A cyber-espionage group has been noticed ever more focusing on Indian govt staff as aspect of a wide campaign to infect victims with as a lot of as 4 new personalized remote access trojans (RATs), signaling a “enhance in their progress functions.”
Attributed to a team tracked as SideCopy, the intrusions culminate in the deployment of a selection of modular plugins, ranging from file enumerators to browser credential stealers and keyloggers (Xeytan and Lavao), Cisco Talos explained in a report released Wednesday.
“Targeting practices and themes observed in SideCopy strategies reveal a substantial degree of similarity to the Transparent Tribe APT (aka APT36) also focusing on India,” researchers Asheer Malhotra and Justin Thattil mentioned. “These include utilizing decoys posing as operational paperwork belonging to the navy and assume tanks and honeytrap-based mostly bacterial infections.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Initial documented in September 2020 by Indian cybersecurity organization Speedy Heal, SideCopy has a record of mimicking infection chains carried out by the Sidewinder APT to deliver its possess set of malware — in an try to mislead attribution and evade detection — even though frequently retooling payloads that include things like further exploits in its weaponry immediately after a reconnaissance of the victim’s data and environment.
The adversary is also considered to be of Pakistani origin, with suspected ties to the Transparent Tribe (aka Mythic Leopard) team, which has been connected to a number of attacks focusing on the Indian navy and authorities entities. Earlier strategies carried out by the risk actor involve making use of govt and armed service-linked lures to solitary out Indian defense models and armed forces staff and provide malware capable of accessing data files, clipboard data, terminating procedures, and even executing arbitrary commands.
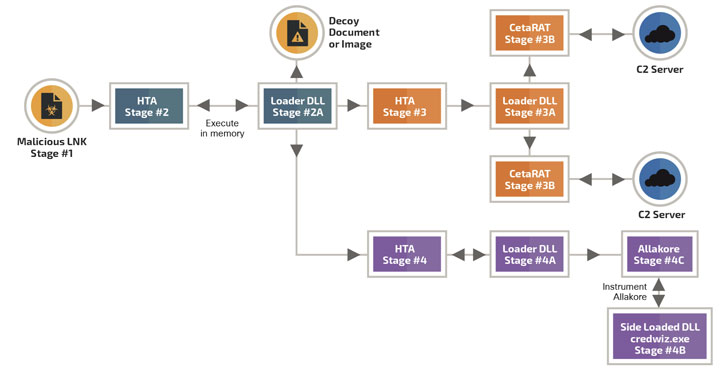
The latest wave of attacks leverages a multitude of TTPs, like malicious LNK data files and decoy files, to supply a mix of bespoke and commercially obtainable commodity RATs such as CetaRAT, DetaRAT, ReverseRAT, MargulasRAT, njRAT, Allakore, ActionRAT, Lillith, and Epicenter RAT. Aside from armed forces themes, SideCopy has also been located using phone calls for proposals and work openings linked to feel tanks in India to concentrate on likely victims.
“The advancement of new RAT malware is an indication that this team of attackers is speedily evolving its malware arsenal and article-infection tools considering the fact that 2019,” Malhotra and Thattil observed. The enhancements reveal an work to modularize the attack chains, when also demonstrating an boost in sophistication of the group’s strategies, the researchers claimed.
Moreover deploying whole-fledged backdoors, SideCopy has also been observed utilizing plugins to have out certain destructive duties on the contaminated endpoint, chief among which is a Golang-primarily based module named “Nodachi” that is intended to conduct reconnaissance and steal documents focusing on a government-mandated two-factor authentication solution referred to as Kavach, which is needed to obtain email providers.

The goal, it appears, is to steal obtain credentials from Indian authorities workforce with a aim on espionage, the scientists reported, including the threat actor made droppers for MargulasRAT that masqueraded as installers for Kavach on Windows.
Malware researcher @0xrb, who is also independently tracking the marketing campaign, achieved out to The Hacker News with two more IPs made use of by SideCopy attackers to join to the command-and-control server — 103[.]255.7.33 and 115[.]186.190.155 — both equally of which are situated in the city of Islamabad, lending credence to the threat actor’s Pakistani provenance.
“What begun as a very simple infection vector by SideCopy to produce a custom RAT (CetaRAT), has evolved into multiple variants of an infection chains delivering numerous RATs,” the researchers concluded. “The use of these lots of infection procedures — ranging from LNK documents to self-extracting RAR EXEs and MSI-based installers — is an sign that the actor is aggressively performing to infect their victims.”
Located this write-up interesting? Follow THN on Fb, Twitter and LinkedIn to browse much more special material we article.
Some components of this article are sourced from:
thehackernews.com


 Microsoft’s emergency ‘PrintNightmare’ patch fails to fix critical exploit
Microsoft’s emergency ‘PrintNightmare’ patch fails to fix critical exploit