Common messaging application Telegram preset a privacy-defeating bug in its macOS application that manufactured it achievable to access self-destructing audio and video clip messages long right after they disappeared from key chats.
The vulnerability was uncovered by security researcher Dhiraj Mishra in edition 7.3 of the application, who disclosed his conclusions to Telegram on December 26, 2020. The issue has considering that been fixed in variation 7.4, introduced on January 29.
Contrary to Sign or WhatsApp, discussions on Telegram by default are not conclusion-to-finish encrypted, unless end users explicitly opt to permit a unit-certain feature referred to as “magic formula chat,” which retains information encrypted even on Telegram servers. Also readily available as part of top secret chats is the alternative to mail self-destructing messages.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

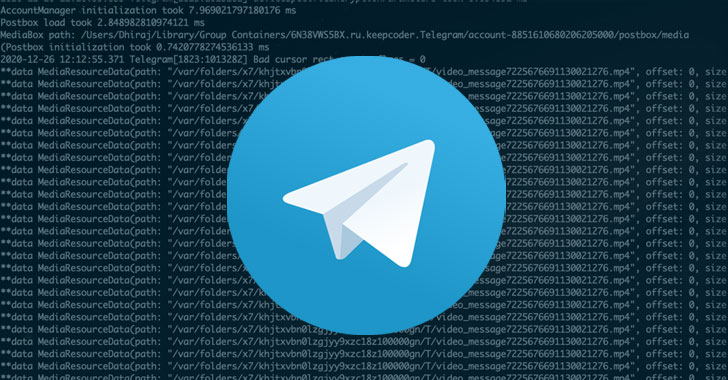
What Mishra located was that when a consumer data and sends an audio or movie concept by way of a common chat, the software leaked the actual path the place the recorded information is saved in “.mp4” format. With the solution chat selection turned on, the path information is not spilled, but the recorded information still will get stored in the exact site.
In addition, even in circumstances wherever a consumer gets a self-destructing message in a mystery chat, the multimedia message stays accessible on the procedure even after the concept has disappeared from the app’s chat monitor.
“Telegram suggests ‘super secret’ chats do not go away traces, but it outlets the community copy of this sort of messages underneath a customized route,” Mishra informed The Hacker News.
Separately, Mishra also recognized a 2nd vulnerability in Telegram’s macOS application that saved regional passcodes in plaintext in a JSON file situated beneath “/Buyers/
Mishra was awarded €3,000 for reporting the two flaws as part of its bug bounty system.
Telegram in January hit a milestone of 500 million lively regular customers, in part led by a surge in customers who fled WhatsApp next a revision to its privacy policy that involves sharing specific data with its company mother or father, Fb.
Though the company does offer you customer-server/server-customer encryption (utilizing a proprietary protocol named “MTProto”) and also when the messages are saved in the Telegram cloud, it’s worthy of holding in thoughts that team chats give no finish-to-stop encryption and that all default chat histories are saved on its servers. This is to make conversations effortlessly obtainable across equipment.
“So if you are on Telegram and want a definitely non-public team chat, you might be out of luck,” Raphael Mimoun, founder of the electronic security nonprofit Horizontal, reported previous month.
Discovered this posting fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to study much more unique information we write-up.
Some sections of this posting are sourced from:
thehackernews.com

 Queen’s University Belfast Recognized for Role in Growing Cybersecurity Awareness
Queen’s University Belfast Recognized for Role in Growing Cybersecurity Awareness