Security Operations is a 24 x 7 work. It does not quit for weekends or holiday seasons or even that a great deal-required coffee split just after the very first hour of the change is comprehensive. We all know this.
Each and every SOC engineer is hoping for some relaxation at some place. Just one of my preferred jokes when talking about Security Operations is “3 SOC engineers walked into a bar…” That the joke. No SOC engineers have time to do that. They get it. They giggle. So why is this all accurate?
Enable us check out that a minor little bit.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
- Need for experienced SOC engineers much surpasses the out there expertise.
- Function volume concentrations boggle the imagination when compared to even just a couple several years in the past.
- Utilization of tools to their utmost ability has usually not been a precedence.
In the Security Functions place, we have been applying SIEM’s for lots of decades with various levels of deployments, customization, and usefulness. For the most element, they have been a beneficial software for Security Operations. But they can be greater. Like any resource, they require to be sharpened and employed the right way.
Right after a though, even a sharpened software can turn into dull from way too significantly use: and with a SIEM that takes the sort of far too numerous gatherings building the dreaded Alert Exhaustion!!!
This is real for security operations and have to be dealt with due to the fact the a lot more alerts, the much more an engineer have to operate on, and the a lot more they will miss out on.
Insert Sigma Regulations for SIEMS (pun supposed) a way for Security Operations to implement standardization into the day by day responsibilities of creating SIEM queries, controlling logs, and danger hunting correlations.
What is a Sigma rule, you may perhaps inquire? A Sigma rule is a generic and open up, YAML-primarily based signature format that enables a security operations group to describe appropriate log activities in a versatile and standardized structure.
So, what does that necessarily mean for security operations? Standardization and Collaboration are now extra feasible than ever before with the adoption of Sigma Policies all through the Security Operations neighborhood. Sigma Guidelines are an open up-supply community task that was began a few yrs in the past as a way to build a prevalent language to be applied in just security functions for SIEM and EDR queries. This enables security operations groups to generate queries in the Sigma rule structure as a substitute of vendor-particular SIEM languages.
I know what you may be contemplating “perfectly that is fantastic that the community is coming jointly to assistance every other out in their each day cybersecurity battles.” But, I use a unique SIEM than whoever wrote this sigma rule or that sigma rule. That is the beauty of the standardization of Sigma Regulations. They’re intended for all people. Just take this instance under of a query in a well-liked SIEM software that is looking for “Very clear command background” – an evasion tactic utilized in Linux.
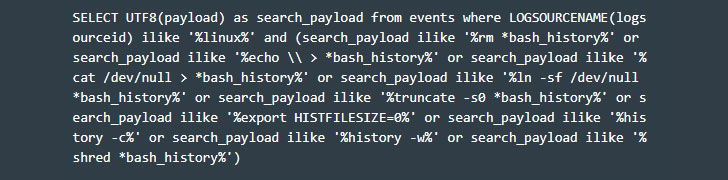
That is particular to that SIEM tool’s language.
Now take a look at a next SIEM’s language for that identical question.
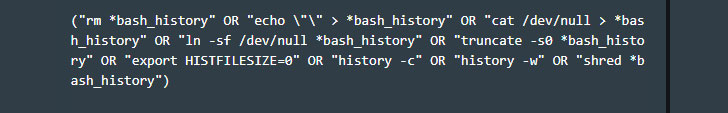
As you can see, two quite various lookups on two distinct SIEM devices will return the correct exact output, derived from the similar sigma rule. So, if you are like me and are asking the issue in your head, “Do I have to understand a new tool’s language to be in a position to take gain of Sigma Rules?” – the solution is NO. These queries came from the exact very same sigma rule. I took this sigma rule and employed a sigma rule converter this kind of as the just one at https://uncoder.io and just did a simple translate.
As of correct now, 25 diverse translations can be produced, which include Grep and PowerShell, two native look for procedures on Linux and Windows. The particulars of a sigma rule are uncomplicated as perfectly.
Each rule must include a title, log source, detection, and issue, and inside of each and every of the earlier essential fields, a variety of optional fields can be produced. Collaboration extends additional with Sigma guidelines: risk intelligence feeds, Breach and Attack Simulations (BAS), and other security validation technologies make it less complicated to sharpen your Security Operations to take care of the never ever-ending security alerts much better.
Today, every single Security Functions crew collects log information and produces customized queries for their working day-to-working day assessment. We all know we are understaffed and in excess of-labored. For people two factors on your own, as a greater community that is charged with defending versus cyberattacks, it is a will have to for the group at substantial to adopt Sigma Principles. Start out the sigma revolution and be component of the birth of a common. Sigma was born to be an open up typical for everyone to use no make a difference the SIEM and no subject the query.
Up until finally now, SIEM functions has genuinely been an island unto alone. No longer is this genuine. Community-dependent Security Operations specifications are below to keep, which is why I really like sigma policies.
For much more facts, stop by www.cymulate.com and sign-up for a Cost-free Demo.
Observed this write-up exciting? Follow THN on Fb, Twitter and LinkedIn to read much more special content we write-up.
Some components of this post are sourced from:
thehackernews.com


 FTC: #COVID19 Helped Double Identity Theft in 2020
FTC: #COVID19 Helped Double Identity Theft in 2020