A destructive web shell deployed on Windows systems by leveraging a previously undisclosed zero-day in SolarWinds’ Orion network monitoring computer software could have been the do the job of a feasible Chinese danger group.
In a report printed by Secureworks on Monday, the cybersecurity business attributed the intrusions to a risk actor it calls Spiral.
Back on December 22, 2020, Microsoft disclosed that a 2nd espionage team may possibly have been abusing the IT infrastructure provider’s Orion application to drop a persistent backdoor known as Supernova on goal units.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
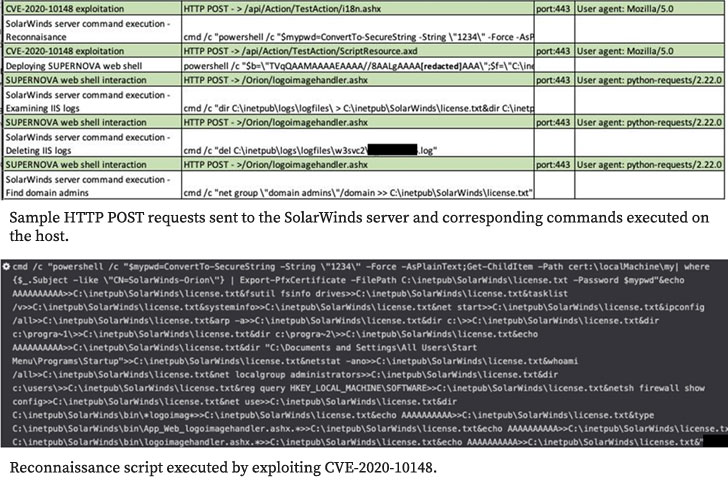
The conclusions have been also corroborated by cybersecurity firms Palo Alto Networks’ Unit 42 danger intelligence group and GuidePoint Security, the two of whom described Supernova as a .NET web shell executed by modifying an “app_web_logoimagehandler.ashx.b6031896.dll” module of the SolarWinds Orion application.
The alterations had been built feasible not by breaching the SolarWinds application update infrastructure but as a substitute by leveraging an authentication bypass vulnerability in the Orion API tracked as CVE-2020-10148, in transform permitting a distant attacker to execute unauthenticated API commands.
“Not like Solorigate [aka Sunburst], this destructive DLL does not have a electronic signature, which indicates that this might be unrelated to the source chain compromise,” Microsoft experienced famous.
Whilst the Sunburst campaign has due to the fact been formally linked to Russia, the origins of Supernova remained a secret until eventually now.
According to Secureworks Counter Risk Device (CTU) researchers — who found the malware in November 2020 while responding to a hack in one of its customers’ networks — “the rapid and specific character of the lateral motion suggests that Spiral had prior knowledge of the network.”
For the duration of the study course of further investigation, the business claimed it uncovered similarities in between the incident and that of a prior intrusion action on the very same network uncovered in August 2020, which experienced been accomplished by exploiting a vulnerability in a products identified as ManageEngine ServiceDesk as early as 2018.
“CTU researchers were to begin with unable to attribute the August action to any identified threat teams,” the scientists mentioned. “Nonetheless, the subsequent similarities to the Spiral intrusion in late 2020 advise that the Spiral threat group was dependable for both equally intrusions.”
The relationship to China stems from the actuality that attacks concentrating on ManageEngine servers have prolonged been linked with risk teams situated in the nation, not to mention the modus operandi of exploiting extended-time period persistence to gather qualifications, exfiltrate sensitive info, and plunder mental assets.
But much more good evidence arrived in the variety of an IP address that geolocated to China, which the researchers said came from a host that was made use of by the attackers to run Secureworks’s endpoint detection and reaction (EDR) computer software for motives ideal identified to the danger actor, suggesting the computer software may perhaps have been stolen from the compromised client.
“The threat team very likely downloaded the endpoint agent installer from the network and executed it on the attacker-managed infrastructure,” the scientists in-depth. “The exposure of the IP address was very likely unintentional, so its geolocation supports the hypothesis that the Spiral threat team operates out of China.”
It truly is well worth pointing out that SolarWinds dealt with Supernova in an update to Orion Platform launched on December 23, 2020.
Uncovered this post attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to go through a lot more exclusive content material we article.
Some areas of this post are sourced from:
thehackernews.com


 Microsoft Exchange Hackers Also Breached European Banking Authority
Microsoft Exchange Hackers Also Breached European Banking Authority