A Microsoft creating in Europe. (efes, CC0, through Wikimedia Commons)
A not too long ago found phishing scam that convincingly impersonates the Microsoft Windows symbol with an HTML table serves as a new reminder of how social engineers can abuse several elements in e-mail to idiot both human recipients and particular security methods.
The plan first started to emerge late final yr into January and entails utilizing a desk to create a 2×2 grid of cells, and then filling them in with colours to make the desk glimpse just like the iconic Windows symbol. The existence of this fraudulent, nevertheless reliable-hunting emblem lends excess credibility to phishing email messages, and according to Inky they can fool some conventional Safe Email Gateways that are likely to overlook the presence of tables as a suspicious component.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“This new tactic most possible originated in a one phishing package and is now adopted in several kits,” reported Bukar Alibe, cyber security analyst at Inky.
Although this certain rip-off may possibly be new, it’s just the hottest phishing tactic to integrate HTML tables. For occasion, “previously HTML tables ended up abused by using mixtures of black and white cells to develop graphics that appear like URLs. This is no more time used for the reason that it appears to be like visually distinctive and suspicious when as opposed to a standard hyperlink,” explained Alibe pointed out.
Another connected strategy used to bypass textual content filters is to produce a table, erase all borders from it, configure it to bunch the various information cells together, and then increase parts of textual content to the specific cells to make it look like common text.
“Attackers… break up malicious phrases and area elements of the term in diverse adjacent cells,” reported Alibe. “For example, a bitcoin filter can be thwarted by putting ‘bi,’ ‘tco,’ and ‘in’ in diverse cells. This would make it readable for people and obfuscated for unsophisticated scanners.”
In this hottest marketing campaign, Inky observed a sequence of emails working with the faux Microsoft brand in an endeavor to get recipients to click on a destructive website link, open up a weaponized attachment or phone a rip-off phone quantity “where an evil operative tries to extract personalized and money info,” the report states.
Examples of these phishes involved a bogus new fax notification from SharePoint, showcasing a hyperlink that utilised an open redirect to choose victims to a compromised web advancement resource website, wherever destructive content material was injected into their computer system. Other lures incorporated a faux Office environment 365 email with a phone password expiration a phony voicemail notification. The attack mechanism, a malicious hyperlink, was concealed in an HTML attachment.
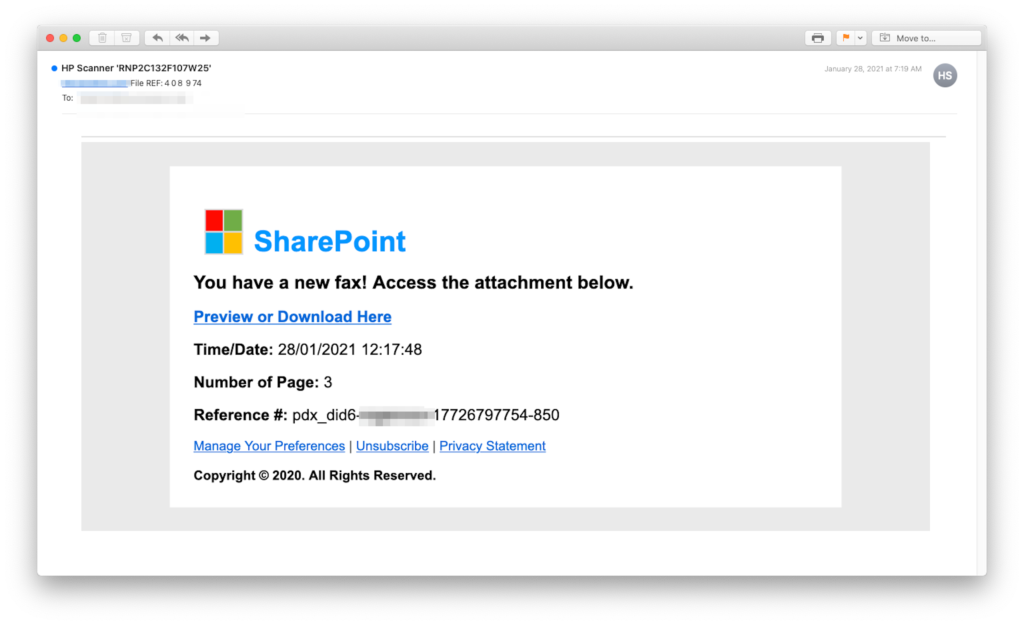 A SharePoint-themed phishing email featuring a bogus Windows brand.
A SharePoint-themed phishing email featuring a bogus Windows brand.
The campaign also leveraged other well-worn tactics, such as “open redirects, abused cloud web sites, booby trapped HTML attachments, hijacked email advertising marketing campaign equipment, and zero-font character stuffing.”
Roy Rotem, Avanan co-founder and head of details science, verified the presence of these fake Microsoft logo attacks, noting that “we’re commencing to see an raise this 12 months.”
“These attacks creatively use HTML and CSS to impersonate logos, models and far more,” Rotem discussed. “We see tons of obfuscation approaches against Workplace 365, and many of them are also prosperous in opposition to common, legacy email gateways. These attacks are appealing due to the fact you cannot depend on the HTML/CSS static investigation that standard alternatives use.”
Fortuitously, companies geared up with more innovative, contemporary email security methods – significantly those with machine studying and/or personal computer vision – ought to be able to recognize the faux brand and deflect this attack.
“In this scenario, a device would see an HTML desk, but computer system eyesight would floor that this supposed desk is hoping to be a Microsoft brand,” the report states. “With that awareness, the detection procedure can test to see irrespective of whether the sender seriously is Microsoft.”
Rotem described an efficient course of action to defend from this sort of obfuscation attacks: “render the HTML email body in a sandbox, and carry out impression analysis… and apply cognitive AI versions to come across similarities and impersonation attempts. By employing headless browsers, you can properly render the website page and implement AI image-recognition models to ascertain if there is any impersonation on the web site. This security layer is not just successful versus this certain attack, but against a huge range of obfuscation tries in the HTML of the email.”
Some sections of this post are sourced from:
www.scmagazine.com


 Click Studios says stop tweeting: Phishers track breach notification info to craft new lures
Click Studios says stop tweeting: Phishers track breach notification info to craft new lures