As software package source chain security will become far more and much more very important, security, DevSecOps, and DevOps teams are a lot more challenged than ever to create transparent believe in in the application they produce or use. In fact, in Gartner just lately posted 2022 cybersecurity predictions, not only do they foresee the ongoing expansion of attack surfaces in the near potential, they also record digital offer chain as a main climbing attack surface and a single of the major trends to observe in 2022.
Just after all, any computer software is only as secure as the weakest website link in its provide chain. A person bad element, any malicious accessibility to your development environment—or any vulnerability in your software’s shipping and delivery lifestyle cycle—and you risk your code’s integrity, your clients, and your status.
Scribe Security a short while ago introduced a new platform that claims to deal with these urgent needs by enabling its people to develop trust in their application across teams and businesses. According to Scribe Security, SBOM is a ideal observe that is predicted to turn out to be widely required and applied to mitigate program source chain risks. With that in intellect, they determined to acquire the direct and turn into the initially vendor to introduce the concept of a Hub for security evidence about software items and have released a friendly and simple-to-use system.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Our team not long ago explored Scribe’s platform in more depth.
Initial matters initially
Scribe’s platform: What you have to have to know before diving in:
- Cost-free and easy to use: Scribe’s system offers a finish self-provide experience. It is quick to put into action and use, as it is plugin and CLI-centered. And at last, you can start with a freemium, no strings attached.
- Software program security evidence hub: Though most other Program Supply Chain security remedies disregard the will need to make software program products’ security transparent to customers, customers, and security groups, Scribe, ‘s system introduces a hub for security evidence. As these types of, the system supports a workflow for sharing SBOMs throughout or in enterprises. A range of insights will quickly be included to the system so stakeholders will receive ongoing updates about the computer software they use. A person these types of insight, CVEs, is by now involved, making it possible for each the program producer and the people today they share their security insights with to see what CVEs are present in just about every new release. An fascinating experimental characteristic of the system is the capacity to validate program integrity and share that proof with stakeholders.
To facilitate this merchandise assessment, the workforce at Scribe Security gave us access to the most up-to-date variation of their platform. This is what we found:
Obtaining Begun
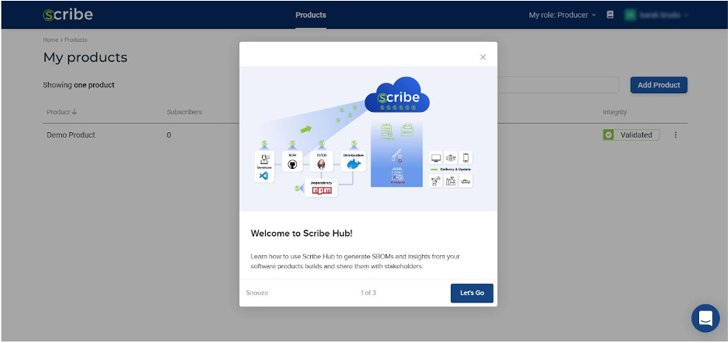
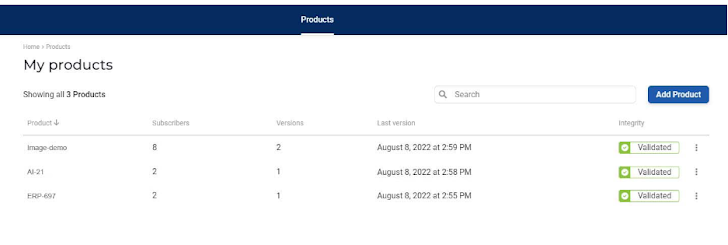
Using the Scribe platform, software producers can attain visibility into their pipelines and artifacts and choose software package consumers—subscribers—for just about every pipeline. Let us say I’m a software program producer interested in attempting the support. This is the initially display I see. Every aspect of the interface is described and illustrated.
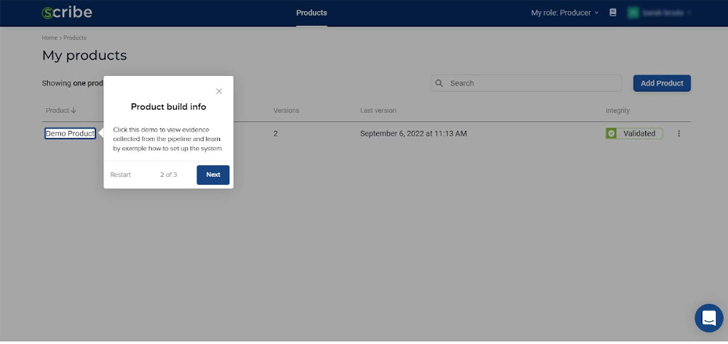
Observe that even when you 1st begin there is now a demo products you can use as an example of how the Scribe platform works. You can possibly play all around with the current demo solution or you can include a new product of your individual.
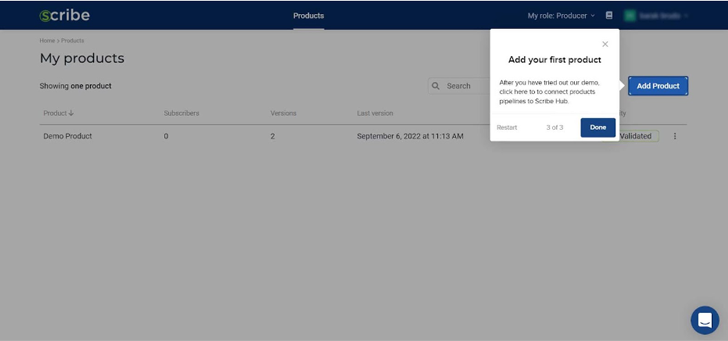
The highlighted ‘add product’ button on the top suitable enables you to insert new merchandise. For each new item, you’ll get the 3 needed strategies: Product Vital, Customer ID, and Client Key. You may also get a url to the integration rationalization of your option presently, you can decide on possibly GitHub, Jenkins, or a standard CI option. We are going to deal with that in more depth in a bit.
Utilizing this instance products, I can exam what the system can supply.
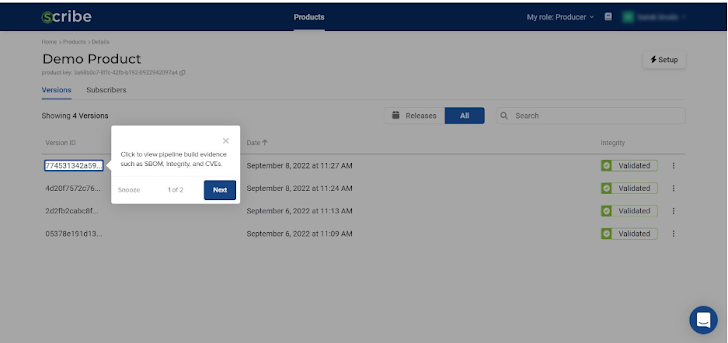
By clicking on it, I can see the product builds that have currently been uploaded. With the intention of screening out the platform’s interface, I started off with a person, and produced numerous additional immediately after.
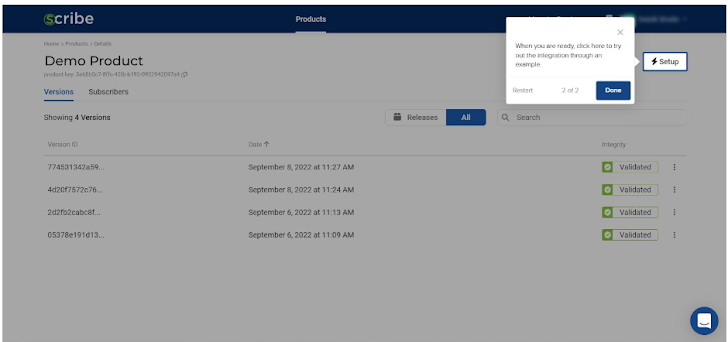
The highlighted ‘Setup’ button on the prime appropriate presents you accessibility to the present product information and facts.
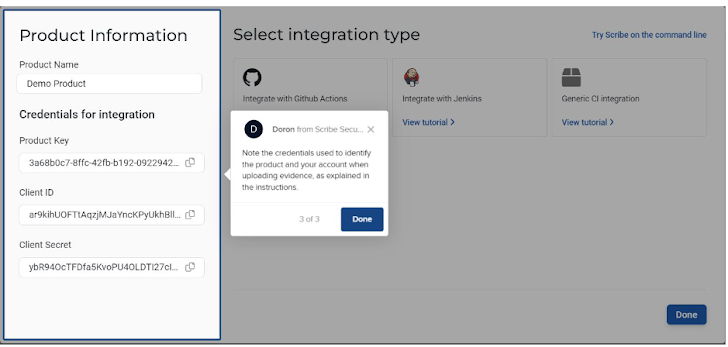
You can see the 3 product or service techniques, Item Important, Shopper ID, and Shopper Secret, just in situation you shed them or forgot them.
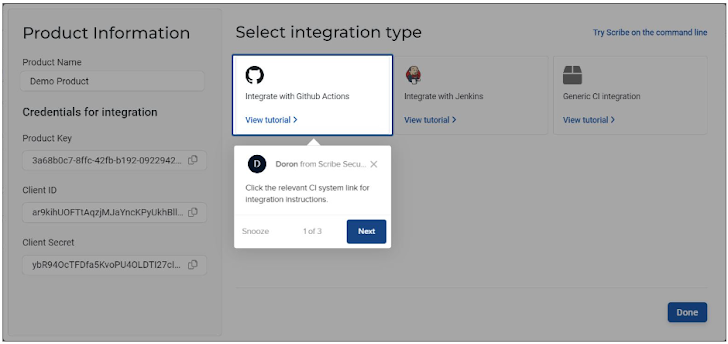
You also get obtain to the integration instructions, so if you altered your pipeline you can now see how to combine the Scribe instrument into your new pipeline.
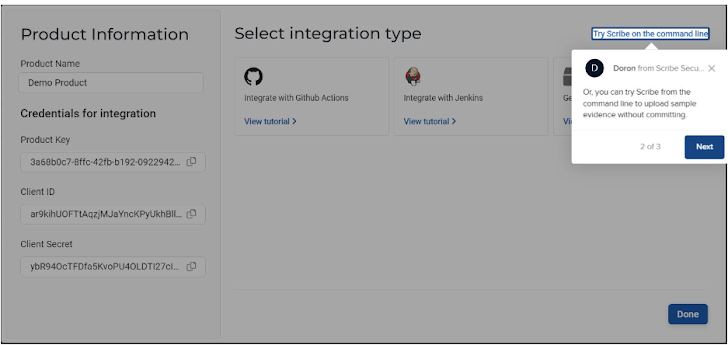
What caught my awareness was a hyperlink at the major proper stating ‘Try Scribe on the command line’, so I decided to click on on it to see what would take place.
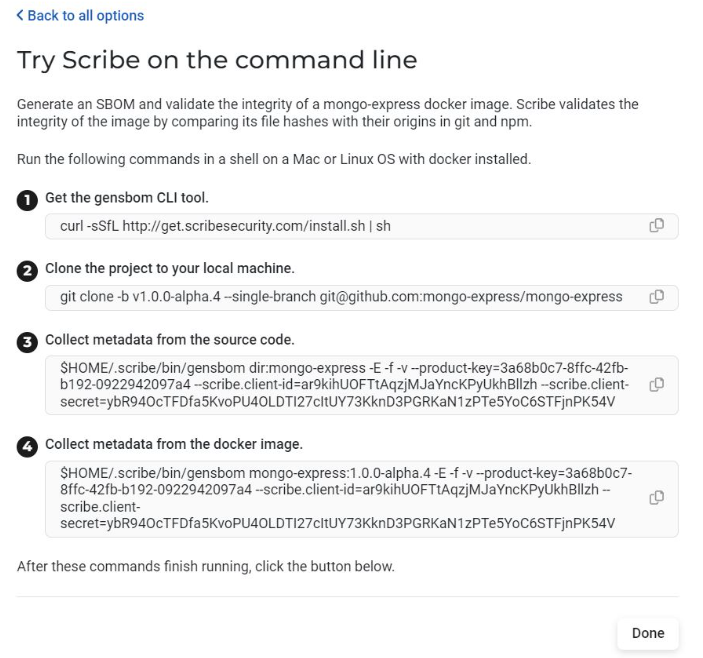
As you can see, the system shows the full CLI instructions when you click ‘Try Scribe on the command line’. The entire fact is unveiled. Employing the CLI, I simply just had to exchange the default project (mongo-specific) with the sample job I desired to test.
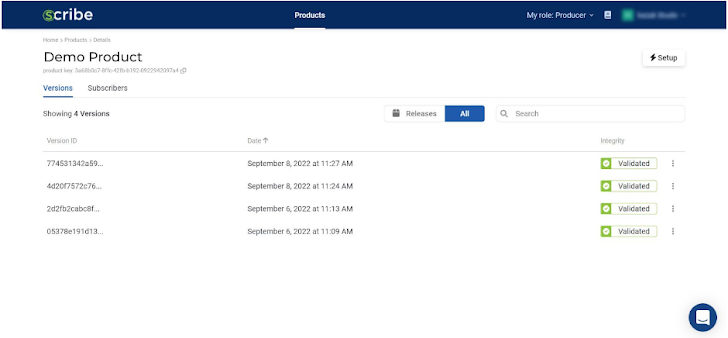
Hunting at all the software program builds I have extra to this product or service, you can see the day and time they had been established and know if they were being validated in conditions of file integrity. The a few dots at the conclusion of just about every construct allows you to ‘release’ a build—make it noticeable to the application shoppers, or subscribers, you have defined for this product. It also enables you to down load the build’s SBOM.
It was really quick to add additional assignments. The only point I experienced to do was go back again to the most important task web page and click on on ‘Add Project’. The moment you’ve performed all over with the sample products you can go ahead and include a new a single of your personal. The display screen you get is equivalent to the ‘setup’ display apart from it gives you the secrets to a brand name new solution, even though the ‘setup’ display presents you the data for the current project exactly where it can be found.
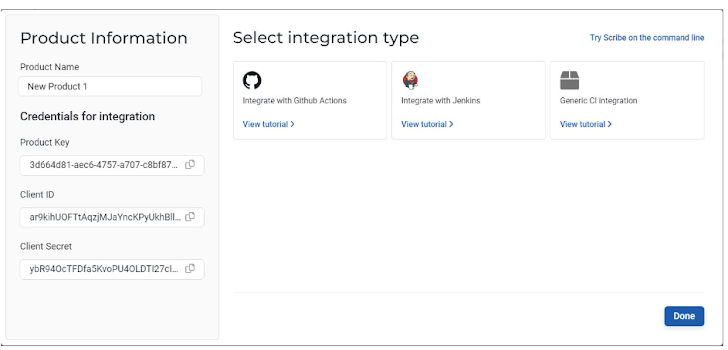
It’s actually simple to use—all I experienced to do was enter the title of the new venture. Bear in brain that there will not be substantially to see until finally I add builds or decide on subscribers for this new venture.
Credentials are what hook up my product or service pipeline to the Scribe platform: Product or service Critical, Consumer ID, and Consumer Mystery. The Shopper ID and Consumer Mystery are valid for all my future projects although the Item Essential is special to each project.
As shortly as I have all the information, I can configure my pipeline to get the required information and add it to the Scribe system.
According to its documentation, Scribe now supports GitHub, Jenkins, and other CI pipelines.
All explanations ended up quite straightforward. As aspect of my pipeline, I was requested to consist of two collectors: The very first collects information and facts about the hashes of resource code information, and the second collects data about dependency hashes. When the to start with collector is optional, the 2nd just one isn’t really. Skipping this stage will consequence in a blank report because the graphic SBOM is created by the next collector. As of the model I tried out, the Scribe system supports Node.js and npm for integrity and provenance validation. As part of this critique process, the Scribe crew also knowledgeable me that they plan to extend their supplying in the in close proximity to upcoming.
As soon as I have configured the pipeline, the specialized element is done. With this pipeline, just about every time I develop a new construct, proof and SBOM are uploaded to the Scribe platform, then processed and introduced as portion of the My Goods web page.
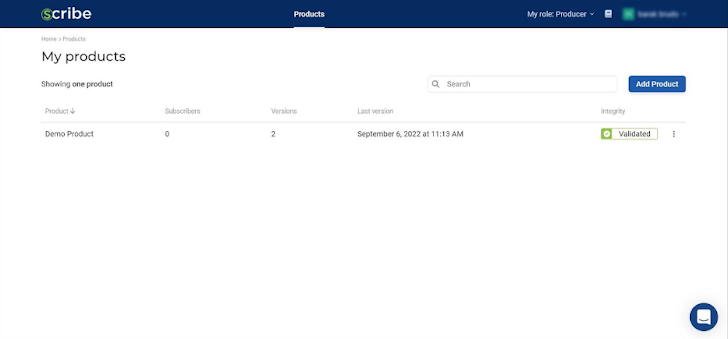
This is where by items received fascinating for me—the a variety of possibilities offered to me on the Scribe platform’s main web site. First, I recognized that I can always add a further product (top correct, blue button). There is no limit to the selection of solutions (or pipelines) I can take care of.
The data I can see for each and every merchandise incorporates its identify (the a person I chose, not automatically the a single utilized in the pipeline or SCM), its subscribers, variations, and past build variation date, as perfectly as regardless of whether its integrity was validated.
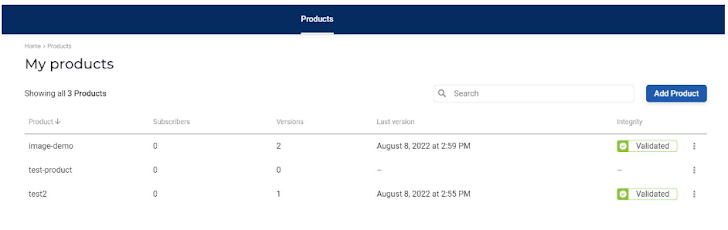
In the above image, the check-item line has no facts given that no build has been manufactured for it and no subscribers have been added. Only soon after my pipeline has uploaded some details will Scribe’s platform be ready to display me everything about that products. Info upload only occurs when a new establish is initiated, so you are going to need to induce a develop to see something in the Scribe system. It is a little bit bothersome if you were not planning on creating a new model just yet, but I realize their reasoning.
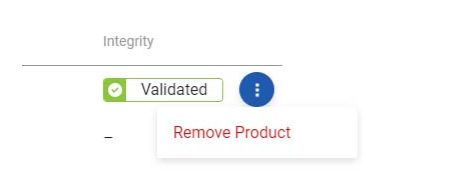
The three dots at the finish of every single line allow for me to eliminate a item if I so opt for.
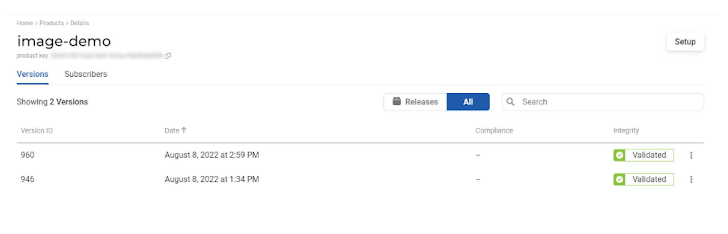
Just after clicking on a item line, I was directed to the unique solution web page. All the builds uploaded for that product are mentioned below alongside with their info.
I can determine which of the current versions (if any) can be unveiled by clicking the three dots at the finish of every line. When I publish a model, the subscribers I have extra to that product will be notified of a new launch and ready to see data connected to that release.
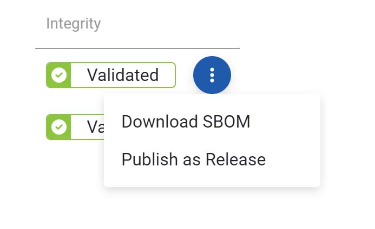
The very same menu enables me to download SBOM for that make so I can accessibility it instantly.
Previously mentioned the solution crucial you can see that there is a Subscribers tab in addition to the Versions tab.
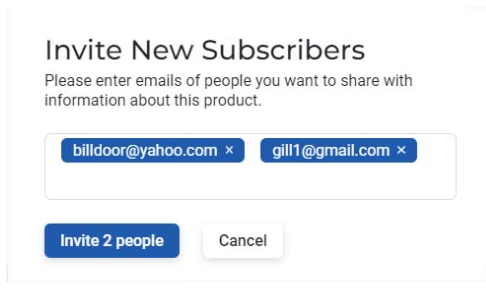
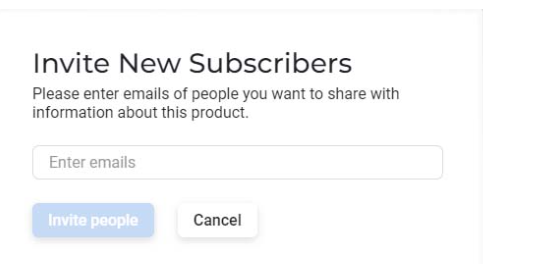
The next step was to navigate to the Subscribers tab, wherever I entered new subscribers’ email addresses to invite them to sign up for. Sure, it’s that straightforward. There was no restrict to the range of e-mails I could enter.
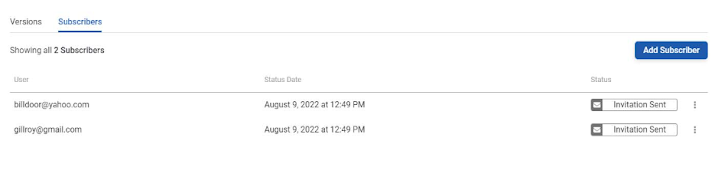
Now that I have some subscribers I can regulate them on this web page.
My job was to exam the system, so I additional two fictitious subscribers and the invite was despatched. The three dots at the end of each and every line enable you to resend the invite or revoke it. There is no uncomplicated way to determine a shared record of subscribers for many jobs considering that subscribers are managed per product or service.
Integrity report and SBOM
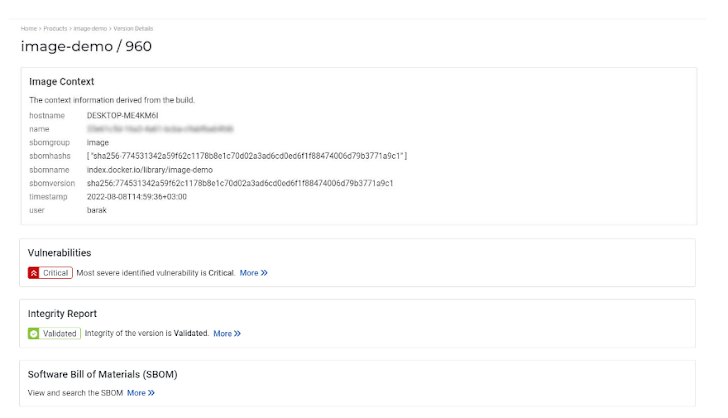
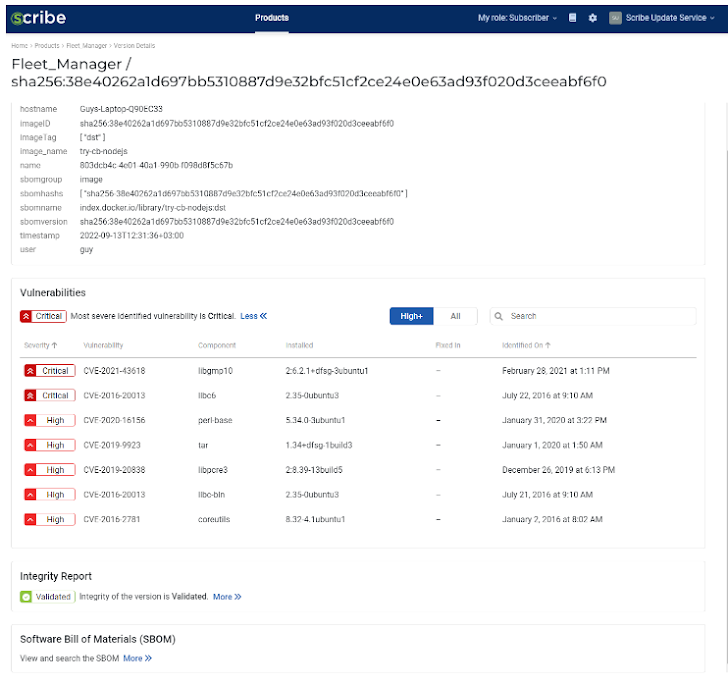
When I clicked a model line on the solitary product web page, I was taken to the build model web page. There you can come across all the context metadata about that particular build, as nicely as links to the integrity report, vulnerabilities report, and the SBOM.
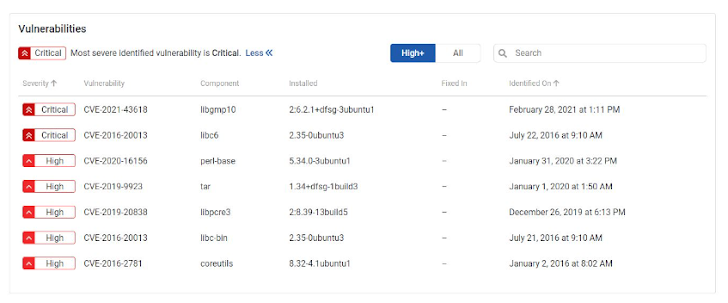
After clicking the More link in the vulnerabilities portion, we can see the vulnerabilities identified in this graphic with the CVE designation and severity. The worst CVEs are designated as critical. You have a filter on the major suitable enabling you to see only the Superior severity CVEs and up, or select to see all of the CVEs. You can also use the search bar to seem for a particular CVE you assume may well effect your build.
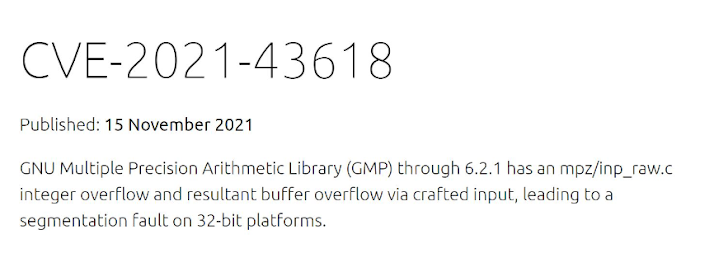
Clicking on a CVE will take you to the CVE’s specifics as they were claimed, including remediation information if it exists.
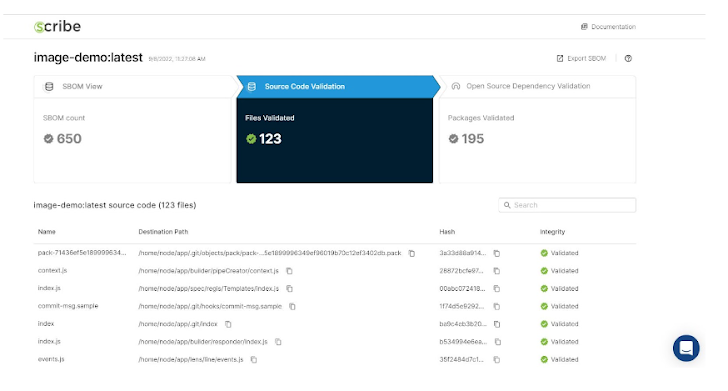
The Far more hyperlink in the Integrity Report area will take you to the entire report. I and all my subscribers have whole obtain to this report and can export the SBOM which represents the report’s fundamental info.
I can achieve the SBOM info from the preceding website page as properly by clicking the ‘more’ website link in the SBOM part.
With the integrity report, I can effortlessly see the validation of the source code (center best box), assuming I have provided that collector in my pipeline. Moreover, I can see the validation of my open-source offers (suitable top rated box) centered on the next collector I have provided.
I can also research for a specific offer, these types of as log4j, if I am so inclined. The look for alternative is independent for your supply code and open-resource offers. Recall to change to the suitable report segment at the major of the website page, depending on what you are wanting for.
If you are a software producer, preserve in thoughts that you are in entire regulate of what you share and when. No one particular is obligated to launch or share a create with a considerably less-than-excellent report only the versions you select to launch will be shared with that project’s subscribers.
Subscriber’s level of check out
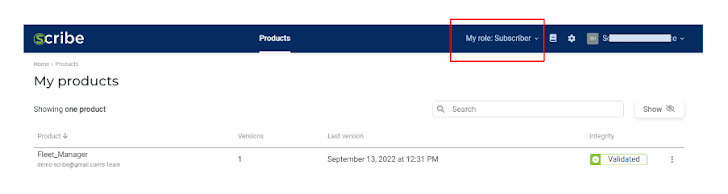
A consumer that was invited to subscribe to a item indications up as a subscriber position immediately after accepting the invitation.
The subscriber then gets a transparency report about the products and updates about CVEs (and other upcoming insights)
Proof shop for builds
Each time you operate a create you get a new edition, a new integrity report, and a new SBOM. This facts can be discovered on the Scribe system product or service site.
It operates as a repository for earlier security data and proof shop for your product where by you can constantly go back again and examine former variations. Your product or service will have a sharable evidence trail with provenance info about your source documents (if you integrated that collector) and dependencies.
Any subscriber can entry just about every model of the product or service retroactively, so you never have to have to compile heaps of experiences and SBOMs. If you are audited or want to share that facts for other factors, simply just incorporate a new subscriber’s email to that solution and they will have accessibility ideal absent.
Summary
Giving an attestation retail store and sharing hub for product builds’ security facts, this product is stable and exciting. Obviously, a great deal of imagined went into it and it truly is certainly a fantastic action ahead. So when (it is really no extended a problem of if) you have to have to crank out, regulate and share SBOMs and related security insights for your program solutions you must give it a try.
The Scribe crew plans to increase vulnerability alerts and item/pipeline security policy validation in the around long term. In my look at, these additions will enrich the platform and make it even far more worthwhile.
Check out the Scribe internet site.
Found this article appealing? Follow THN on Fb, Twitter and LinkedIn to go through additional exclusive content we publish.
Some areas of this report are sourced from:
thehackernews.com

 Google Rolling Out Passkey Passwordless Login Support to Android and Chrome
Google Rolling Out Passkey Passwordless Login Support to Android and Chrome