These days AI looks to be just about everywhere, and Sophos Intercept X proudly exploits it to assist discover unknown malware. It also blocks ransomware attacks working with behavioral analysis, and supplies equipment to look into possible threats to see how and why they happened.
This may perhaps seem sophisticated, but everything is rolled neatly into a one web portal for simple access. You can also pick and pick which attributes you want: alongside with conventional workstation and notebook guidance, independent modules are accessible for protecting servers and cell products. If you only require main protection products and services then you can go for the Intercept X Essentials subscription, but we trialled the Intercept X State-of-the-art company, which adds aid for several security procedures, software and web protection and product controls.
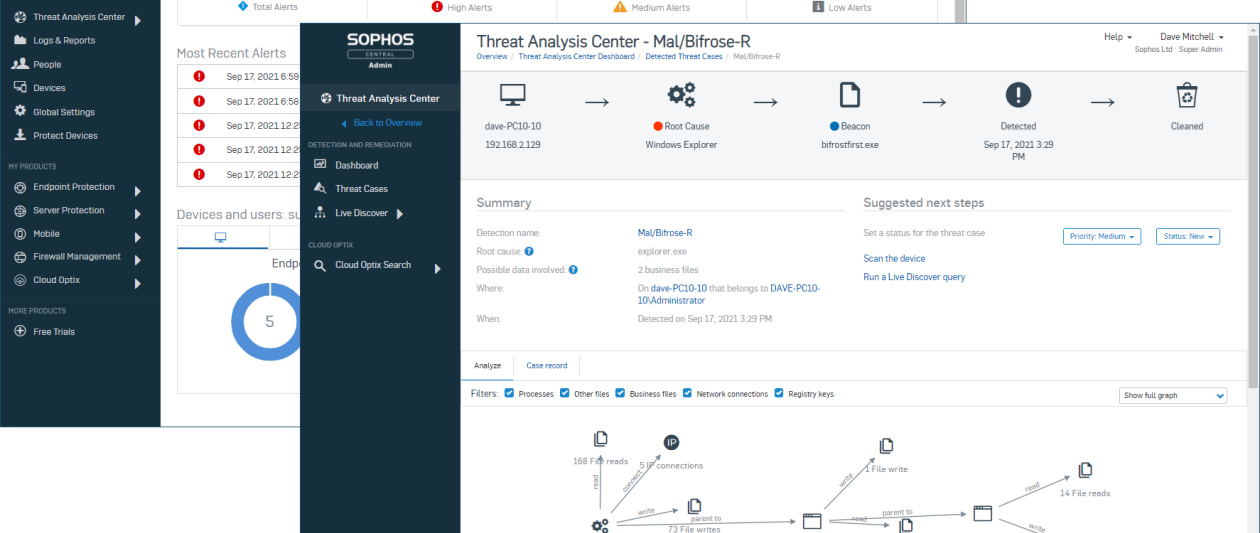
An Sophisticated subscription also allows the risk examination centre, wherever you can review attacks and investigate occasion chain diagrams, which observe how a malware incident unfolded, such as facts of which processes and documents had been accessed. If you’ve gone for the optional XDR (prolonged detection and reaction) licence, you can also make use of the Are living Explore function, which uses SQL queries to develop comprehensive studies for selected endpoints – as properly as furnishing obtain to the Sophos Info Lake, exactly where you can retail outlet up to 30 days of report data in the cloud.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
All of this is administered from the Sophos Central portal (which also normally takes care of any Sophos firewalls in your enterprise). The primary dashboard exhibits recent alerts, a summary of units and end users and specifics on how web entry controls are accomplishing.
Deploying the client software package is reasonably uncomplicated. You can make end users in the portal and email them a connection to put in the agent, or you can install the Mac and Windows application from a central distribution point like any frequent application. Either way, the agent takes around 10 minutes to absolutely install security then begins instantly, with the agent choosing up a foundation set of security procedures from your portal account. These can be system-certain or, if you use the Sophos Active Listing sync software or Azure sync support to import buyers and groups, you can make guidelines that observe users no matter of which product they are logged into.
When it arrives to customising your guidelines, there’s a huge range of possibilities to decide on from. The base insurance policies for web, software and unit controls can be tweaked to your tastes, or you can generate new kinds. Data-reduction avoidance guidelines established policies that avert specified styles of information and facts from currently being copied or transferred we examined this with a policy that appeared for files made up of payment information and facts and located it worked beautifully, blocking all attempts to share a text file made up of credit score card figures.
The CryptoGuard element, meanwhile, neuters ransomware by checking all file writes when a method tries to overwrite an current file, a short term cleanse duplicate is cached on the area drive. The software then analyses the updated file, and if it decides that it’s been maliciously encrypted, it immediately restores the primary cached duplicate of the file.
All of these options can be configured and customised, but if you want to keep items straightforward you can just allow the AI-driven Deep Studying service, tick the “recommended settings” box and leave the rest up to the program.
SMBs that want a large-ranging security solution will need look no further more than Sophos Intercept X. It is loaded with powerful functions, still remains uncomplicated to use and uncomplicated to manage from the Sophos Central cloud portal.
Some elements of this short article are sourced from:
www.itpro.co.uk

 Panasonic Suffers Data Breach After Hackers Hack Into Its Network
Panasonic Suffers Data Breach After Hackers Hack Into Its Network