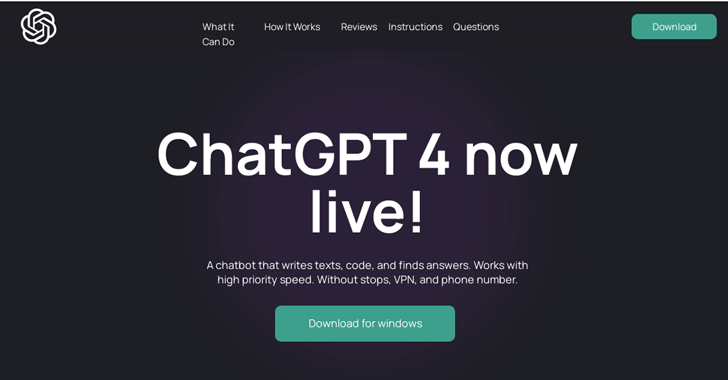
Malicious Google Lookup adverts for generative AI expert services like OpenAI ChatGPT and Midjourney are being employed to immediate users to sketchy web sites as section of a BATLOADER marketing campaign made to deliver RedLine Stealer malware.
“The two AI products and services are particularly well-liked but absence initial-party standalone applications (i.e., customers interface with ChatGPT through their web interface when Midjourney uses Discord),” eSentire stated in an analysis.
“This vacuum has been exploited by threat actors seeking to push AI app-seekers to imposter web pages advertising faux applications.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
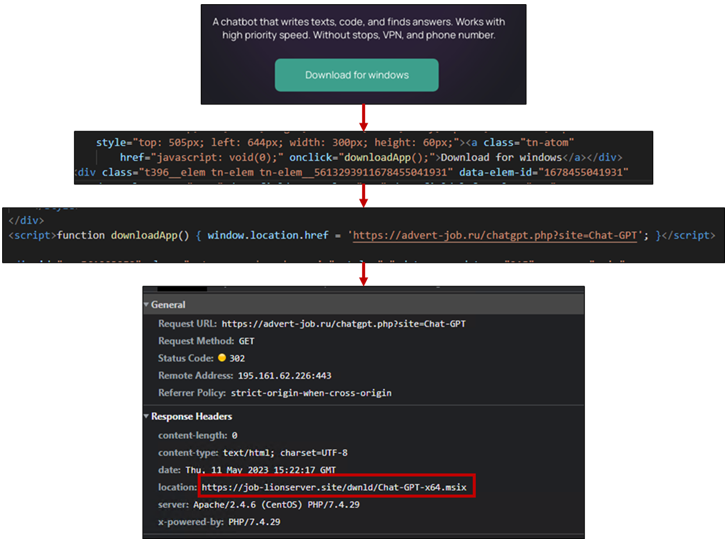
BATLOADER is a loader malware that is propagated by using drive-by downloads the place consumers exploring for certain key terms on look for engines are exhibited bogus advertisements that, when clicked, redirect them to rogue landing internet pages hosting malware.
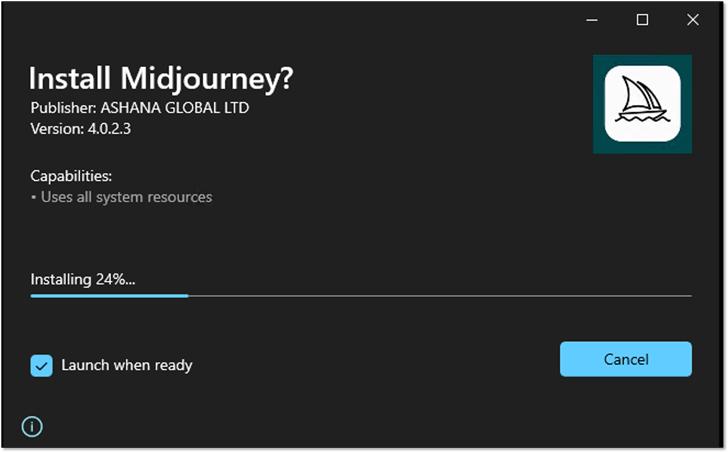
The installer file, per eSentire, is rigged with an executable file (ChatGPT.exe or midjourney.exe) and a PowerShell script (Chat.ps1 or Chat-All set.ps1) that downloads and loads RedLine Stealer from a remote server.
Once the installation is entire, the binary can make use of Microsoft Edge WebView2 to load chat.openai[.]com or www.midjourney[.]com – the legitimate ChatGPT and Midjourney URLs – in a pop-up window so as to not increase any crimson flags.
The adversary’s use of ChatGPT and Midjourney-themed lures to serve destructive advertisements and eventually fall the RedLine Stealer malware was also highlighted past week by Development Micro.
This is not the first time the operators behind BATLOADER have capitalized on the AI craze to distribute malware. In March 2023, eSentire specific a comparable established of attacks that leveraged ChatGPT lures to deploy Vidar Stealer and Ursnif.
The cybersecurity company additional pointed out the abuse of Google Look for ads has fallen off from their early 2023 peak, suggesting that the tech huge is using energetic steps to curtail its exploitation.
Impending WEBINARZero Trust + Deception: Find out How to Outsmart Attackers!
Discover how Deception can detect state-of-the-art threats, end lateral movement, and improve your Zero Rely on tactic. Join our insightful webinar!
Help you save My Seat!
The findings occur months right after Securonix uncovered a phishing campaign dubbed OCX#HARVESTER that qualified the cryptocurrency sector among December 2022 and March 2023 with More_eggs (aka Golden Chickens), a JavaScript downloader which is made use of to serve extra payloads.
eSentire, in January, traced the id of one particular of the critical operators of the malware-as-a-company (MaaS) to an specific positioned in Montreal, Canada. The next danger actor involved with the group is believed to reside in Moldova or Romania.
Found this write-up interesting? Follow us on Twitter and LinkedIn to read through much more unique material we submit.
Some areas of this short article are sourced from:
thehackernews.com

 Top 10 Considerations for Choosing the Best SAST Solutionwww.checkmarx.comDevSecOps / AppSecKnow how to compare SAST solutions before investing in a new tool.
Top 10 Considerations for Choosing the Best SAST Solutionwww.checkmarx.comDevSecOps / AppSecKnow how to compare SAST solutions before investing in a new tool.