It is no top secret that sysadmins have a good deal on their plates. Running, troubleshooting, and updating software or hardware is a monotonous undertaking. Furthermore, admins should grapple with complicated webs of permissions and security. This can rapidly turn out to be too much to handle without the proper equipment.
If you might be a sysadmin in search of to simplify your workflows, you’re in luck. We’ve collected some superb computer software picks to assist deal with distinct responsibilities additional successfully.
Luckily, these free of charge applications are also respectful of restricted budgets—without sacrificing main features.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Very best for Permissions Management: SolarWinds Permissions Analyzer for Lively Listing
Regardless of whether you are component of an corporation with a lot of customers or numerous resources, maintaining track of permissions can be tough. Alterations in responsibilities, titles, or even work statuses can affect one’s entry to proprietary knowledge. Each and every consumer has unique privileges.
We not only want to visualize these but regulate them on a case-by-situation foundation. Earlier, this would require a deep, tiresome dive into file techniques, shares, and Advertisement groups.
SolarWinds Permissions Analyzer streamlines this process. At the time the software has method access, you might examine user permissions applying the lookup bars. This allows you cross-reference precise end users with essential file groups—showing read through accessibility, create or modify access, delete or develop capabilities, and even complete command.
How does Permissions Analyzer (PA) verify this?
This procedure is very speedy. Referring to the determine previously mentioned, the way SolarWinds displays this information and facts is its bread and butter. Permissions Analyzer organizes the output into a hierarchical table—including expandable groups primarily based on inheritance. For instance, you can see if team membership impacts particular permissions statuses.
This facts is demonstrated in concert with NTFS, Shares, and Full permissions. The GUI makes it possible for for quick usage making use of iconography and colour (partially adopting the traffic light-weight scheme). Thus, PA excels the place possibilities drop shorter: simplicity and usability.
Be aware that SolarWinds Permissions Analyzer is an investigative device. It doesn’t permit you to edit permissions in the application having said that, it offers swift visibility into your permissions framework.
Finest for Boosting Password Security: Specops Password Auditor
Active Directory password security is vitally crucial, still many companies routinely are unsuccessful small. Groups can institute password policies—both broad and high-quality-grained. But, are these attempts adequate? Specops Password Auditor can solution that issue and additional for you.
Password Auditor does what its namesake implies by scanning all user accounts inside of your atmosphere to detect leaked passwords. Specops maintains a dictionary of compromised passwords ought to any person passwords match, Password Auditor highlights them inside of the tool.
The central dashboard shows the adhering to in a unified perspective:
- Breached passwords (and their corresponding people)
- Similar passwords (and matching customers)
- Admin account names and stale variants
- Accounts with expired passwords
- Numerous password policies according to people, roles, and security
- Password plan utilization and compliance (go, caution, are unsuccessful)

This breakdown is less complicated to examine at a glance than most other people out there—including some paid out selections. It really is also a great dietary supplement to Azure Ad Password Security. Even though that functionally applies password policies to area controllers, Password Auditor establishes if these guidelines are in the end operating effectively.
Are dormant accounts resulting in issues? Maybe password length and complexity usually are not up to snuff. Password Auditor can drop mild on these issues.
Like SolarWinds Permissions Analyzer, Specops’ tool conducts a scan of your buyers and procedures. This system is fast and quick to watch. Password Auditor immediately compiles a report of its conclusions, which is obtainable as a downloadable PDF. You may well also export to CSV.
Future, you can measure your guidelines towards criteria set by NIST, PCI, Microsoft, and SANS. It’s even easy to test your insurance policies from brute-force attacks. This promotes adherence to very best methods.
Anxious about possible tampering? Specops Password Auditor is a study-only application.
Finest for Network Visibility and Protocol Examination: Wireshark
For fans of the now-deprecated Microsoft Information Analyzer, Wireshark has emerged as a common replacement. The multi-platform device supports an expansive listing of functioning programs:
- Windows 8+ and Windows Server 2012(R)+
- macOS 10.12+
- Above a dozen versions of UNIX, Linux, and BSD
Wireshark can inspect hundreds of network protocols, and even when that record is frequently evolving. Appropriately, Wireshark can capture knowledge irrespective of whether you happen to be on line or offline, permitting for uninterrupted inspection. Wireshark also supports about 20 capture file formats.
You may possibly retrospectively parse logs working with your most popular interface—whether that be the GUI or the TShark terminal utility. Files compressed working with gzip can be uncompressed on the fly, which saves time.
Want to examine the packets traveling all over your network? Simply just consider gain of the a few-pane browser view, which retains info well arranged. Layouts also function collapsible sections—letting you expose further aspects on need or retain the interface uncluttered.
What else does Wireshark supply?
- Several show filters
- VoIP examination
- Genuine-time data reads more than ethernet, IEEE, Bluetooth, USB, token ring, and more
- Decryption for IPsec, Kerberos, SNMP, ISAKMP, SSL/TLS, WEP, WPA, and WPA2
- Customizable coloring policies
- Quick information export via XML, PostScript, CSV, or plain text
Wireshark stays open up resource to this working day, and the developers retain higher-high quality documentation on Wireshark’s web page and GitHub pages.
Most effective for Proactive Person-Password Management: Specops Password Notification Email
Even when your password policy is seem, it is really crucial to preserve passwords from becoming stale. This can protect against hackers from attaining repeat accessibility to a compromised account over the lengthy term.
Unanticipated expiry can also separate end users from vital methods. Appropriately, businesses implementing periodic password expiry need to glance no even further than Specops Password Notification.
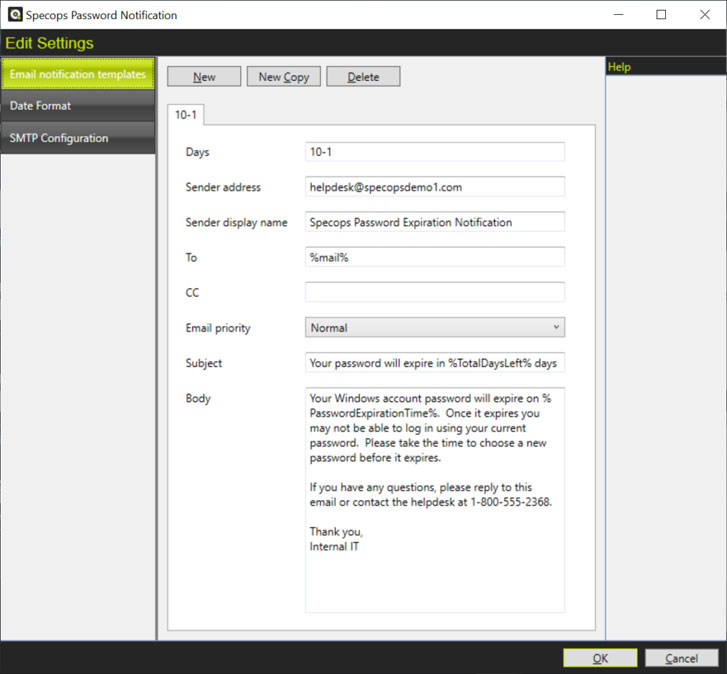
Password Notification’s premise is very very simple: protect against a lockout, thwart unwelcome entry, and hold buyers related from afar. Additionally, the goal is to reduce the stress on help desk technicians and universally prevent aggravation. How specifically does the resource function?
- The pwdLastSet attribute is compared to the maximum password age. This age is outlined in a specified area policy or wonderful-grained password policy
- Customers impacted by appropriate GPOs are sent notification emails when their password nears expiry. This warning interval, message, and subject matter are customizable
- IT admins can talk with all users—even people on remote networks or VPNs
Standard Windows people you should not receive these alerts when they are off the network.
How else can you tailor e-mails in Password Notification? Email frequency is adjustable, as are recipients (including numerous contacts). You can also established priority amounts that alter dynamically as deadlines solution. Seamless time zone integrations are also available.
Guide methods may well otherwise rely on scripting by way of PowerShell. Specops’ instrument offers users abundant functionality out of the box, without the need of the require for major configuration.
Discovered this posting attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to read far more special material we publish.
Some sections of this short article are sourced from:
thehackernews.com


 Dell and LORCA extend partnership to support UK security startups
Dell and LORCA extend partnership to support UK security startups