Around the very last several years, there have been various high-profile security breaches. These breaches have underscored the fact that common cyber defenses have grow to be woefully inadequate and that more robust defenses are wanted. As this sort of, lots of companies have transitioned towards a zero trust security model.
A zero believe in security design is based mostly on the strategy that no IT useful resource ought to be dependable implicitly. Prior to the introduction of zero have confidence in security, a user who authenticated into a network was trusted for the length of their session, as was the user’s gadget.
In a zero trust design, a person is no lengthier considered to be honest just mainly because they entered a password at the beginning of their session. As a substitute, the user’s identification is verified via multi-factor authentication, and the user might be prompted to re-authenticate if they try to accessibility means that are significantly delicate or if the person tries to do some thing out of the everyday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
How Complex is it to Implement Zero Have faith in Inside Your Group?
Zero trust security tends to be hard to employ for numerous causes. Very first, zero have confidence in security frequently indicates operating in a vastly unique fashion than what IT and the organization’s customers are employed to. For the IT office, this pretty much normally signifies studying new expertise and supplying up particular privileges. For close-buyers, the transition to zero have confidence in security may mean doing the job in a far far more restrictive ecosystem.
A further thing that tends to make zero trust security complicated to implement is that zero trust could greatest be assumed of as a condition that businesses aspire to attain. There is no item that an business can buy that will quickly changeover the firm into a zero believe in product. Similarly, there is no technique that an corporation can follow to configure their IT sources for zero have faith in. The way in which zero believe in is executed varies extensively from one particular firm to the upcoming.
What varieties of extra security does a zero belief model offer?
Though it is sometimes tempting to believe of the zero belief product as becoming person-centric, zero have confidence in really signifies producing positive that all actions can be validated and that no actions can be done with out the proper validation. Every single zero trust implementation is diverse, but below are quite a few characteristics that are usually provided in zero believe in:
- Multi-factor authentication is expected for all person accounts. In addition, customers may be essential to prove their identities if they remain logged in for an abnormal total of time, attempt to do something unconventional, or consider to accessibility delicate facts.
- Units are validated to be certain that they are not compromised. At a single time, people logged in practically solely from area-joined company desktops that were being hardened by group guidelines and other security mechanisms. Today it is just as typical for a consumer to log in from a particular system. The zero have confidence in product usually focuses on generating confident that a machine satisfies sure requirements just before enabling it to accessibility the network. In the situation of a Windows product for case in point, the product may possibly be required to have the Windows Firewall enabled, antivirus software program put in, and the newest Windows updates set up.
- Least Privileged Obtain is the norm. People are specified entry to only those people sources that are needed for a consumer to do their work, and almost nothing far more. On top of that, buyers only receive compose accessibility to a source if these entry is essential.
- AI is made use of to enrich security. Artificial Intelligence and equipment studying check the network and detect any sort of irregular conduct that could signal a security issue.
Any illustrations in which a zero believe in product would have prevented a cyber-attack?
Most security breaches could conceivably have been stopped by a zero have confidence in design. Think about, for case in point, the notorious information breach of retailer Focus on in 2013. The attackers gained accessibility to Target’s gateway by employing stolen qualifications and then exploited many weaknesses to gain entry to the shopper support databases.
The zero rely on basic principle of multi-factor authentication could have stopped stolen credentials from getting made use of in the to start with position. Even if the attacker had managed to log in, however, employing minimum privilege entry correctly may well have stopped the attacker from accessing the databases or planting malware (which was also section of the attack). Furthermore, security-oriented device finding out mechanisms may well have been ready to detect the abnormal activity and place a halt to the attack.
What about trusting the IT workers?
Though the zero have faith in product is most often used to IT methods, it is also crucial to notice that there are various means for personnel to compromise an organization’s security without owning to attack an IT system instantly. Even a little something as uncomplicated as a call to the organization’s service desk can put an organization’s security in jeopardy.
If a consumer ended up to call an organization’s assistance desk for support with an issue these types of as a password reset, the technician would probably take actions to try out to verify the user’s id. This may possibly include asking the person a security question this sort of as their personnel ID range. The problem with this is that there are any variety of means that an attacker can supply this information and use it to impersonate a legitimate person and get hold of obtain to their account through a fake password reset.
The assistance desk agent can also pose a menace to the organization’s security. After all, there is normally very little stopping the technician from simply resetting a user’s password (without obtaining a password reset ask for) and then making use of the reset password to gain access to the user’s account.
Specops Safe Company Desk can aid to do away with these types of security dangers, which is in holding with zero trust security concepts. For case in point, the helpdesk technician could validate the user’s identification by sending a one-use code to the user’s cellular system or by applying a 3rd-party authentication service this sort of as Okta Validate, PingID, Duo Security, or Symantec VIP to confirm the user’s identification. At the identical time, this resource can prohibit the technician from resetting the user’s password except if the user has confirmed their identity, thus confirming that the consumer has asked for the password reset as opposed to the technician heading rogue.
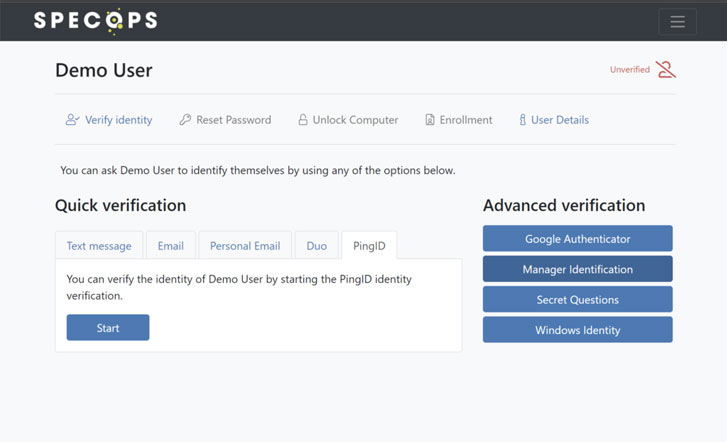 Specops Safe Support Desk on the backend
Specops Safe Support Desk on the backend
Summary
Although IT methods want to be configured in accordance with zero belief rules, an organization’s security is finally in the palms of the people and IT personnel. Software this sort of as Specops Secure Services Desk can help to make confident that people and helpdesk professionals are complying with the organization’s security needs.
Found this short article exciting? Abide by THN on Fb, Twitter and LinkedIn to go through additional unique written content we publish.
Some components of this article are sourced from:
thehackernews.com

 High-Severity RCE Flaw Disclosed in Several Netgear Router Models
High-Severity RCE Flaw Disclosed in Several Netgear Router Models