As lots of as 16 malicious apps with more than 20 million cumulative downloads have been taken down from the Google Participate in Keep right after they were being caught committing cellular advertisement fraud.
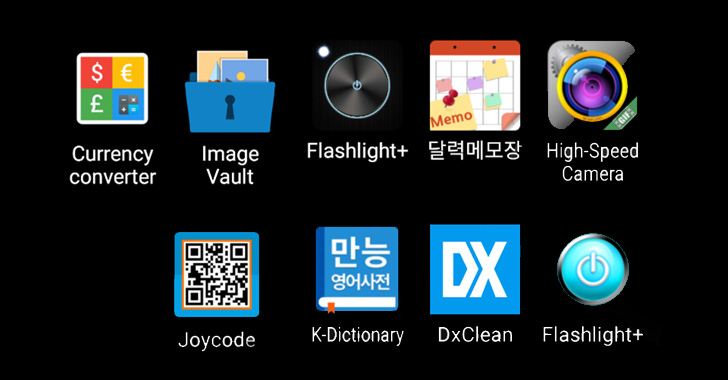
The Clicker malware masqueraded as seemingly harmless utilities like cameras, forex/unit converters, QR code audience, note-having apps, and dictionaries, among others, in a bid to trick people into downloading them, cybersecurity business McAfee claimed.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The list of offending apps is as follows –
- Large-Velocity Digicam (com.hantor.CozyCamera) – 10,000,000+ downloads
- Good Undertaking Manager (com.james.SmartTaskManager) – 5,000,000+ downloads
- Flashlight+ (kr.caramel.flash_moreover) – 1,000,000+ downloads
- 달력메모장 (com.smh.memocalendar) – 1,000,000+ downloads
- K-Dictionary (com.joysoft.wordBook) – 1,000,000+ downloads
- BusanBus (com.kmshack.BusanBus) – 1,000,000+ downloads
- Flashlight+ (com.candlencom.candleprotest) – 500,000+ downloads
- Fast Note (com.movinapp.quicknote) – 500,000+ downloads
- Forex Converter (com.smartwho.SmartCurrencyConverter) – 500,000+ downloads
- Joycode (com.joysoft.barcode) – 100,000+ downloads
- EzDica (com.joysoft.ezdica) – 100,000+ downloads
- Instagram Profile Downloader (com.schedulezero.instapp) – 100,000+ downloads
- Ez Notes (com.meek.tingboard) – 100,000+ downloads
- 손전등 (com.candlencom.flashlite) – 1,000+ downloads
- 계산기 (com.doubleline.calcul) – 100+ downloads
- Flashlight+ (com.dev.imagevault) – 100+ downloads
The Clicker application, after set up and launched, unleashes its fraudulent functionality that allows the malware to covertly visit bogus web sites and simulate advert clicks with no the victims’ expertise.

“This may perhaps result in weighty network site visitors and consume electric power without having consumer consciousness for the duration of the time it generates gain for the risk actor behind this malware,” McAfee researcher SangRyol Ryu explained.
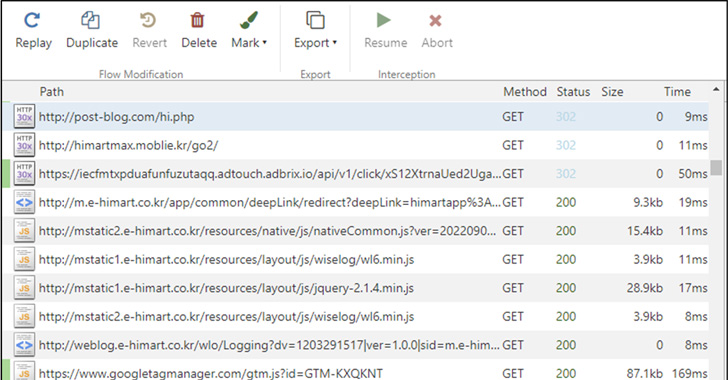
To further conceal its correct motive, the app takes into account the app’s set up time these kinds of that the suspicious action won’t kick in in the first one hour of downloading the application. It also incorporates a randomized delay in concerning to stay below the radar.
The results arrive two months after McAfee discovered a dozen Android adware apps distributed on the Google Perform Keep, which harbored a malware strain called HiddenAds that ended up located to execute quickly without having any person interaction.
“Clicker malware targets illicit promoting profits and can disrupt the cell promoting ecosystem,” Ryu mentioned. “Destructive behavior is cleverly concealed from detection.”
Observed this post exciting? Observe THN on Facebook, Twitter and LinkedIn to examine far more exclusive content material we put up.
Some sections of this short article are sourced from:
thehackernews.com

 Microsoft Misconfiguration Exposes Customer Data
Microsoft Misconfiguration Exposes Customer Data