Software program vulnerabilities are a important danger to businesses currently. The value of these threats is significant, equally monetarily and in terms of track record.
Vulnerability management and patching can easily get out of hand when the number of vulnerabilities in your business is in the thousands and tracked in inefficient approaches, this sort of as using Excel spreadsheets or many reports, specifically when numerous groups are concerned in the group.
Even when a procedure for patching is in area, organizations nevertheless struggle to properly patch vulnerabilities in their property. This is frequently for the reason that teams seem at the severity of vulnerabilities and are inclined to apply patches to vulnerabilities in the next severity get: critical > high > medium > reduced > information. The pursuing sections make clear why this technique is flawed and how it can be enhanced.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Why is Patching Complicated?
Whilst it is effectively known that vulnerability patching is exceptionally essential, it is also challenging to patch vulnerabilities successfully. Vulnerabilities can be described from sources this kind of as pentest reviews and several scanning applications. Scans can be performed on your web programs, APIs, resource code, infrastructure, dependencies, containers, and many others.
The complete quantity of experiences that require to be sifted as a result of to prioritize patches can raise drastically even in a limited period of time of time, and when many teams are concerned, this can additional maximize the complexity and time essential to coordinate and prioritize patches.
To make issues even worse, new exploits keep on surfacing almost daily, and retaining monitor of new exploits and accessible patches can develop into a mammoth process that can immediately get out of hand if not resolved effectively. Unless of course an group has a pretty mature security plan in position, it is intricate to deal with patching effectively.
Getting the Risk-Based mostly Solution to Patching Vulnerabilities
Simplifying patching calls for you to simplify prioritizing initial. “Risk-based solution” suggests that you’ll weigh the potential impression of a vulnerability versus the chance of its exploitation. This allows you to determine no matter whether or not it’s well worth using motion.
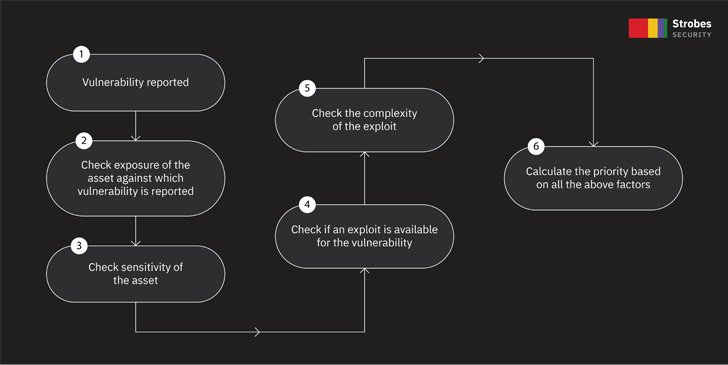
To simplify prioritizing, you have to take into consideration the following items:
- The exposure of the asset,
- The business enterprise sensitivity of the asset,
- The severity of the vulnerability claimed against the asset,
- The availability of an exploit for the vulnerability described,
- The complexity of the exploit, if it is out there,
- The taxonomy of the vulnerability reported.
* Asset could be something within just your organization, like a web application, mobile application, code repository, router, server, databases, and so forth.
 Simplifying Prioritization
Simplifying Prioritization
This method will help in drastically reducing the time put in to prioritize vulnerabilities. Let us go over every stage in element:
Exposure: If your asset is general public-dealing with the Internet, or private, i.e., at the rear of a firewall within just the network with controlled entry. Public property usually carry a larger risk, but that does not usually mean they should really be prioritized. The reason is that not each individual general public asset is sensitive. Some general public assets may merely be static pages that do not include person data, when other community property could be handling payments and PII info. So even if an asset is public, you ought to take into consideration its sensitivity.
Asset sensitivity: Categorize the company sensitivity of all your property based on how vital that asset is to your company. An asset that is made up of sensitive details about users or processes payments may be categorized as a critical small business sensitivity asset. An asset that supplies only some static material can be labeled as an asset with low business enterprise sensitivity.
Severity of the claimed vulnerability: This a person is self-explanatory you have to prioritize vulnerabilities in get of critical > significant > medium > low > details severity.
Exploit availability: Vulnerabilities for which public exploits are currently offered ought to be prioritized in excess of vulnerabilities for which no exploits are obtainable.
Exploit complexity: If an exploit is extremely simple to exploit and involves minor to no user interaction, then vulnerabilities for this form of exploit should really be prioritized more than vulnerabilities with very advanced exploits that generally involve substantial privileges and user conversation.
Taxonomy: The classification of the vulnerability noted also has to be taken into thing to consider and really should be mapped with market standards like OWASP or CWE. An instance would be that a remote code execution impacting a server need to be prioritized bigger than a consumer-facet vulnerability, say a Reflected Cross Web page Scripting.
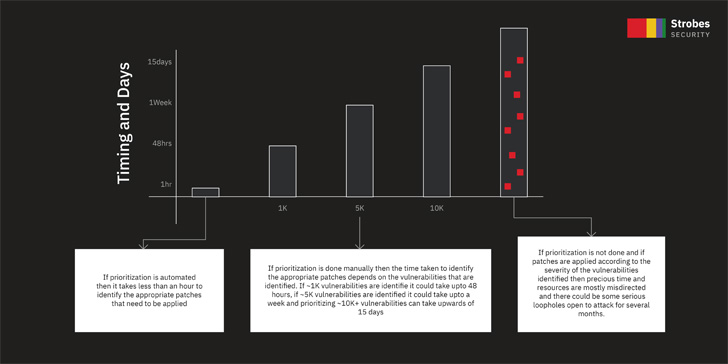 Time invested to prioritize vulnerabilities
Time invested to prioritize vulnerabilities
An example of a large prioritized vulnerability would be if the asset which is afflicted is publicly uncovered, has a critical company sensitivity, the vulnerability severity is critical, an exploit is offered, and does not involve consumer conversation or authentication/privileges.
The moment all vulnerabilities are prioritized, addressing the most critical vulnerabilities will dramatically lessen the risk to your business.
So what issues should a vulnerability administration report measure to assure your software security satisfactorily? – Look at out the Whitepaper.
How to get the info about patches?
You can get data about patches from many advisories like NVD. In these reports, you can locate a number of references on how to patch the vulnerabilities. Also, the web sites of the products and solutions you use ordinarily offer this information and facts. Even though it is achievable to manually go through all the resources and get the information and facts about the patches, if there are a lot of security vulnerabilities in your corporation, obtaining all the information from multiple resources can be tedious.
The Alternative:
Strobes can appreciably help organizations of all sizes drastically decrease the time it can take to prioritize vulnerabilities and provide patching information and facts within just the system. Prioritization is also simple simply because Strobes routinely prioritizes vulnerabilities for you dependent on the metrics explained in the Risk-Dependent Solution to Patching Vulnerabilities portion.
Strobes Security is main the way to disrupt the vulnerability administration area with its flagship solutions VM365 and PTaaS. If you’re not still a Strobes Security’s user, what are you waiting for? Indicator up for totally free right here, or Agenda a demo.
Uncovered this posting interesting? Stick to THN on Fb, Twitter and LinkedIn to read through more exclusive information we article.
Some parts of this short article are sourced from:
thehackernews.com


 No More Ransom Has Helped Over 1.5m Victims
No More Ransom Has Helped Over 1.5m Victims