Cybersecurity scientists on Wednesday disclosed a number of security vulnerabilities impacting CODESYS automation computer software and the WAGO programmable logic controller (PLC) platform that could be remotely exploited to take command of a company’s cloud operational technology (OT) infrastructure.
The flaws can be turned “into modern attacks that could place threat actors in posture to remotely management a company’s cloud OT implementation, and threaten any industrial system managed from the cloud,” the New York-headquartered industrial security firm Claroty claimed in a report shared with The Hacker Information, including they “can be utilized to goal a cloud-based administration console from a compromised area product, or just take about a firm’s cloud and attack PLCs and other units to disrupt functions.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CODESYS is a advancement ecosystem for programming controller applications, enabling uncomplicated configuration of PLCs in industrial control systems. WAGO PFC100/200 is a collection of PLCs that make use of the CODESYS system for programming and configuring the controllers.
The list of 7 vulnerabilities is listed underneath –
- CVE-2021-29238 (CVSS rating: 8.) – Cross-web-site request forgery in CODESYS Automation Server
- CVE-2021-29240 (CVSS score: 7.8) – Inadequate Verification of Knowledge Authenticity in CODESYS Bundle Supervisor
- CVE-2021-29241 (CVSS score: 7.5) – Null pointer dereference in CODESYS V3 solutions that contains the CmpGateway component
- CVE-2021-34569 (CVSS rating: 10.) – WAGO PFC diagnostic equipment – Out-of-bounds publish
- CVE-2021-34566 (CVSS rating: 9.1) – WAGO PFC iocheckd services “I/O-Check out” – Shared memory buffer overflow
- CVE-2021-34567 (CVSS rating: 8.2) – WAGO PFC iocheckd service “I/O-Verify” – Out-of-bounds go through
- CVE-2021-34568 (CVSS rating: 7.5) – WAGO PFC iocheckd service “I/O-Look at” – Allocation of resources devoid of limitations
Effective exploitation of the flaws could help the installation of destructive CODESYS packages, end result in a denial-of-provider (DoS) condition, or direct to privilege escalation by way of execution of destructive JavaScript code, and even worse, manipulation or total disruption of the gadget.
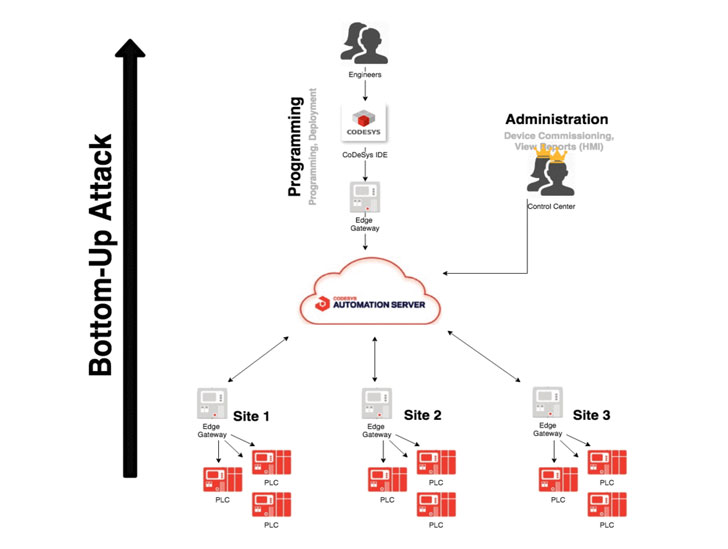
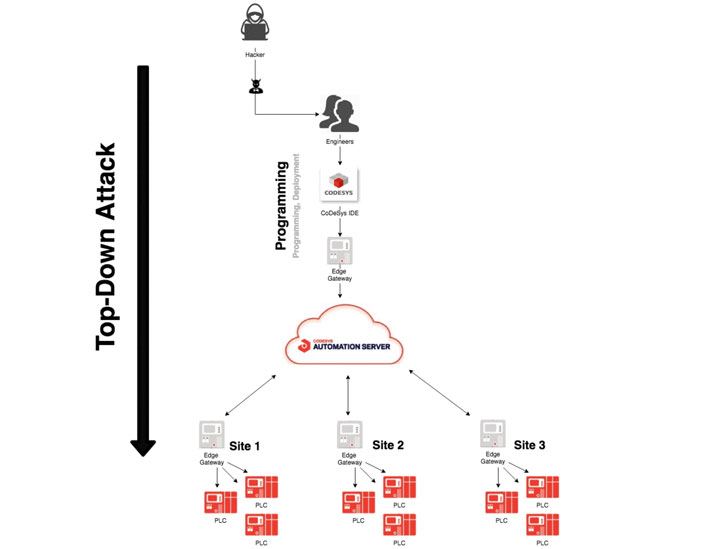
In the wild, this could participate in out in 1 of two techniques: “base-up” or “best-down.” The twin methods mimic the paths an adversary is very likely to just take to either command a PLC endpoint in order to sooner or later compromise the cloud-centered administration console, or the reverse, commandeer the cloud in buy to manipulate all networked subject devices.

In a “base-up” intricate exploit chain devised by Claroty, a blend of CVE-2021-34566, CVE-2021-34567, and CVE-2021-29238 had been exploited to get distant code execution on the WAGO PLC, only to get access to the CODESYS WebVisu human-machine interface and stage a cross-web page request forgery (CSRF) attack to seize handle of the CODESYS automation server occasion.
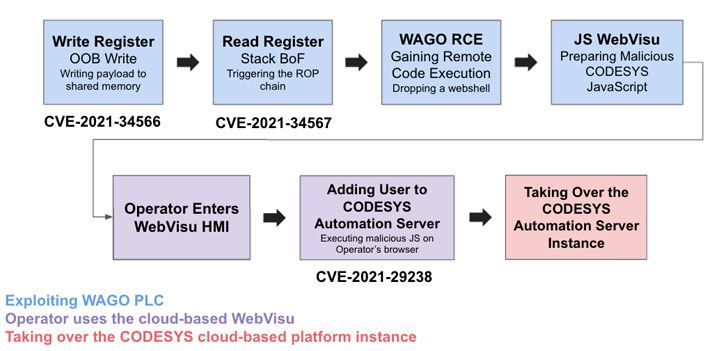
“An attacker that obtains access to a PLC managed by the Automation Server Cloud can modify the ‘webvisu.js’ file and append JavaScript code to the conclusion of the file that will send out a malicious ask for to the cloud server on behalf of the logged in person,” Claroty senior researcher Uri Katz, who learned and documented the flaws, spelled out.
“When a cloud user views the WebVisu webpage, the modified JavaScript will exploit the absence of CSRF token and run in the context of the person viewing it the ask for will contain the CAS cookie. Attackers can use this to Article to ‘/api/db/User’ with a new administrator user, supplying them full obtain to the CODESYS cloud system,” Katz included.
An alternate “top rated-down” attack circumstance, on the other hand, will involve compromising the CODESYS engineering station by deploying a destructive offer (CVE-2021-29240) that’s intended to leak the cloud qualifications related with an operator account, and subsequently employing it to tamper with the programmed logic and get unfettered obtain to all the connected PLCs.
“Organizations going ahead with cloud-dependent management of OT and ICS gadgets ought to be informed of the inherent risks, and increased threats from attackers keen on focusing on industrial enterprises with extortion-primarily based attacks—including ransomware—and much more refined attacks that can trigger bodily problems,” Katz reported.
The disclosures mark the 2nd time-critical flaws that have been uncovered in CODESYS and WAGO PLCs in as quite a few months. In June, researchers from Favourable Technologies unveiled ten critical vulnerabilities in the software’s web server and runtime method components that could be abused to attain remote code execution on the PLCs.
The development also arrives a week just after IoT security firm Armis disclosed a critical authentication bypass vulnerability affecting Schneider Electric powered Modicon PLCs — dubbed “ModiPwn” (CVE-2021-22779) — that could be exploited to let entire regulate about the PLC, together with overwriting critical memory areas, leaking sensitive memory written content, or invoking internal capabilities.
In a related report revealed previously this Might, Claroty made community a memory defense bypass vulnerability in Siemens SIMATIC S7-1200 and S7-1500 PLCs (CVE-2020-15782) that could be leveraged by a malicious actor to remotely acquire access to safeguarded regions of the memory and reach unrestricted and undetected code execution.
The revelations also coincide with a joint cybersecurity advisory introduced by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) documenting a historical spear-phishing and intrusion marketing campaign conducted by condition-sponsored Chinese actors from December 2011 to 2013, concentrating on 23 oil and purely natural fuel (ONG) pipeline operators in the country.
“CISA and the FBI evaluate that these actors had been exclusively focusing on U.S. pipeline infrastructure for the reason of holding U.S. pipeline infrastructure at risk,” the businesses explained. “Furthermore, CISA and the FBI evaluate that this exercise was finally meant to enable China produce cyberattack abilities versus U.S. pipelines to physically destruction pipelines or disrupt pipeline functions.”
Uncovered this posting fascinating? Comply with THN on Facebook, Twitter and LinkedIn to study a lot more distinctive articles we put up.
Some sections of this post are sourced from:
thehackernews.com

![[ebook] a guide to stress free cybersecurity for lean it security](https://thecybersecurity.news/data/2021/07/eBook-A-Guide-to-Stress-Free-Cybersecurity-for-Lean-IT-Security-80x80.jpg) [eBook] A Guide to Stress-Free Cybersecurity for Lean IT Security Teams
[eBook] A Guide to Stress-Free Cybersecurity for Lean IT Security Teams