A number of backdoors have been found out in the course of a penetration test in the firmware of a broadly made use of voice above Internet Protocol (VoIP) equipment from Auerswald, a German telecommunications components manufacturer, that could be abused to attain entire administrative access to the gadgets.
“Two backdoor passwords had been found in the firmware of the COMpact 5500R PBX,” scientists from RedTeam Pentesting explained in a technical analysis posted Monday. “One particular backdoor password is for the solution user ‘Schandelah’, the other can be utilized for the optimum-privileged user ‘admin.’ No way was uncovered to disable these backdoors.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The vulnerability has been assigned the identifier CVE-2021-40859 and carries a critical severity ranking of 9.8. Next liable disclosure on September 10, Auerswald addressed the trouble in a firmware update (variation 8.2B) released in November 2021. “Firmware Update 8.2B is made up of important security updates that you must definitely utilize, even if you will not have to have the state-of-the-art attributes,” the firm reported in a post with no specifically referencing the issue.
PBX, brief for private department trade, is a switching program that serves a non-public organization. It truly is used to create and manage phone phone calls in between telecommunication endpoints, including customary phone sets, destinations on the community switched telephone network (PSTN), and gadgets or companies on VoIP networks.
RedTeam Pentesting reported it uncovered the backdoor soon after it commenced to take a closer search into a services Auerswald presents in the function a consumer were being to drop entry to their administrator account, in which circumstance the password involved with a privileged account can be reset by achieving out to the manufacturer.
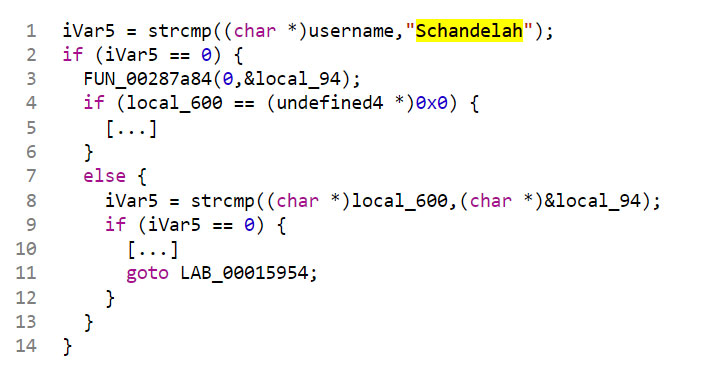
Particularly, the researchers located that the units are configured to check out for a tricky-coded username “Schandelah” besides “sub-admin,” the account that’s important to deal with the system, according to the formal documentation. “It turns out that Schandelah is the title of a small village in northern Germany the place Auerswald provides their units,” the scientists stated.
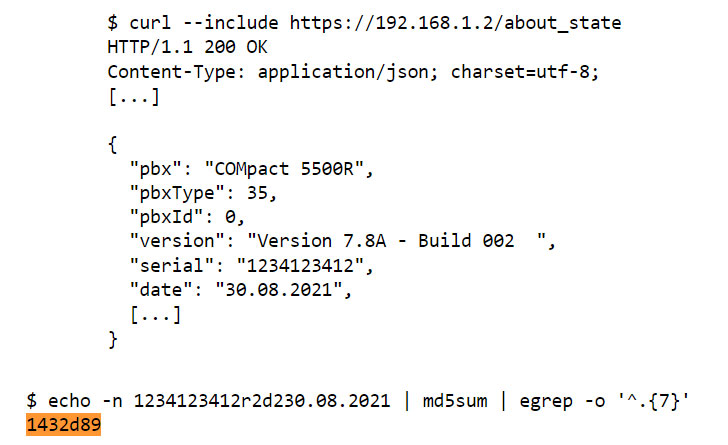
Observe-on investigation by the German pen-testing firm revealed that “the corresponding password for this username is derived by concatenating the PBX’s serial range, the string ‘r2d2,’ and the present-day day [in the format ‘DD.MM.YYYY’], hashing it with the MD5 hash algorithm and getting the first seven decreased-case hex chars of the end result.”
Set just, all an attacker requires to make the password for the username “Schandelah” is to get hold of the serial range of the PBX — a piece of information and facts that can be trivially retrieved making use of an unauthenticated endpoint (“https://192.168.1[.]2/about_point out”), enabling the poor actor to acquire accessibility to a web interface that lets for resetting the administrator password.
On major of that, the scientists claimed they determined a 2nd backdoor when the administrative username “admin” is passed, for which a fallback password is programmatically derived utilizing the aforementioned algorithm, only variance being that a two-letter place code is suffixed to the concatenated string prior to generating the MD5 hash. The alternative password, as in the previous case, provides whole-privileged entry to the PBX without the need of getting to adjust the password in the initially place.
“Using the backdoor, attackers are granted accessibility to the PBX with the greatest privileges, enabling them to totally compromise the product,” the scientists mentioned. “The backdoor passwords are not documented. They secretly coexist with a documented password restoration function supported by the vendor.”
Uncovered this report exciting? Follow THN on Fb, Twitter and LinkedIn to go through much more special information we put up.
Some pieces of this report are sourced from:
thehackernews.com



 NCA donates 225 million passwords to Have I Been Pwned
NCA donates 225 million passwords to Have I Been Pwned