Cybersecurity researchers on Monday took the wraps off a new Android trojan that will take benefit of accessibility characteristics on the gadgets to siphon credentials from banking and cryptocurrency services in Italy, the U.K., and the U.S.
Dubbed “SharkBot” by Cleafy, the malware is designed to strike a total of 27 targets — counting 22 unnamed global banking institutions in Italy and the U.K. as perfectly as 5 cryptocurrency applications in the U.S. — at least given that late October 2021 and is thought to be in its early stages of growth, with no overlaps located to that of any identified households.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
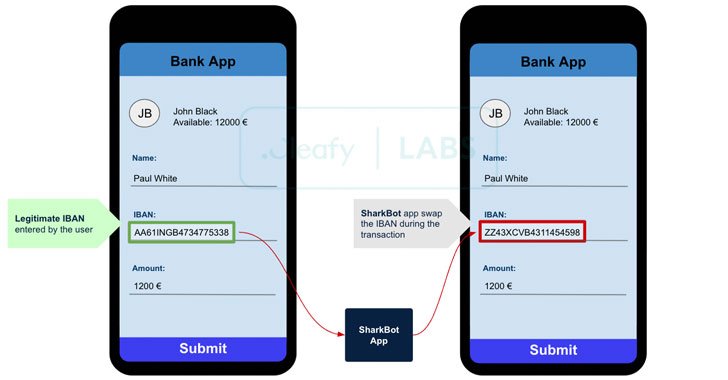
“The primary intention of SharkBot is to initiate dollars transfers from the compromised products by means of Automatic Transfer Programs (ATS) approach bypassing multi-factor authentication mechanisms (e.g., SCA),” the researchers stated in a report.
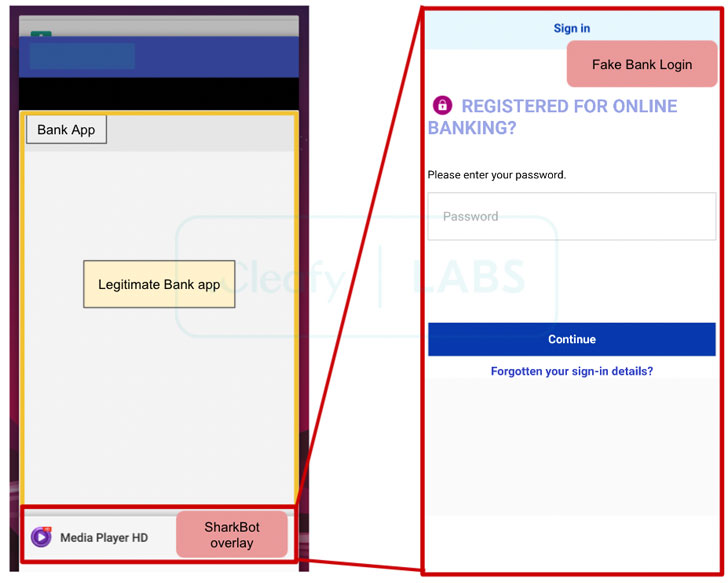
“After SharkBot is successfully mounted in the victim’s system, attackers can attain delicate banking data by means of the abuse of Accessibility Expert services, these as credentials, individual data, current equilibrium, etcetera., but also to perform gestures on the contaminated system.”
Masquerading as a media player, are living Tv, or information restoration apps, SharkBot, like its other malware counterparts TeaBot and UBEL, consistently prompts people with rogue pop-ups to grant it wide permissions only to steal delicate info. Wherever it stands aside is the exploitation of accessibility settings to carry out ATS attacks, which enable the operators to “automobile-fill fields in legitimate cellular banking apps and initiate dollars transfers from the compromised products to a revenue mule network managed by the [threat actor].”
The modus operandi effectively obviates the require for enrolling a new gadget to accomplish fraudulent things to do, even though also bypassing two-factor authentication mechanisms set in place by the banking applications.

In addition, the malware comes with all capabilities now noticed across all Android banking trojans, these kinds of as the means to carry out overlay attacks to steal login credentials and credit rating card facts, intercept reputable banking communications despatched by means of SMS, permit keylogging, and obtain whole remote manage of the compromised products.
SharkBot is also notable for the measures it takes to evade investigation and detection, which include working emulator checks, encrypting command-and-management communications with a distant server, and hiding the app’s icon from the household screen submit-installation. No samples of the malware have been detected on the formal Google Perform Keep, implying that the malicious applications are installed on the users’ equipment possibly through sideloading or social engineering techniques.
The discovery of SharkBot in the wild exhibits “how cell malwares are immediately obtaining new strategies to complete fraud, seeking to bypass behavioural detection countermeasures put in position by a number of financial institutions and economic companies throughout the final yrs,” the scientists claimed.
Observed this post intriguing? Follow THN on Fb, Twitter and LinkedIn to examine a lot more distinctive material we publish.
Some pieces of this article are sourced from:
thehackernews.com

 The Best Ransomware Response, According to the Data
The Best Ransomware Response, According to the Data 