An evolving phishing marketing campaign noticed at the very least due to the fact May 2020 has been located to concentrate on substantial-position company executives across producing, actual estate, finance, authorities, and technological sectors with the goal of acquiring delicate details.
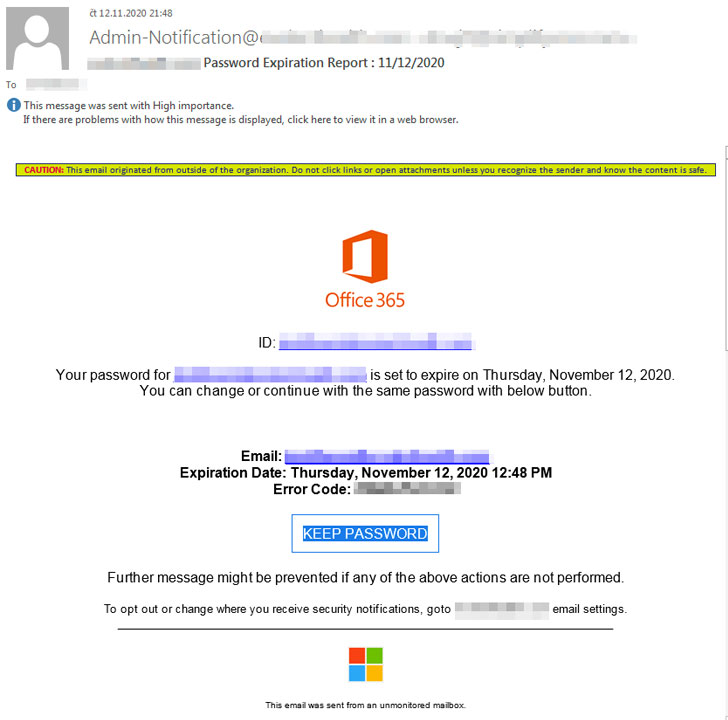
The campaign hinges on a social engineering trick that will involve sending e-mails to prospective victims that contains faux Office environment 365 password expiration notifications as lures. The messages also involve an embedded website link to keep the same password that, when clicked, redirects customers to a phishing site for credential harvesting.
“The attackers focus on significant profile personnel who could not be as technically or cybersecurity savvy, and could be far more probably to be deceived into clicking on malicious one-way links,” Craze Micro researchers reported in a Monday investigation.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“By selectively targeting C-level personnel, the attacker appreciably will increase the price of received credentials as they could lead to even more entry to sensitive own and organizational information, and utilised in other attacks.”
In accordance to the scientists, the specific email addresses were being primarily collected from LinkedIn, although noting that the attackers could have purchased such concentrate on lists from advertising websites that present CEO/CFO email and social media profile info.
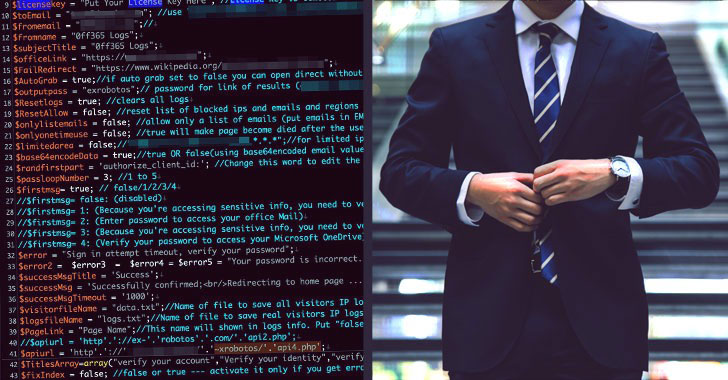
The Workplace 365 phishing package, currently in its fourth iteration (V4), is mentioned to have been at first launched in July 2019, with extra options additional to detect bot scanning or crawling tries and supply different material when bots are detected. Curiously, the alleged developer at the rear of the malware announced V4’s availability on their “business enterprise” Facebook webpage in mid-2020.
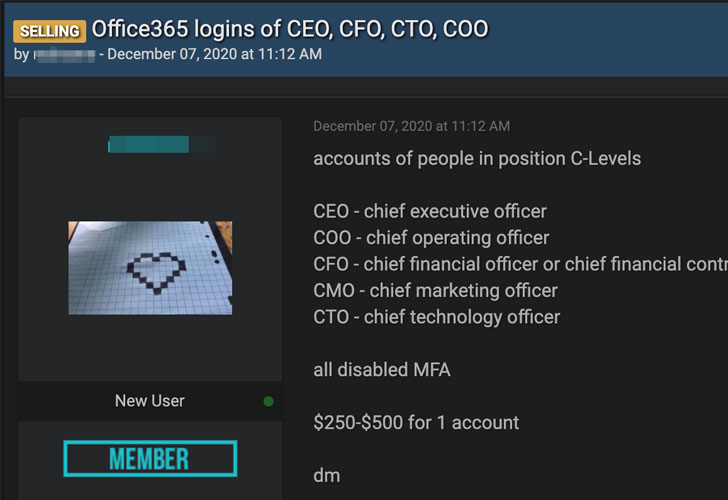
Apart from promoting the phishing package, the actor has also been found to peddle account credentials of CEOs, main economic officers (CFOs), finance department customers, and other significant-profile executives on social media internet pages.
What’s additional, Pattern Micro’s investigation unearthed a attainable url to a consumer cope with on underground boards that was noticed providing a credential harvester tool as well as stolen C-Level account passwords everywhere in between $250 to $500, echoing preceding stories late previous year.
The researchers uncovered at least eight compromised phishing web-sites hosting the V4 phishing package, raising the risk that they ended up applied by different actors for a huge range of phishing strategies directed against CEOs, presidents, board customers, and founders of businesses situated in the U.S., the U.K., Canada, Hungary, the Netherlands, and Israel.
“While companies are conscious and wary of the facts they incorporate in general public-facing websites and platforms, their respective workers need to be continuously reminded to be mindful of the facts they disclose on own pages,” the researchers concluded. “These can be quickly applied versus them for attacks using social engineering approaches.”
Located this short article appealing? Follow THN on Fb, Twitter and LinkedIn to go through extra special written content we publish.
Some pieces of this article are sourced from:
thehackernews.com

 TikTok Flaw Lay Bare Phone Numbers, User IDs For Phishing Attacks
TikTok Flaw Lay Bare Phone Numbers, User IDs For Phishing Attacks