A suspected Iranian danger exercise cluster has been connected to attacks aimed at Israeli shipping and delivery, governing administration, strength, and healthcare organizations as aspect of an espionage-concentrated campaign that commenced in late 2020.
Cybersecurity firm Mandiant is monitoring the team below its uncategorized moniker UNC3890, which is thought to perform functions that align with Iranian passions.
“The gathered knowledge may perhaps be leveraged to aid several pursuits, from hack-and-leak, to enabling kinetic warfare attacks like individuals that have plagued the shipping field in recent many years,” the company’s Israel Exploration Crew pointed out.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

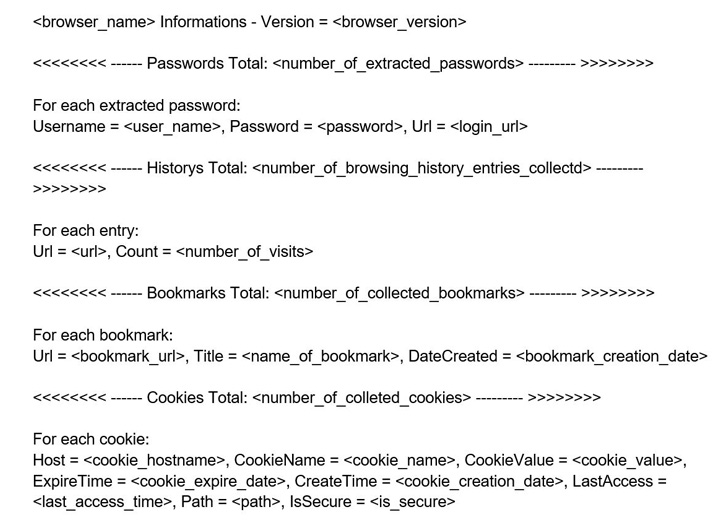
Intrusions mounted by the team lead to the deployment of two proprietary pieces of malware: a “compact but efficient” backdoor named SUGARUSH and a browser credential stealer called SUGARDUMP that exfiltrates password details to an email tackle related with Gmail, ProtonMail, Yahoo, and Yandex.
Also used is a network of command-and-management (C2) servers that host fake login internet pages impersonating authentic platforms these as Workplace 365, LinkedIn, and Fb that are designed to converse with the targets as properly as a watering gap which is considered to have singled out the shipping sector.
The watering gap, as of November 2021, was hosted on a login website page of a genuine Israeli transport corporation, Mandiant pointed out, introducing the malware transmitted preliminary details about the logged-in user to an attacker-managed domain.
Though the actual methodology for original access stays unknown, it’s suspected to involve a combine of watering holes, credential harvesting by masquerading as reputable services, and fraudulent job presents for a software package developer posture at a information analytics business LexisNexis.
“A person of UNC3890’s most the latest endeavors to concentrate on victims consists of the usage of a online video professional for AI-based mostly robotic dolls, employed as a entice to produce SUGARDUMP,” the scientists mentioned.

SUGARUSH, the 2nd bespoke malware, works by establishing a relationship with an embedded C2 server to execute arbitrary CMD instructions issued by the attacker, granting the adversary comprehensive regulate about the victim’s environment on getting first entry.
Other instruments made use of by UNC3890 include the Metasploit penetration tests application and Unicorn, a publicly offered utility for conducting a PowerShell downgrade attack and injecting shellcode into memory.
The group’s connections to Iran stem from the use of Farsi language artifacts in the most recent version of SUGARDUMP, the steady targeting of Israeli entities that dovetails with other Iranian menace actor clusters, and the usage of the NorthStar C2 Framework.
Found this short article interesting? Stick to THN on Facebook, Twitter and LinkedIn to read more exceptional information we submit.
Some areas of this write-up are sourced from:
thehackernews.com


 Escape the ransomware maze
Escape the ransomware maze