A new information wiper malware has been noticed deployed from an unnamed Ukrainian authorities network, a day after destructive cyber attacks struck many entities in the region preceding the start out of Russia’s military services invasion.
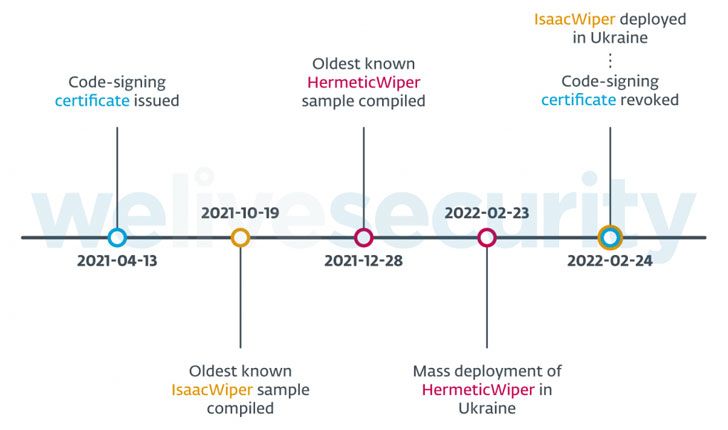
Slovak cybersecurity business ESET dubbed the new malware “IsaacWiper,” which it explained was detected on February 24 in an corporation that was not impacted by HermeticWiper (aka FoxBlade), a different information wiping malware that specific numerous companies on February 23 as portion of a sabotage procedure aimed at rendering the machines inoperable.
More investigation of the HermeticWiper attacks, which infected at minimum five Ukrainian corporations, have unveiled a worm constituent that propagates the malware throughout the compromised network and a ransomware module that functions as a “distraction from the wiper attacks,” corroborating a prior report from Symantec.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“These harmful attacks leveraged at the very least 3 components: HermeticWiper for wiping the info, HermeticWizard for spreading on the nearby network, and HermeticRansom performing as a decoy ransomware,” the firm claimed.
In a independent evaluation of the new Golang-based ransomware, Russian cybersecurity organization Kaspersky, which codenamed the malware “Elections GoRansom,” characterised it as a previous-minute operation, incorporating it was “possible used as a smokescreen for the HermeticWiper attack due to its non-innovative design and weak implementation.”
As an anti-forensic measure, HermeticWiper is also made to hinder assessment by erasing by itself from the disk by overwriting its own file with random bytes.
ESET stated it did not obtain “any tangible link” to attribute these attacks to a regarded danger actor, with the malware artifacts implying that the intrusions had been prepared for quite a few months, not to point out the fact that the targeted entities experienced compromises effectively in advance to the wiper’s deployment.
“This is based mostly on numerous specifics: the HermeticWiper PE compilation timestamps, the oldest currently being December 28, 2021 the code-signing certificate issue date of April 13, 2021 and the deployment of HermeticWiper as a result of the default domain coverage in at the very least just one occasion, suggesting the attackers had prior obtain to a single of that victim’s Active Directory servers,” said Jean-Ian Boutin, ESET head of threat research.
Also unidentified are the initial entry vectors applied to deploy the two the wipers, despite the fact that it can be suspected that the attackers leveraged tools like Impacket and RemCom, a remote accessibility computer software, for lateral motion and malware distribution.
Also, IsaacWiper shares no code-level overlaps with HermeticWiper and is significantly a lot less sophisticated, even as it sets out to enumerate all the bodily and sensible drives just before continuing to have out its file wiping operations.
“On February 25, 2022, attackers dropped a new variation of IsaacWiper with debug logs,” the scientists stated. “This may possibly show that the attackers had been unable to wipe some of the specific devices and added log messages to comprehend what was occurring.”
Discovered this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to browse more unique articles we publish.
Some sections of this report are sourced from:
thehackernews.com



 Conti Ransomware Gang’s Internal Chats Leaked Online After Siding With Russia
Conti Ransomware Gang’s Internal Chats Leaked Online After Siding With Russia