Cybersecurity scientists have disclosed information about a new malware family members that depends on the Popular Log File Program (CLFS) to cover a 2nd-phase payload in registry transaction information in an endeavor to evade detection mechanisms.
FireEye’s Mandiant State-of-the-art Procedures crew, which made the discovery, dubbed the malware PRIVATELOG, and its installer, STASHLOG. Particulars about the identities of the menace actor or their motives continue to be unclear.
Whilst the malware is nonetheless to be detected in genuine-world attacks aimed at buyer environments or be spotted launching any 2nd-stage payloads, Mandiant suspects that PRIVATELOG could nonetheless be in enhancement, the do the job of a researcher, or deployed as portion of a highly qualified action.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
CLFS is a standard-function logging subsystem in Windows which is obtainable to each kernel-method as well as consumer-mode purposes this sort of as database units, OLTP systems, messaging shoppers, and network function management techniques for building and sharing superior-functionality transaction logs.
“Because the file structure is not extensively used or documented, there are no accessible instruments that can parse CLFS log data files,” Mandiant scientists defined in a create-up published this 7 days. “This presents attackers with an chance to disguise their details as log data in a handy way, mainly because these are available by way of API features.”
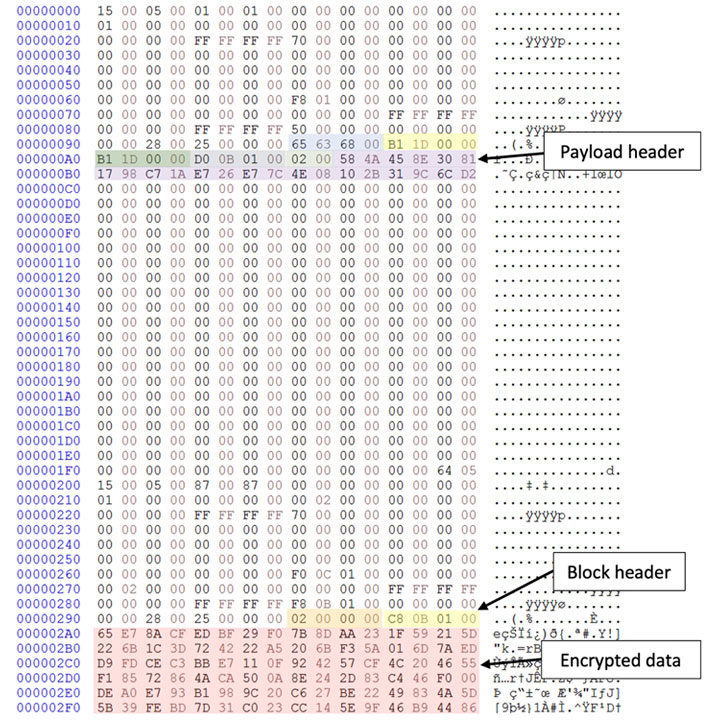
PRIVATELOG and STASHLOG come with capabilities that enable the destructive software to linger on infected gadgets and avoid detection, together with the use of obfuscated strings and manage circulation approaches that are expressly intended to make static investigation cumbersome. What is additional, the STASHLOG installer accepts a upcoming-stage payload as an argument, the contents of which are subsequently stashed in a distinct CLFS log file.
Fashioned as an un-obfuscated 64-bit DLL named “prntvpt.dll,” PRIVATELOG, in contrast, leverages a procedure named DLL look for get hijacking in purchase to load the destructive library when it is named by a sufferer plan, in this circumstance, a assistance identified as “PrintNotify.”
“Similarly to STASHLOG, PRIVATELOG starts off by enumerating *.BLF documents in the default user’s profile directory and makes use of the .BLF file with the oldest generation date timestamp,” the scientists famous, prior to employing it to decrypt and keep the next-stage payload.
Mandiant endorses that companies implement YARA principles to scan inner networks for signs of malware and observe out for opportunity Indicators of Compromise (IoCs) in “course of action”, “imageload” or “filewrite” activities associated with endpoint detection and response (EDR) method logs.
Discovered this report interesting? Observe THN on Facebook, Twitter and LinkedIn to read a lot more unique content material we post.
Some elements of this short article are sourced from:
thehackernews.com


 Amazon promises to be ‘more proactive’ in effort to remove harmful websites
Amazon promises to be ‘more proactive’ in effort to remove harmful websites