Cybersecurity scientists on Tuesday lifted the lid on a formerly undocumented malware pressure dubbed “MosaicLoader” that singles out men and women hunting for cracked software as part of a international campaign.
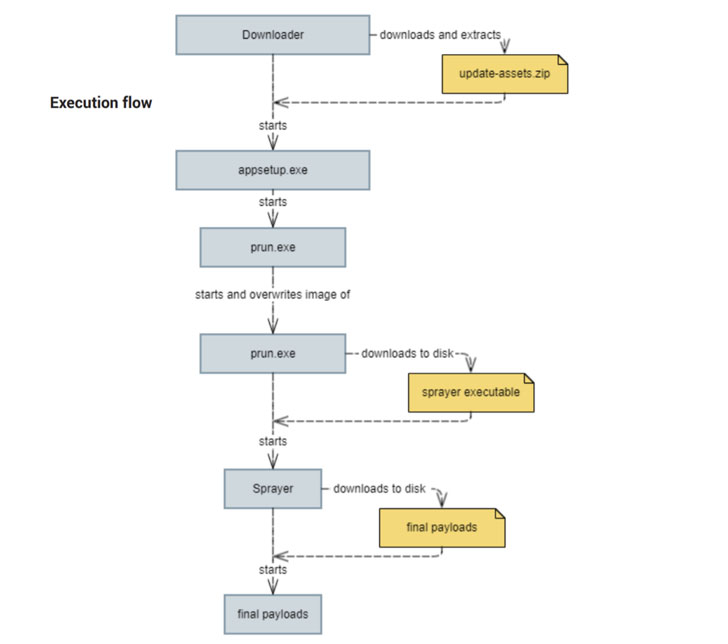
“The attackers powering MosaicLoader established a piece of malware that can supply any payload on the system, building it probably successful as a shipping and delivery service,” Bitdefender scientists mentioned in a report shared with The Hacker News. “The malware comes on target units by posing as cracked installers. It downloads a malware sprayer that obtains a listing of URLs from the C2 server and downloads the payloads from the been given backlinks.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The malware has been so named simply because of its sophisticated internal construction that is orchestrated to protect against reverse-engineering and evade examination.
Attacks involving MosaicLoader count on a very well-proven tactic for malware shipping known as lookup motor optimization (Search engine optimisation) poisoning, whereby cybercriminals order advertisement slots in search motor outcomes to enhance their malicious back links as best results when buyers search for conditions connected to pirated computer software.

On a successful infection, the initial Delphi-based dropper — which masquerades as a computer software installer — functions as an entry stage to fetch following-stage payloads from a remote server and also incorporate area exclusions in Windows Defender for the two downloaded executables in an attempt to thwart antivirus scanning.
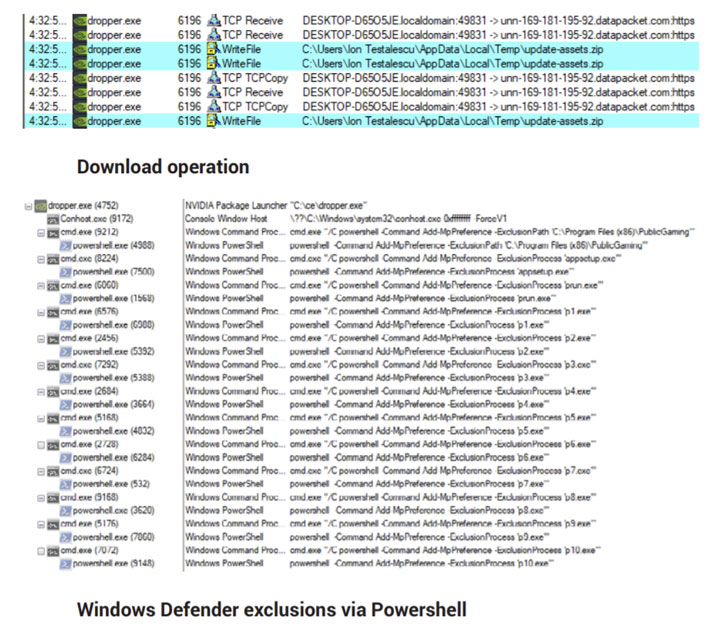
It is value pointing out that this sort of Windows Defender exclusions can be uncovered in the registry keys outlined under:
- File and folder exclusions – HKEY_Regional_MACHINESOFTWAREMicrosoftWindows DefenderExclusionsPaths
- File type exclusions – HKEY_Community_MACHINESOFTWAREMicrosoftWindows DefenderExclusionsExtensions
- Approach exclusions – HKEY_Regional_MACHINESOFTWAREMicrosoftWindows DefenderExclusionsProcesses
A person of the binaries, “appsetup.exe,” is conceived to obtain persistence on the system, while the second executable, “prun.exe,” features as a downloader for a sprayer module that can retrieve and deploy a range of threats from a list of URLs, ranging from cookie stealers to cryptocurrency miners, and even a lot more innovative implants like Glupteba.

“prun.exe” is also notable for its barrage of obfuscation and anti-reverse tactics that require separating code chunks with random filler bytes, with the execution circulation created to “soar more than these pieces and only execute the tiny, significant chunks.”
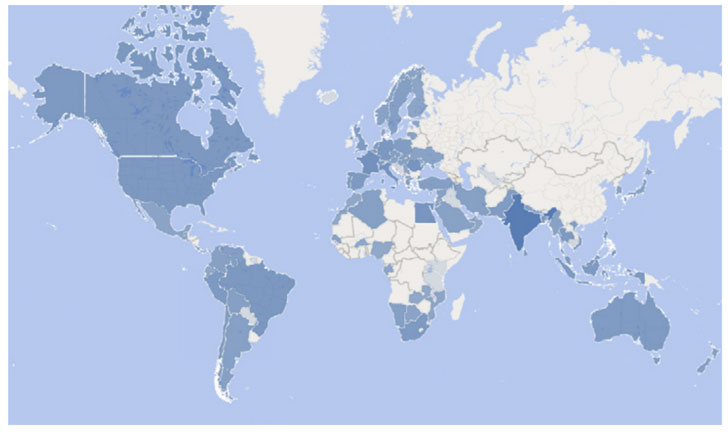
Specified MosaicLoader’s vast-ranging abilities, compromised systems can be co-opted into a botnet that the risk actor can then exploit to propagate several and evolving sets of sophisticated malware, such as each publicly out there and tailored malware, to obtain, expand, and manage unauthorized access to victim computer systems and networks.
“The very best way to protect from MosaicLoader is to prevent downloading cracked software program from any source,” the scientists explained. “Aside from currently being towards the legislation, cybercriminals seem to target and exploit users looking for unlawful software,” including it’s vital to “examine the resource area of each and every download to make guaranteed that the files are reputable.”
Found this article interesting? Stick to THN on Fb, Twitter and LinkedIn to study extra special content material we write-up.
Some areas of this short article are sourced from:
thehackernews.com


 US and Global Allies Accuse China of Massive Microsoft Exchange Attack
US and Global Allies Accuse China of Massive Microsoft Exchange Attack