A quantity of high-profile Android applications are however utilizing an unpatched version of Google’s greatly-utilised app update library, possibly putting the individual facts of hundreds of millions of smartphone consumers at risk of hacking.
Lots of preferred apps, together with Grindr, Bumble, OkCupid, Cisco Groups, Moovit, Yango Pro, Microsoft Edge, Xrecorder, and PowerDirector, are still vulnerable and can be hijacked to steal delicate information, these as passwords, economic specifics, and e-mails.
The bug, tracked as CVE-2020-8913, is rated 8.8 out of 10. for severity and impacts Android’s Enjoy Main Library versions prior to 1.7.2.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Although Google resolved the vulnerability in March, new findings from Test Stage Investigation demonstrate that quite a few third-party app builders are however to combine the new Perform Core library into their applications to mitigate the threat entirely.
“As opposed to server-side vulnerabilities, wherever the vulnerability is patched wholly after the patch is used to the server, for client-facet vulnerabilities, each individual developer wants to get the newest edition of the library and insert it into the application,” the cybersecurity firm stated in a report.
Participate in Core Library is a well-known Android library that will allow developers to regulate the shipping of new element modules proficiently, set off in-app updates at runtime, and down load added language packs.
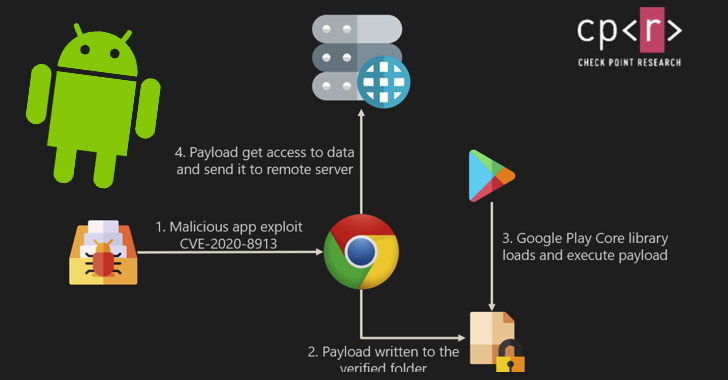
First claimed in late August by scientists at application security startup Oversecured, the issue allows a danger actor to inject destructive executables to any application relying on the library, thus granting the attacker comprehensive entry to all the assets as that of the compromised software.
The flaw stems from a path traversal vulnerability in the library that could be exploited to load and execute destructive code (e.g., an APK file) on to a concentrate on app to steal users’ login specifics, passwords, fiscal details, and other delicate info stored in it.
The outcomes of thriving exploitation of this flaw are enormous. It can be utilised to “inject code into banking programs to seize qualifications, and at the very same time have SMS permissions to steal the two-factor authentication (2FA) codes,” seize messages from chat apps, spy on users’ spots, and even attain obtain to company sources by tampering with business applications.
According to Verify Position Investigation, of the 13% of Google Enjoy applications analyzed in the thirty day period of September 2020, 8% of people applications experienced a susceptible model.
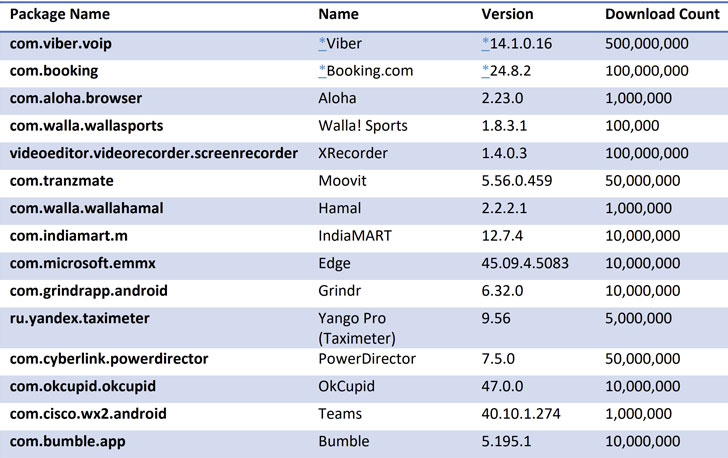
Immediately after the cybersecurity organization responsibly disclosed their conclusions, Viber, Meetup, and Booking.com up to date their apps to the patched edition of the library.
The researchers also demonstrated a evidence-of-principle that utilized a susceptible version of the Google Chrome application to siphon the bookmarks saved in the browser via a focused payload.
“We’re estimating that hundreds of thousands and thousands of Android end users are at security risk,” Look at Point’s Manager of Cellular Analysis, Aviran Hazum, said. “Even though Google executed a patch, several apps are continue to using out-of-date Participate in Main libraries. The vulnerability CVE-2020-8913 is extremely harmful, [and] the attack options below are only limited by a risk actor’s creativity.”
Discovered this short article interesting? Abide by THN on Facebook, Twitter and LinkedIn to read extra special content material we submit.
Some elements of this article are sourced from:
thehackernews.com

 Philly Food Bank Loses $1m in BEC Scam
Philly Food Bank Loses $1m in BEC Scam