U.S. Supreme Court Chief Justice John Roberts and Supreme Court Justice Elena Kagan go to the State of the Union handle in the chamber of the U.S. House of Reps on February 04, 2020 in Washington, DC. The Supreme Court docket on Monday listened to oral arguments in Van Buren v. United States, a personal computer crimes case whose verdict could drastically broaden or slender the scope of the Computer system Fraud and Abuse Act. (Mario Tama/Getty Photographs)
The Supreme Courtroom on Monday read oral arguments in Van Buren v. United States, a laptop crimes circumstance whose verdict could significantly broaden or slim the scope of the Computer system Fraud and Abuse Act (CFAA), such as no matter whether associates of the moral hacking group could facial area federal penalties.
The substantial court’s future ruling may perhaps ultimately hinge on regardless of whether the justices concur with the U.S.’s interpretation of the statute – specifically how it defines when a human being has criminally exceeded authorized obtain to a pc method, web page or app. In that regard, numerous justices on equally sides of the ideological spectrum expressed doubt or confusion with regards to the federal government’s stance.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The scenario centers all around the conviction of Nathan Van Buren, a police officer in Georgia who, in exchange for a bribe, employed his accessibility to a legislation enforcement database to seem up license plate info for an acquaintance. Whilst Van Buren was authorized to obtain the databases, he was charged with laptop or computer fraud below CFAA simply because his steps ended up outdoors the purview of his job.
Cybersecurity professionals and electronic legal rights companies claim the statute, passed in 1986, is outdated, and fear that bug hunters and pen testers could be billed if their analysis into techniques are deemed extreme, even if they actions are intended to be ethical.
“These regulations weren’t even created with the strategy of a fantastic faith hacker in brain. That didn’t really exist at that position in time,” claimed Casey Ellis, chief technology officer, founder and chairman of Bugcrowd. Ellis reported that making law that specifies what steps on a computer system program are unlawful is “inherently ambiguous… as laptop techniques get far more complicated, so the idea of broadening matters out to accommodate all of that ends up in this position exactly where a total bunch of factors conclude up getting a criminal offense that should not be.”
Jeffrey Fisher, the lawyer who is pleasing the 11th Circuit of Appeals’ selection to uphold Van Buren’s conviction, argued in advance of the courtroom that even employees and shoppers could conceivably be prosecuted for disregarding published or verbal recommendations for how to interact with a distinct internet site or laptop or computer technique.
In his opening argument, Fisher explained that the U.S. government’s interpretation of the CFAA “would brand most American criminals on a each day basis,” which include staff members who may well use their corporate laptops for individual enterprise versus their employer’s instructions. He stated the law’s wording have to not be considered in this kind of a way as to “transform the CFAA into a sweeping police mandate.”
Neither Fisher nor any of the justices particularly cited the law’s prospective affect on cybersecurity researchers or vulnerability disclosure programs, but Fisher did warn of the CFAA’s prospective chilling influence – a single that could surely use to cyber scientists: “The language of this statute has its very own deterrent effect… For folks who use the internet just about every day, they have to be knowledgeable of the criminal regulation,” explained Fisher. “And don’t forget: this status has a civil element.”
Opposing counsel Eric Feigin, assistant to the U.S. solicitor common, prompt Fisher was imagining worst-situation scenarios in which prosecutors applied and enforced the CFAA considerably far too broadly. “He’s trotting out this parade of horribles and telling you the only way to avoid it is to interpret [the act’s] language – which I believe is pretty clear – in his way, as a way that would get rid of all of the privacy security that the statute provides,” he reported.
Nonetheless, some justices seemed dubious of Feigin’s assert that the CFAA’s language implicitly imposes constraints that would preclude legal or civil fees in several other cases.
So much rides on definition of “so”
The CFAA defines “exceeds approved access” as “to accessibility a computer system with authorization and to use this kind of obtain to obtain or change info in the laptop or computer that the accesser is not entitled so to obtain or alter.” Fisher asserted that this suggests it is illegal for authorized process consumers to acquire or change details only if they are in no way entitled to stated details. But the U.S. argues that the inclusion of the term “so” in that sentence means that persons are committing laptop or computer fraud even if they are accessing information they are generally entitled to, but are executing so outside of their mentioned terms of usage.
Dawn Mertineit, a lover in the law firm Seyfarth Shaw who procedures in the firm’s Trade Secrets, Computer Fraud and Non-Competes group, called the government’s rationalization of the phrase “so” as “muddled and to some degree tortured,” incorporating that the U.S. would “likely have an uphill battle convincing the court that the [current language supports] the broad interpretation of ‘exceeds authorized accessibility.’”
“You would concede, would not you, that if the word ‘so’ was not there, you would reduce this circumstance?” requested Justice Elena Kagan to Feign.
“I think it would be a considerably more durable case for us without the phrase ‘so’ your honor,” he replied.
Attempting to quell fears of prosecutorial overreach, Feigin also contended that CFAA’s “exceeds authorized access” language doesn’t utilize to persons who violate websites’ terms of products and services by, for instance, registering them selves with untrue private information and facts.
A community web-site “is not a procedure that needs authorization,” explained Feigin. “It’s not one particular that employs needed credentials that mirror some distinct, individualized consideration.” Also, he extra, “services like Facebook and Hotmail that will give accounts to any individual who have a pulse – and even people who never simply because they really don’t seriously check out – thoses aren’t authorization-based techniques, and I feel that slender indicating makes a terrific deal of perception in this statute.”
“What Congress was aiming at” when referring to authorization, Feigin posited, “was people today who ended up especially reliable. Individuals akin to workforce – the type of individual that has truly been especially thought of and independently licensed.”
If the U.S.’s recommended definition of “authorization” is without a doubt akin to work, then a vulnerability researcher or bug hunter working beneath agreement or as part of a bug bounty software could theoretically be accused of exceeding authorized obtain if his or her operate was to be considered out of bounds.
Justice Stephen Breyer also questioned Feigin whether or not employees who are issued company-provisioned function desktops are thought of separately authorized. Feigin acknowledged that they are, but argued that they would nevertheless be protected from CFAA expenses by the more narrowing phrase “use such obtain.” Feigin claimed the act’s language implies that licensed persons are only in violation of the act if they demonstrably abuse their privileged access to obtain or change information that would usually be complicated to entry.
“So if you choose to [use your work computer to] deliver an e-mail to your friend about when you’re likely to have lunch collectively, and that’s one thing you could do from your phone, there’s almost nothing specific about applying the access” that warrants fees, even though you may perhaps have technically violated organization coverage, he said.
But some justices expressed skepticism of Feigin’s implied definitions. “My dilemma is that you are providing definitions that slim the statute that the statute does not have,” stated Sotomayor. “You’re asking us to publish definitions to narrow what could if not be considered as a quite wide statute, and dangerously obscure.”
Additionally, Chief Justice John Roberts explained to Feigin, “I really don’t understand your focus on authorization as a limiting phrase.” And Justice Amy Coney Barrett advised Feigin that he was “attributing an dreadful whole lot of specificity to authorization that it does not have.”
Barrett did nevertheless, also query Fisher’s interpretation of authorization, questioning why authorization should be looked at simply just as a black-and-white “on-off switch,” utilizing the metaphor of a babysitter who was provided keys to the parents’ vehicle “but utilizes the vehicle to operate individual errands.”
“Doesn’t the concept of entitlement or authorization alone have a scope part?” she asked Fisher, who in convert replied that in this certain statute, scope or objective was not carved out by Congress.
A case of federal overreach?
Numerous justices also expressed problems over the probable privacy ramifications of approved people today getting knowledge outside the house the scope of the usual employment, as Van Buren did. Justice Clarence Thomas, for occasion, requested about a automobile rental firm worker who employs GPS information not to find a lacking vehicle but to stalk a partner, while Justice Samuel Alito envisioned a state of affairs in which a bank’s fraud department employee marketed credit history card numbers for financial gain.
“Do you believe that none of that was of worry when Congress enacted this statute?” requested Alito.
“I do not feel it was,” reported Fisher. “What Congress was worried about was computer hacking, and that is up and down the legislative history – this new issue [in 1986] of personal computer of hacking.” Fisher acknowledged that Congress may desire to further amend the CFAA to specially deal with Thomas’s and Alito’s examples, but under the law’s present language, there’s no way to criminalize these kinds of malicious steps without also criminalizing “every other everyday worker who violates an personnel handbook.”
Fisher also mentioned this kind of actions usually currently represent crimes that can be prosecuted under other federal and state legislation – just not CFAA.
In fact, Justice Neil Gorsuch said with regards to the U.S. government’s “reverse parade of horribles” in which lots of laptop or computer crimes go unpunished, “I’m struggling to picture how long that parade would be given the abundance of legal guidelines out there.”
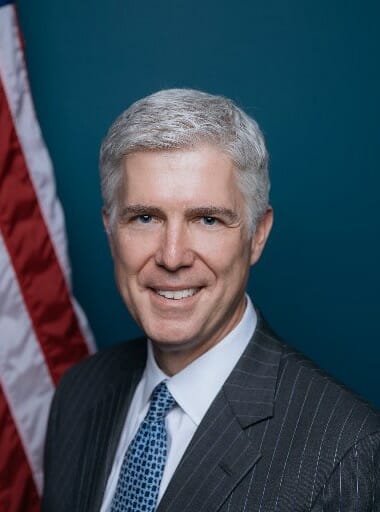 Supreme Court Justice Neil Gorsuch (The White House, Community domain, through Wikimedia Commons).
Supreme Court Justice Neil Gorsuch (The White House, Community domain, through Wikimedia Commons).
Gorsuch in certain reserved sharp criticism for the government’s use of CFAA in the Van Buren scenario, noting a “long line of scenarios in current years exactly where the federal government has constantly sought to increase prison jurisdictional in really major contestable ways that this courtroom has rejected.”
“And I’m just kind of curious why we’re back below all over again on a relatively small point out crime that is prosecutable beneath state law and perhaps less than other federal legislation,” Gorsuch ongoing, including that the CFAA’s language could be “making a federal criminal of us all.”
“I would have believed that the solicitor general’s business isn’t just a rubber stamp from the U.S. attorney’s workplaces and that there would be some thorough thought specified as to irrespective of whether this is really an ideal looking at of these statutes,” Gorsuch said.
Feigin held organization, however, insisting that the US will not be prosecuting an unlimited quantity of scenarios below this statute. He accused Fisher of creating an “imaginary avalanche of hypothetical prosecutions” though staying not able to cite reputable examples of past CFAA prosecutorial overreaches.
But citing Marinello v United States, Fisher reminded the court docket that “you just can’t construe a statute only on the assumption that the government will use it responsibly” in the long run.
Ellis from Bugcrowd reported that government’s logic “assumes that everyone’s working in fantastic religion, and has alignment around intent in the scenario of security research that’s becoming performed in the interests of making a technique safer for consumers, but that requires passing data to an firm that could not necessarily want to listen to it or may well even have a record of responding negatively to that variety of factor.” In fact claimed Ellis, CFAA has at periods been utilised as a deterrent by application builders and other companies to discourage research that may expose vulnerabilities.
Andy Baer, technology, privacy and info security chair at the law firm Cozen O’Connor, agreed, noting that the CFAA “in recent decades has progressed into a weapon which website operators wield versus facts scrapers who crawl their web pages in violation of the phrases of use and corporations use in opposition to personnel who accessibility corporate computer system units to attain private information to just take with them to competitors.”
Requested by Gorsuch if he was basing his arguments on any constitutional grounds, Fisher referenced violation of the honest discover doctrine because of to the law’s “impossible vagueness” and ambiguity in phrases of what actions are conceivably punishable. For this purpose, Fisher argued that the court should lean on the rule of lenity, which requires the court, when a prison legislation is deemed ambiguous, to rule in a method that is most favorable to the defendant even though still honoring legislative intent.
Legislative history also performed a crucial purpose in the arguments, as several justices famous that the CFAA was launched as an amendment to an earlier regulation that had at first involved language explicitly making it a criminal offense to use one’s licensed computer system accessibility for unintended applications.
Even so, Fisher famous that this individual provision used only to federal employees at the time, and when Congress afterwards “expanded the statute eventually to address all computer systems, essentially, in the United States, it also did, at the very same time, clear away that murky ground of liability” by eradicating these kinds of language “because it was not… the core of the statutory issue.”
Feigin argued that CFAA’s heritage must be taken less than thought when interpreting the latest legislation, and insisted that the illegality of inappropriate use is even now implied by the statute. But Fisher stated it was “very dangerous to rely on legislative historical past to resolve ambiguity,” noting that the wording was eliminated for a cause.
The justices in this circumstance ended up also knowledgeable by a amount of amicus briefs, which include 1 from the Digital Frontier Foundation, the Heart for Democracy & Technology, Bugcrowd, Swift7, Scythe, Tenable and a consortium of laptop security researchers, who collectively emphasized the critical mother nature of vulnerability exploration and disclosure, and urged the court “to adopt a narrow building of the law regular with Congress’s intent and to explain that contravening penned prohibitions on means of entry is not a violation of the CFAA.”
Conversely, the Electronic Privacy Facts Centre (EPIC) and 15 technical experts submitted their individual temporary arguing that Van Buren’s steps constituted a important invasion of privacy – exactly what the CFAA is meant to shield from. “The CFAA safeguards sensitive personal knowledge and should be interpreted consistent with that reason,” the short states. “We want the CFAA, now much more than at any time, to be an more check out from abuse by the people today entrusted to accessibility sensitive info and systems.”
“I discover this a really complicated scenario to determine based on the briefs that we have been given,” admitted Alito, acknowledging both of those “concerns about the outcome on… personal privacy of adopting Mr. Fisher’s proposed interpretation” as nicely as fears that adopting [the United States’s CFAA] interpretation would criminalize all sorts of action that folks regard as mostly innocuous.”
The Supreme Courtroom has right up until June 2021 to issue a verdict on the situation.
Some parts of this short article are sourced from:
www.scmagazine.com


 Electronic Medical Records Cracked Open by OpenClinic Bugs
Electronic Medical Records Cracked Open by OpenClinic Bugs