Cybersecurity corporations Sophos and ReversingLabs on Monday jointly launched the very first-at any time production-scale malware investigate dataset to be built readily available to the normal general public that aims to make efficient defenses and push sector-huge enhancements in security detection and reaction.
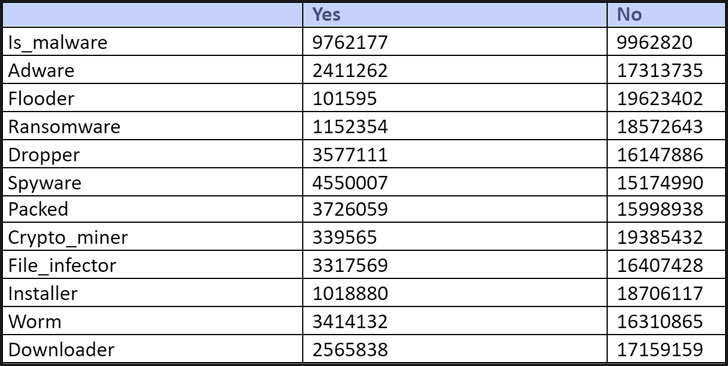
“SoReL-20M” (small for Sophos-ReversingLabs – 20 Million), as it is really called, is a dataset containing metadata, labels, and functions for 20 million Windows Moveable Executable (.PE) information, which include 10 million disarmed malware samples, with the purpose of devising equipment-finding out techniques for much better malware detection abilities.
“Open up expertise and knowledge about cyber threats also sales opportunities to extra predictive cybersecurity,” Sophos AI group explained. “Defenders will be in a position to anticipate what attackers are accomplishing and be far better organized for their following transfer.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Accompanying the release are a established of PyTorch and LightGBM-centered machine finding out products pre-skilled on this details as baselines.
Compared with other fields these as all-natural language and picture processing, which have benefitted from vast publicly-out there datasets this kind of as MNIST, ImageNet, CIFAR-10, IMDB Evaluations, Sentiment140, and WordNet, acquiring maintain of standardized labeled datasets devoted to cybersecurity has proved difficult because of the existence of personally identifiable facts, delicate network infrastructure information, and non-public mental house, not to mention the risk of furnishing destructive application to unknown third-get-togethers.
Although EMBER (aka Endgame Malware BEnchmark for Study) was unveiled in 2018 as an open-source malware classifier, its more compact sample sizing (1.1 million samples) and its operate as a one-label dataset (benign/malware) intended it “limit[ed] the variety of experimentation that can be performed with it.”
SoReL-20M aims to get around these issues with 20 million PE samples, which also involves 10 million disarmed malware samples (individuals are unable to be executed), as properly as extracted attributes and metadata for an supplemental 10 million benign samples.
Furthermore, the tactic leverages a deep understanding-dependent tagging product educated to crank out human-interpretable semantic descriptions specifying significant attributes of the samples involved.
The release of SoReL-20M follows identical business initiatives in modern months, including that of a coalition led by Microsoft, which introduced the Adversarial ML Risk Matrix in October to aid security analysts detect, react to, and remediate adversarial attacks in opposition to equipment discovering programs.
“The thought of danger intelligence sharing in security just isn’t new but is much more critical than ever given the innovation menace actors have revealed around the past many yrs,” ReversingLabs researchers claimed. “Machine finding out and AI have turn out to be central to these attempts enabling menace hunters and SOC teams to shift over and above signatures and heuristics and develop into extra proactive in detecting new or qualified malware.”
Discovered this article appealing? Follow THN on Fb, Twitter and LinkedIn to study additional special information we submit.
Some components of this post are sourced from:
thehackernews.com

 Google Cloud Hires Goldman Sachs Man as First CISO
Google Cloud Hires Goldman Sachs Man as First CISO