Watch Post
Editor’s Take note: This set of evaluations originally appeared in June 2020. To find out a lot more about SC Labs, get in touch with Adrian Sanabria at [email protected]
This thirty day period, SC Labs assessed a number of identification and entry management methods. This evaluation will come at a relevant time with the recent functions bordering COVID-19 and the worldwide change to performing from home. The standard, known perimeter has grown ever more immaterial around the decades. The unprecedented, entire world-huge scramble to do the job remotely has emphasized that the earlier recognised perimeter is just about non-existent.
These making an attempt times have mercilessly highlighted a amount of cybersecurity weaknesses throughout industries. It is our honest hope that these evaluations find our readers in a point out of proactive owing diligence in its place of a article-incident scramble pursuing a lesson learned the difficult way. The identity and accessibility administration alternatives reviewed here guard the proverbial gates of critical corporation methods, examining the IDs of absolutely everyone that attempts to enter, making sure identities match close-user claims and privileged access is adequate for entry. Without having this cybersecurity bouncer to guard the doorway to your assets, malicious actors have a free move into critical apps and details.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Products Team Opener
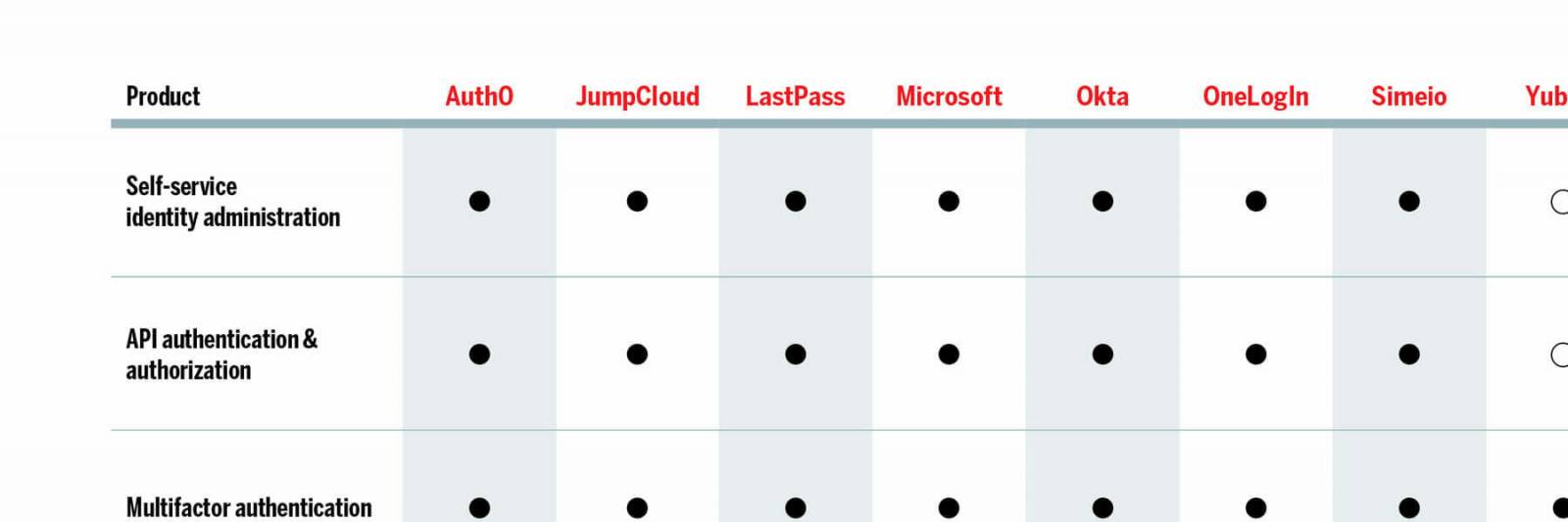
This month, SC Labs looked at a handful of items in the identification and obtain administration (IAM) house, which collectively purpose as an organization gateway in between end-end users and critical group data with centralized obtain management of cloud, on-premises and legacy applications and sources. The emphasis below is on the word collectively. Although these alternatives approximately solely provide main abilities these types of as authentication and authorization, the merchandise we assessed are most effective when deployed along with at least a person other IAM solution. Various of these items already have constructed-in integration to assistance one another.
Onboarding customers onto the system, in most circumstances, is automated with a wide vary of directory integrations. Bisynchronous interactions among the id system and supported directories requires the guide operate practically entirely out of the fingers of directors and dramatically reduces the complexity of implementation and time-to-worth.
Some of this month’s goods may run on the frontend with MSSP operation when a paired id and access management remedy operates in the backend. This particular use case and sort of deployment allows a seamless change involving IAM options devoid of the want to retrain stop-buyers. A third type of product or service, YubiKey (hardware), can insert an more layer of id security operating as a critical to the backend identity and entry management lock.
We see the industrywide trend of incorporating synthetic intelligence and machine mastering with identity methods as perfectly. State-of-the-art attributes these as user habits assessment allow dynamic assessments of, and responses to, various risk at the user or session degree. A baseline comprehending of anticipated consumer actions (time of working day, IP tackle, area, and so forth.) enables the flagging of anomalous behavior.
Identity and obtain management products and solutions increase common login qualifications with several security capabilities such as password management and analysis, single indicator-on and multifactor authentication. Some of the answers have password vaults so that close buyers may securely retail outlet organization qualifications. Password management keeps tabs on the frequency with which passwords are reused and the inherent security of those passwords according to length and complexity. One indicator-on streamlines application and useful resource entry serving as a central, unified login portal. This encourages stop customers to use prolonged and advanced passwords because only require to indicator in as soon as to entry all an organization’s assets in its place of getting to log into just about every one personal resource. Some products and solutions even permit authentication at the workstation amount.
Identity and access administration items are critical to enterprise security across industries and considerably increase existing security investments. In addition to bringing in an further layer of security and heading a phase farther with knowledge decline avoidance, their capabilities and options can improve productivity and over-all return on financial investment.
Pick of the Litter
Yubico YubiKey 5Ci presents the most straightforward and maximum stage of security offered for an identification answer that is so customer pleasant. If there ended up an simplicity-of-use class, this would win by a mile. The a person-contact YubiKey knowledge comes with a substantial ecosystem of integrations, a low whole price of ownership, and a considerable return on financial commitment, earning Yubico YubiKey an SC Labs Finest Acquire.
Okta Identification Cloud is a flexible resolution with an in depth integration network that addresses every identification use case for any technology. Okta reliably and proficiently improves productiveness and security, driving profitability and progress to optimize overall return on financial investment and to minimize the overall value of possession, generating this our SC Labs Advised solution for this month’s spherical of tests.
June critiques
Auth0
JumpCloud
LogMeIn LastPass Identity
Microsoft Azure Energetic Directory (Azure Advert)
Okta Id Cloud
OneLogIn Reliable Practical experience System (TEP)
Simeio Id Orchestrator
Yubico YubiKey 5Ci
Simply click on the chart beneath for the total-dimension variation
Some areas of this write-up are sourced from:
www.scmagazine.com

 Hackers target gamers with a supply-chain attack
Hackers target gamers with a supply-chain attack