ShadowPad, an notorious Windows backdoor that allows attackers to obtain further destructive modules or steal facts, has been place to use by five distinctive Chinese danger clusters considering that 2017.
“The adoption of ShadowPad considerably decreases the fees of improvement and routine maintenance for danger actors,” SentinelOne scientists Yi-Jhen Hsieh and Joey Chen mentioned in a specific overview of the malware, including “some risk teams stopped producing their personal backdoors following they acquired accessibility to ShadowPad.”
The American cybersecurity firm dubbed ShadowPad a “masterpiece of privately marketed malware in Chinese espionage.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

A successor to PlugX and a modular malware platform because 2015, ShadowPad catapulted to widespread attention in the wake of source chain incidents focusing on NetSarang, CCleaner, and ASUS, primary the operators to change tactics and update their defensive actions with superior anti-detection and persistence strategies.
Extra just lately, attacks involving ShadowPad have singled out companies in Hong Kong as effectively as critical infrastructure in India, Pakistan, and other Central Asian countries. Whilst mostly attributed to APT41, the implant is recognised to be shared between quite a few Chinese espionage actors this kind of as Tick, RedEcho, RedFoxtrot, and clusters dubbed Operation Redbonus, Redkanku, and Fishmonger.
“[The threat actor behind Fishmonger is] now using it and another backdoor identified as Spyder as their key backdoors for prolonged-phrase checking, whilst they distribute other very first-phase backdoors for preliminary infections such as FunnySwitch, BIOPASS RAT, and Cobalt Strike,” the researchers reported. “The victims include things like universities, governments, media sector providers, technology businesses and well being corporations conducting COVID-19 exploration in Hong Kong, Taiwan, India and the U.S.”

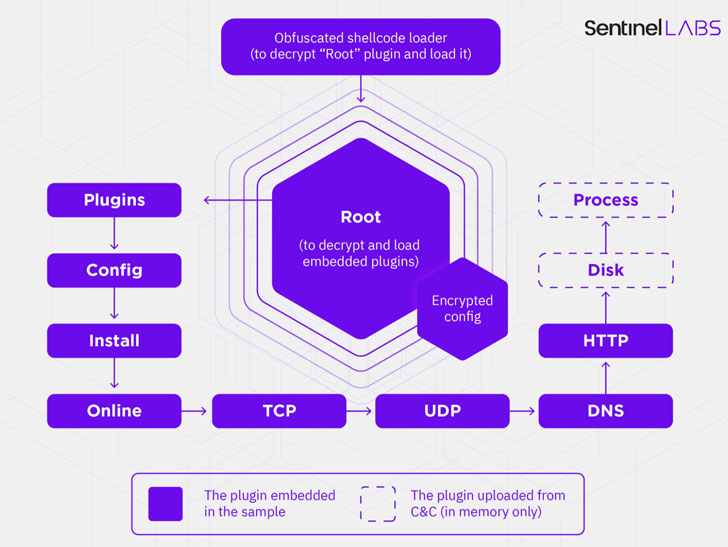
The malware functions by decrypting and loading a Root plugin in memory, which usually takes care of loading other embedded modules through runtime, in addition to dynamically deploying supplemental plugins from a remote command-and-handle (C2) server, enabling adversaries to integrate excess features not built into the malware by default. At the very least 22 exclusive plugins have been determined to date.
The contaminated machines, for their aspect, are commandeered by a Delphi-based controller that’s employed for backdoor communications, updating the C2 infrastructure, and handling the plugins.
Apparently, the characteristic established designed out there to ShadowPad buyers is not only tightly managed by its vendor, each individual plugin is offered independently as an alternative of featuring a entire bundle made up of all of the modules, with most samples — out of about 100 — embedded with much less than nine plugins.
“The emergence of ShadowPad, a privately offered, well-developed and functional backdoor, offers danger actors a fantastic prospect to shift absent from self-designed backdoors,” the scientists explained. “When it is very well-created and hugely possible to be generated by an experienced malware developer, both of those its functionalities and its anti-forensics abilities are below energetic development.”
Found this short article interesting? Comply with THN on Facebook, Twitter and LinkedIn to read through a lot more special content material we put up.
Some areas of this write-up are sourced from:
thehackernews.com


 AVG Internet Security review: Money for nothing
AVG Internet Security review: Money for nothing