Network security business SonicWall has dealt with a critical security vulnerability influencing its Secure Cellular Access (SMA) 100 sequence appliances that can allow distant, unauthenticated attackers to achieve administrator access on focused equipment remotely.
Tracked as CVE-2021-20034, the arbitrary file deletion flaw is rated 9.1 out of a greatest of 10 on the CVSS scoring procedure, and could allow an adversary to bypass path traversal checks and delete any file, resulting in the gadgets to reboot to manufacturing unit default settings.
“The vulnerability is due to an improper limitation of a file path to a limited listing perhaps main to arbitrary file deletion as ‘nobody,'” the San Jose-centered agency noted in an advisory released Thursday. “There is no proof that this vulnerability is remaining exploited in the wild.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
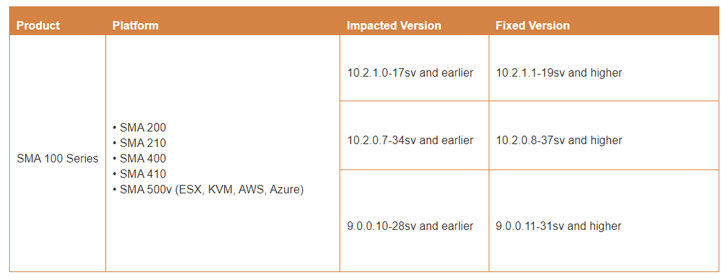
SonicWall credited Wenxu Yin of Alpha Lab, Qihoo 360, with reporting the security shortcoming, which impacts SMA 100 Series — SMA 200, SMA 210, SMA 400, SMA 410, and SMA 500v — running the next versions:
- 9…10-28sv and before
- 10.2..7-34sv and earlier
- 10.2.1.-17sv and previously

Specified that there are no workarounds to remediate the attack vector and SonicWall products have become a valuable target for threat actors to deploy ransomware in modern months, clients are recommended to apply applicable patches as shortly as doable to mitigate any potential exploitation risk.
Located this report intriguing? Comply with THN on Fb, Twitter and LinkedIn to go through more exclusive articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 A New APT Hacker Group Spying On Hotels and Governments Worldwide
A New APT Hacker Group Spying On Hotels and Governments Worldwide