A systematic examination of attacks in opposition to Microsoft’s Internet Info Providers (IIS) servers has discovered as quite a few as 14 malware families, 10 of them recently documented, indicating that the Windows-dependent web server computer software carries on to be a hotbed for natively made malware for close to 8 yrs.
The results ended up introduced these days by ESET malware researcher Zuzana Hromcova at the Black Hat Usa security convention.
“The a variety of kinds of native IIS malware identified are server-aspect malware and the two points it can do very best is, initially, see and intercept all communications to the server, and next, influence how the requests are processed,” Hromcova instructed in an interview with The Hacker News. “Their motivations variety from cybercrime to espionage, and a technique identified as Seo fraud.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

IIS is an extensible web server computer software created by Microsoft, enabling builders to acquire advantage of its modular architecture and use added IIS modules to grow on its core performance.
“It arrives as no surprise that the exact extensibility is appealing for malicious actors – to intercept network targeted traffic, steal sensitive info or provide malicious content,” in accordance to a ESET report shared with The Hacker News.
“Also, it is quite uncommon for endpoint (and other) security computer software to run on IIS servers, which would make it effortless for attackers to function unnoticed for long periods of time. This should be disturbing for all severe web portals that want to protect their visitors’ info, which includes authentication and payment details.”
 IIS malware phases
IIS malware phases
By amassing above 80 malware samples, the review grouped them into 14 unique family members (Team 1 to Team 14), most of which ended up initial detected concerning 2018 and 2021 and undergoing energetic development to date. Even though they may not show any link to just one a different, what’s frequent between all the 14 malware households is that they are all produced as destructive indigenous IIS modules.
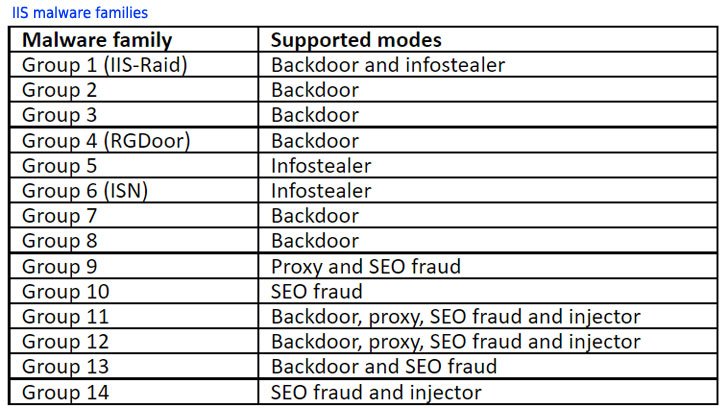
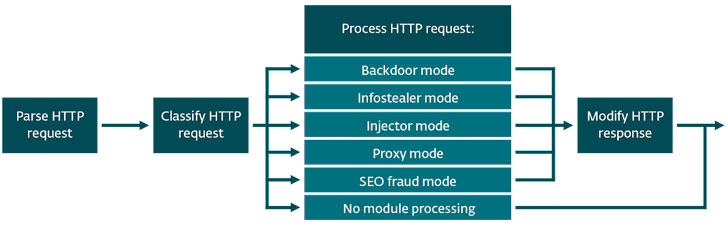
“In all situations, the most important goal of IIS malware is to approach HTTP requests incoming to the compromised server and have an affect on how the server responds to (some of) these requests – how they are processed relies upon on malware type,” Hromcova spelled out. The malware family members have been found to function in one of the five modes –
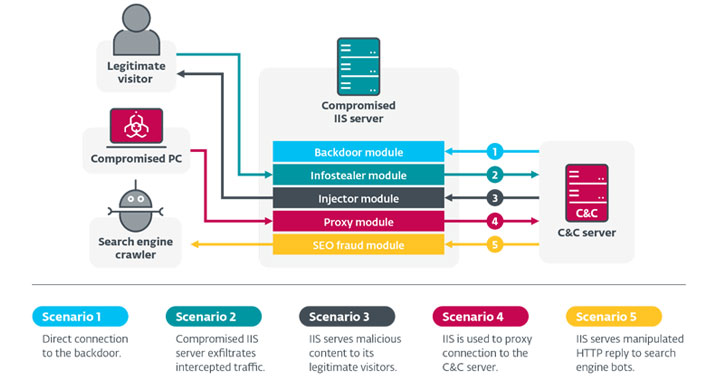
- Backdoor manner – remotely control the compromised personal computer with IIS mounted
- Infostealer method – intercept regular traffic involving the compromised server and its genuine readers, to steal information and facts such as login qualifications and payment info
- Injector mode – modify HTTP responses sent to genuine readers to provide malicious content
- Proxy method – change the compromised server into an unwitting component of command-and-regulate (C2) infrastructure for yet another malware family, and relay conversation amongst victims and the genuine C2 server
- Seo fraud manner – modify the articles served to research engine crawlers in order to artificially enhance rating for picked internet sites (aka doorway internet pages)
Infections involving IIS malware ordinarily hinge on server directors inadvertently setting up a trojanized edition of a reputable IIS module or when an adversary is able to get access to the server by exploiting a configuration weak spot or vulnerability in a web application or the server, utilizing it to install the IIS module.
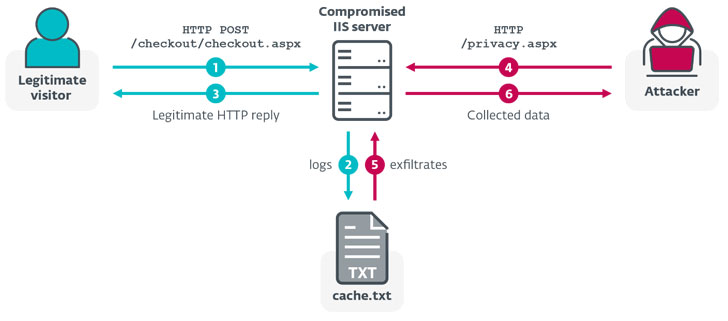 infostealing mechanism
infostealing mechanism
Just after Microsoft released out-of-band patches for ProxyLogon flaws affecting Microsoft Exchange Server 2013, 2016, and 2019 earlier this March, it was not prolonged before several state-of-the-art persistent risk (APT) teams joined in the attack frenzy, with ESET observing four email servers found in Asia and South America that were being compromised to deploy web shells that served as a channel to install IIS backdoors.

This is much from the initial time Microsoft web server software program has emerged a beneficial concentrate on for danger actors. Past thirty day period, researchers from Israeli cybersecurity agency Sygnia disclosed a collection of specific cyber intrusion attacks carried out by an superior, stealthy adversary acknowledged as Praying Mantis focusing on internet-dealing with IIS servers to infiltrate large-profile community and non-public entities in the U.S.
To reduce compromise of IIS servers, it’s advisable to use focused accounts with sturdy, one of a kind passwords for administration-similar reasons, put in indigenous IIS modules only from dependable resources, reduce the attack surface area by restricting the services that are exposed to the internet, and use a web application firewall for an further layer of security.
“One of the most shocking facets of the investigation is how versatile IIS malware is, and the [detection of] Search engine marketing fraud criminal scheme, wherever malware is misused to manipulate search engine algorithms and assistance strengthen the status of third-party internet websites,” Hromcova explained. “We have not noticed something like that just before.”
Discovered this write-up fascinating? Stick to THN on Facebook, Twitter and LinkedIn to read a lot more exclusive written content we put up.
Some elements of this report are sourced from:
thehackernews.com

 US Senate: Seven out of Eight Agencies Are Failing on Cyber
US Senate: Seven out of Eight Agencies Are Failing on Cyber