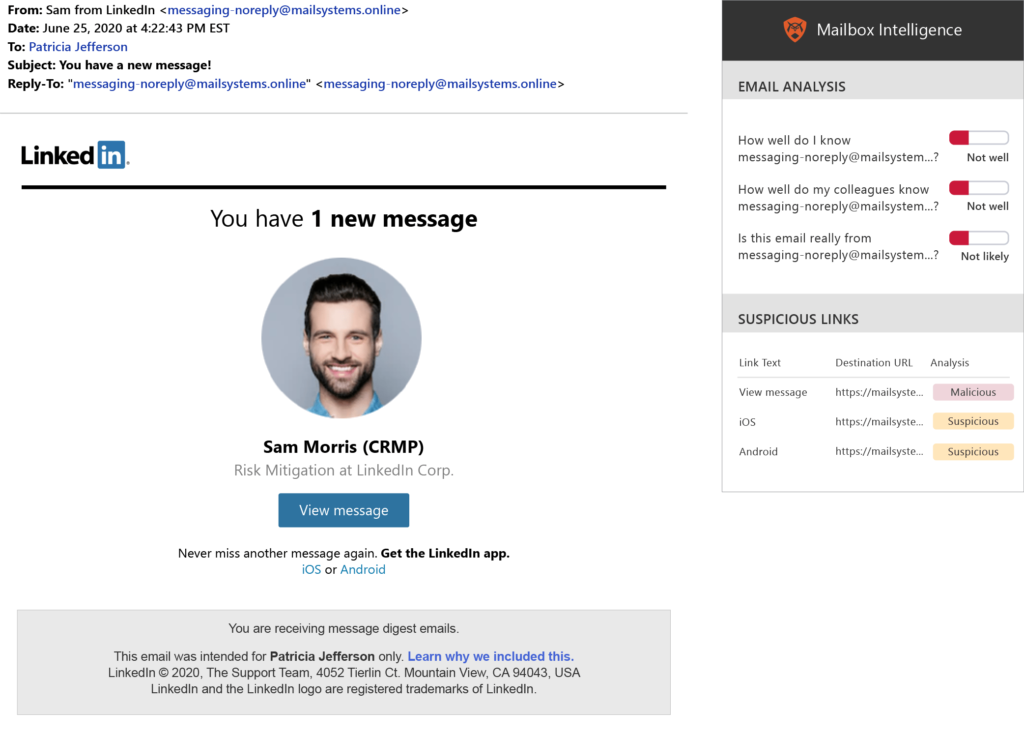
GreatHorn also quizzed test-takers with a LinkedIn email notifying the user of a concept from a LinkedIn Licensed Risk Administration Experienced. “The return route area is not what it must be, but it’s obtained all of the hallmarks of how these brand impersonations do the job,” reported O’Brien. “The logo’s there, the colors are suitable, it’s not ‘system administrator,’ and you probably get occasional e-mail from LinkedIn that looks sort of like this. So yeah, uncomplicated to get tricked.” Indeed, 41 per cent were being fooled and thought it was genuine, even even though LinkedIn “does not send out mail like this,” O’Brien added.
Among the categories of email that induced the most confusion ended up individuals linked with respectable organization solutions particularly, Confluence, Dropbox and Microsoft Groups.
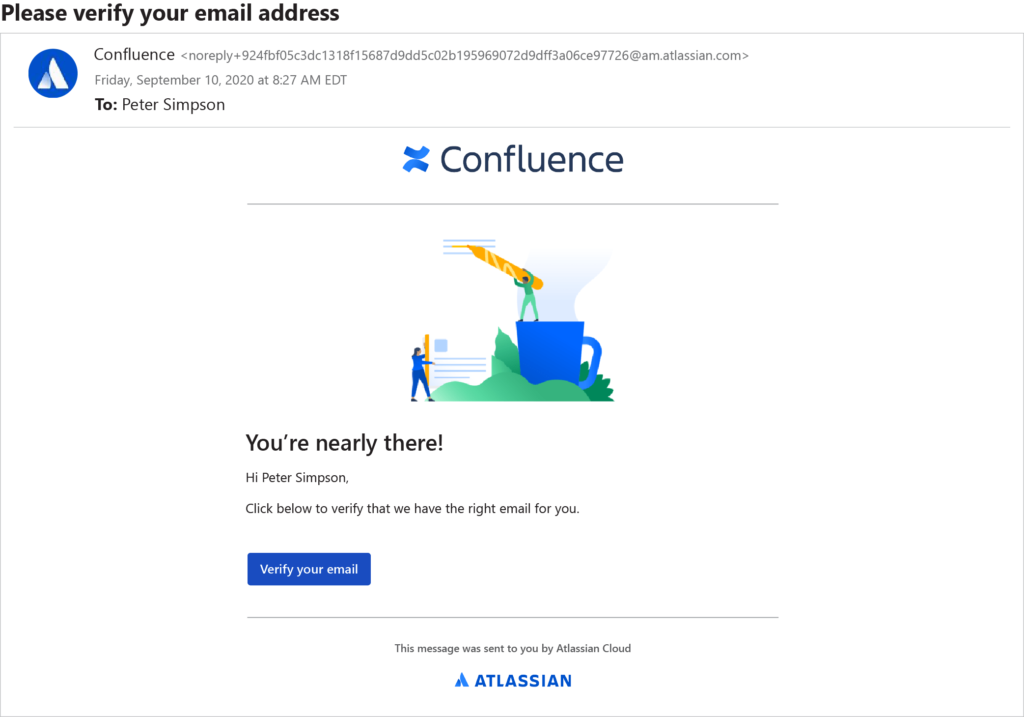
The Confluence email seemed to me like a verification email that I would usually acquire if I were being to indication up for the collaborative workspace services from Atlassian. Assuming that in this I did in fact indicator up, I the right way deduced that the email was legit. (If not, why would I hassle to open up up the email in the initial area?)
“Your instinct is suitable,” explained O’Brien. Nevertheless, a whopping 71 p.c wrongly thought it was a phishing attack. The difficulty, he stated, is that often staff obtain this specific form of email and mistakenly think it is a phish for the reason that their employer had established them up on the support without alerting them to start with. So the staff disregard the email, which results in productivity lapses.
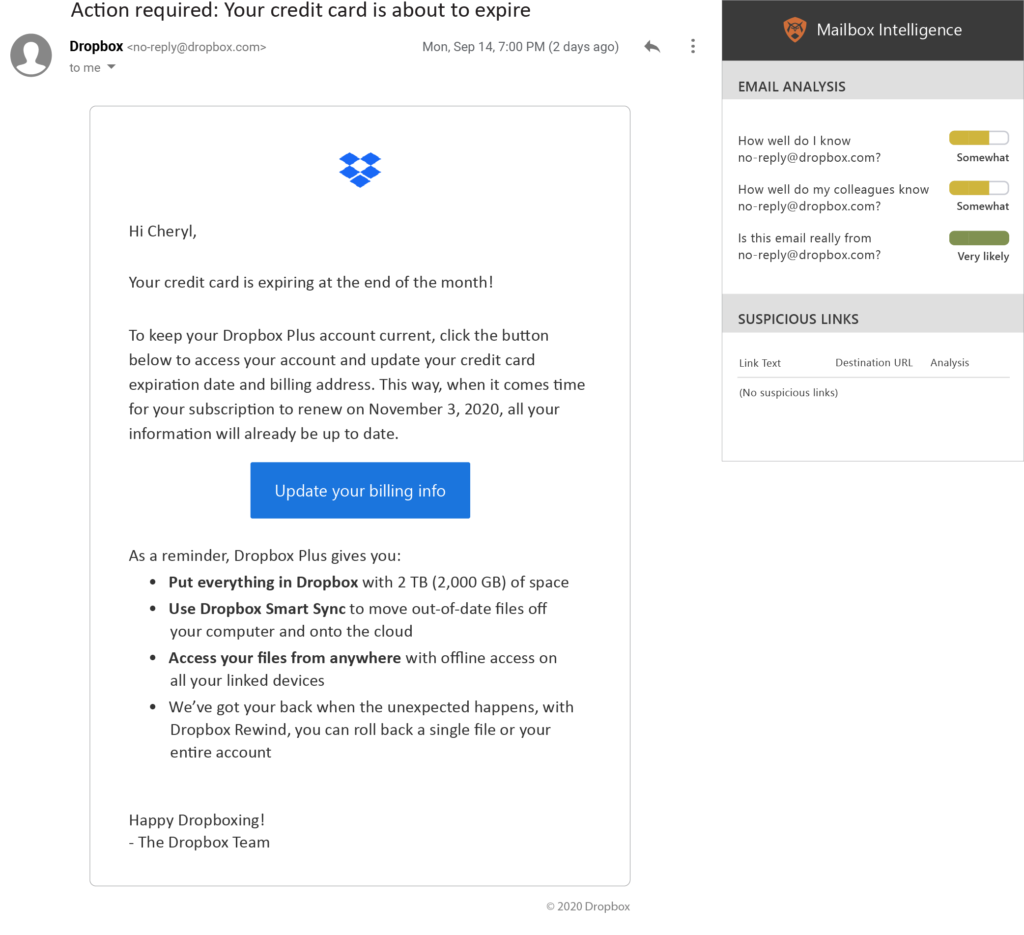
A identical legit email that threw off test-takers was the earlier mentioned Dropbox communication – 55 p.c considered it was a phish, when it was basically authentic. Yet again, in a case like this, failure to answer has its penalties – the user’s credit score card will expire if motion is not taken.
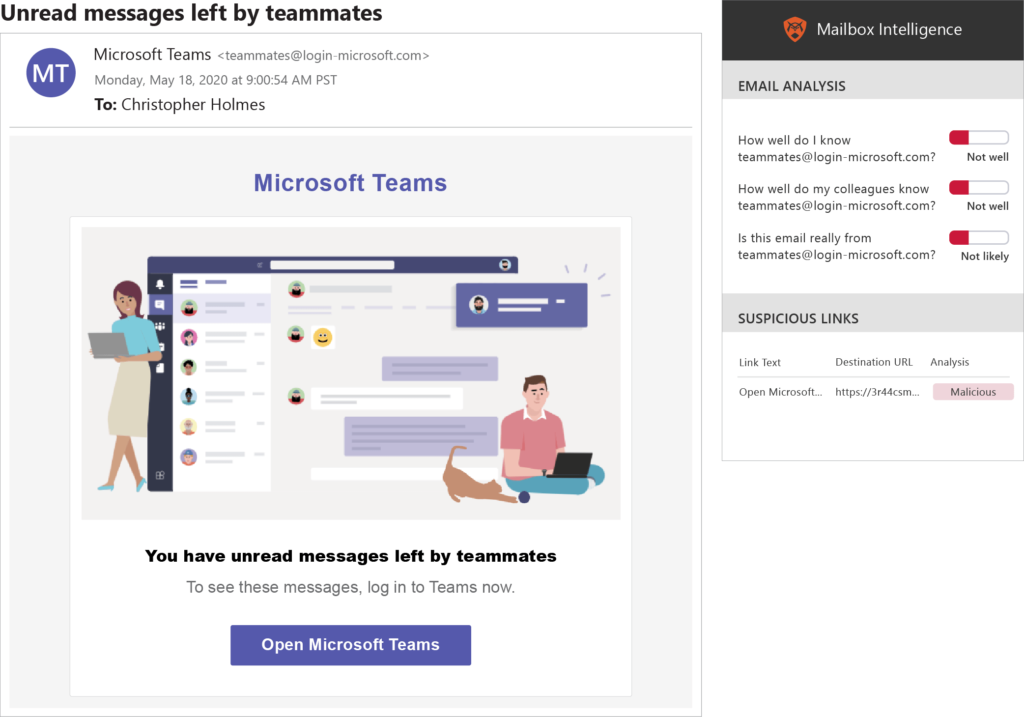
On the other hand, the higher than Microsoft Teams case in point is a phish – one particular that fooled 53 percent of the exam-takers. While the email appears to be like skillfully created, Microsoft does not use the handle [email protected] to mail these communications about unread messages. And even though buyers can look for on the web to see if a sender’s tackle is legit or not, “the chance that an end user is heading to do that is zero,” said O’Brien.
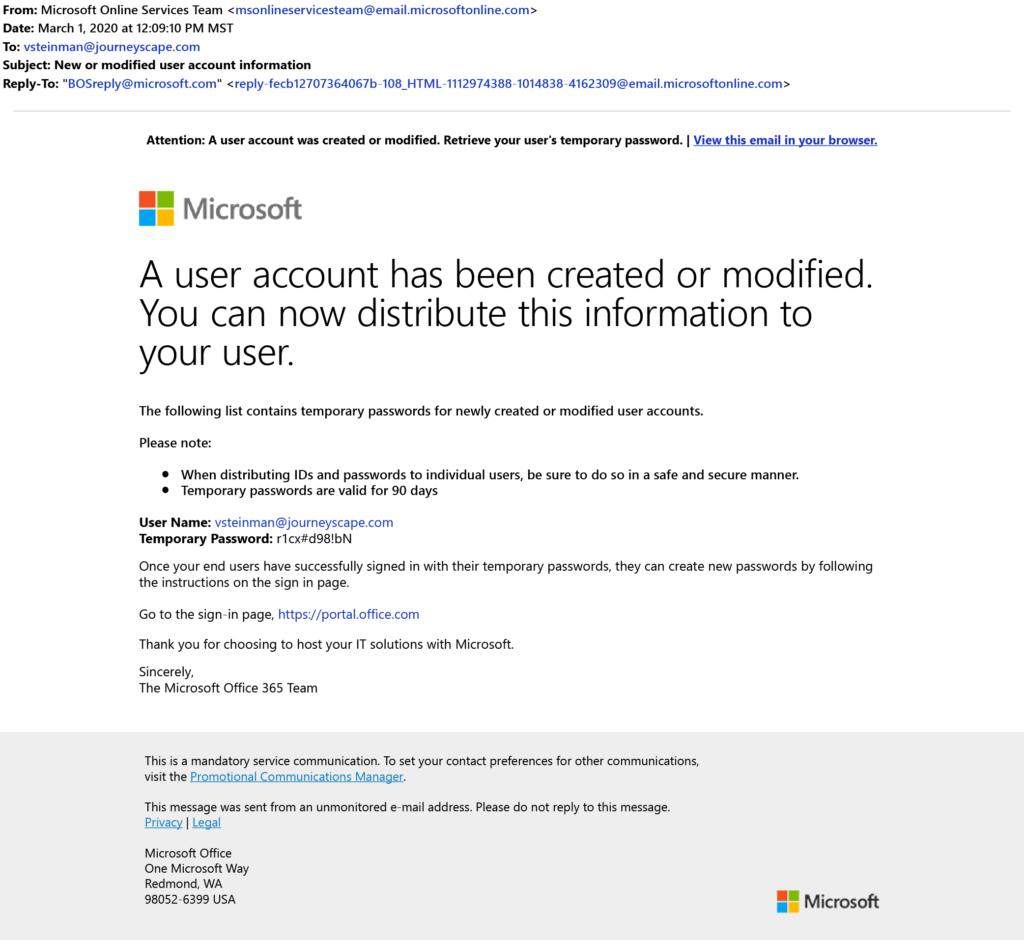
There was a second Microsoft email on the check – an Workplace 365 a person that contains a password for a freshly made or modified account. Respondents have been evenly split, with 50.4 per cent properly guessing it was a authentic email, though 49.6 percent mistook it as a phish. “And it definitely highlights just how terrible authentic mail is,” claimed O’Brien. “Email is not a tremendous secure medium, and aspect of why is that even with authentic messages, you’re like, ‘I don’t know.’”
For sure inquiries, the check randomly gave end users extra valuable context by incorporating an graphic from GreatHorn’s Mailbox Intelligence plugin device, which suggests familiarity with the sender’s email handle, the chance that the email is essentially from the sender, and the presence of suspicious inbound links.
Simply by trusting the tool’s suggestions, take a look at takers could have answered those people questions appropriately. On typical, the device gave buyers a 10 percent greater possibility of precisely guessing if an email was a phish or not. And had these people today actually been properly trained to use and recognize the instrument, the scores would have been even better, mentioned O’Brien.
Surely, workforce can use all the assist they can get. No one’s great – not even this reporter, as my 90 per cent score proves. And in real everyday living it only usually takes one incorrect guess to give you and your business a a lot even bigger issue than a tiny pop quiz anxiety.
Some parts of this report are sourced from:
www.scmagazine.com


 URL address spoofing flaw keeps victims from determining fake, real sites
URL address spoofing flaw keeps victims from determining fake, real sites