Cybersecurity scientists have presented perception into a beforehand undocumented program regulate panel utilized by a fiscally inspired danger team acknowledged as TA505.
“The group usually modifications its malware attack strategies in response to global cybercrime traits,” Swiss cybersecurity firm PRODAFT mentioned in a report shared with The Hacker Information. “It opportunistically adopts new technologies in get to acquire leverage more than victims in advance of the wider cybersecurity sector catches on.”
Also tracked beneath the names Evil Corp, Gold Drake, Dudear, Indrik Spider, and SectorJ04, TA505 is an intense Russian cybercrime syndicate driving the notorious Dridex banking trojan and which has been connected to a quantity of ransomware strategies in new many years.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

It is also said to be connected to the Raspberry Robin attacks that emerged in September 2021, with similarities uncovered among the malware and Dridex.
Other notable malware households associated with the group consist of FlawedAmmyy, Neutrino botnet, and a backdoor codenamed ServHelper, one variant of which is capable of downloading a distant obtain trojan termed FlawedGrace.
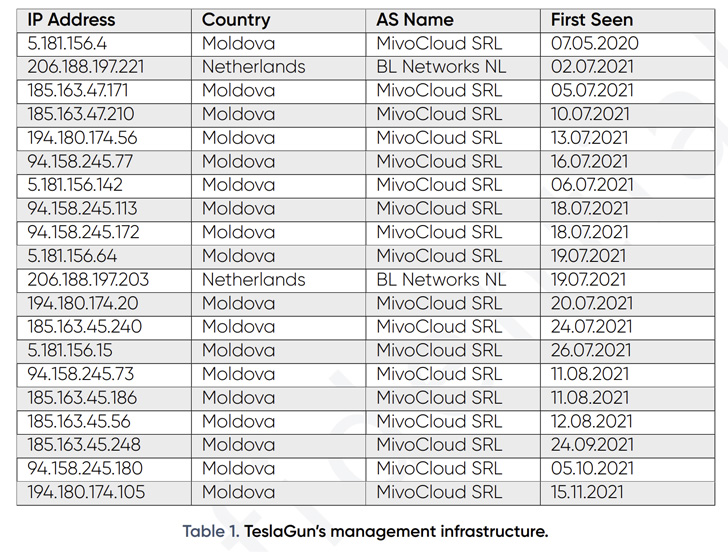
The command panel, known as TeslaGun, is mentioned to be utilised by the adversary to deal with the ServHelper implant, functioning as a command-and-regulate (C2) framework to commandeer the compromised machines.
On top of that, the panel offers the capability for the attackers to issue instructions, not to point out mail a single command to all target equipment in go or configure the panel this kind of that a predefined command is routinely run when a new target is additional to the panel.
“The TeslaGun panel has a pragmatic, minimalist style. The main dashboard only contains contaminated victim data, a generic remark section for each individual victim, and quite a few solutions for filtering sufferer data,” the researchers claimed.
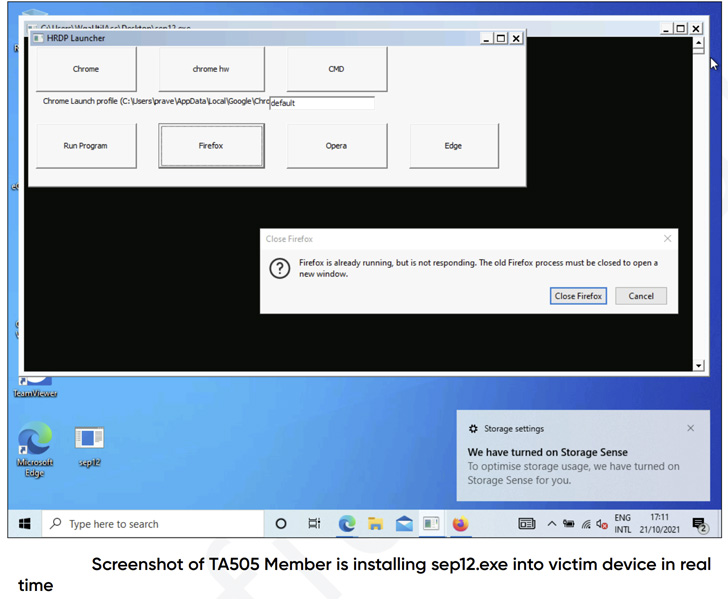
Apart from using the panel, the menace actors are also identified to hire a distant desktop protocol (RDP) software to manually hook up to the focused units by using RDP tunnels.
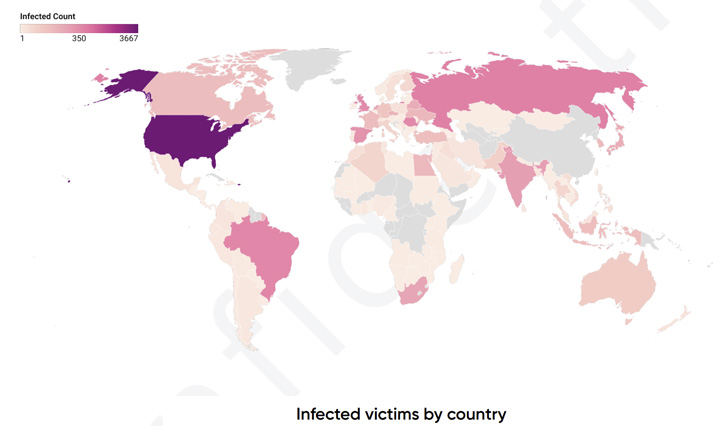
PRODAFT’s assessment of TeslaGun sufferer details reveals that the group’s phishing and targeted strategies have hit at least 8,160 targets since July 2020. A greater part of these victims are located in the U.S. (3,667), followed by Russia (647), Brazil (483), Romania (444), and the U.K. (359).

“It is clear that TA505 is actively on the lookout for on line banking or retail customers, which include crypto-wallets and e-commerce accounts,” the scientists mentioned, citing responses made by the adversarial group in the TeslaGun panel.
The conclusions also arrive as the U.S. Division of Well being and Human Companies (HHS) warned of considerable threats posed by the group to the overall health sector by way of data exfiltration attacks that purpose to steal intellectual property and ransomware operations.
“Evil Corp has a huge established of hugely-capable instruments at their disposal,” the agency’s Well being Sector Cybersecurity Coordination Center (HC3) stated in an advisory published late final thirty day period.
“These are created and taken care of in-house, but are often applied in conjunction with commodity malware, living-off-the-land procedures and typical security tools that were being developed for genuine and lawful security assessments.”
Discovered this post appealing? Stick to THN on Facebook, Twitter and LinkedIn to go through far more unique material we submit.
Some pieces of this posting are sourced from:
thehackernews.com


 TikTok refutes allegations of a massive security breach
TikTok refutes allegations of a massive security breach