Cybersecurity scientists on Tuesday disclosed a now-patched security flaw in TikTok that could have possibly enabled an attacker to make a database of the app’s consumers and their related phone figures for long term destructive exercise.
Despite the fact that this flaw only impacts these people who have joined a phone number with their account or logged in with a phone number, thriving exploitation of the vulnerability could have resulted in data leakage and privacy violation, Look at Position Investigation mentioned in an analysis shared with The Hacker News.
TikTok has deployed a take care of to tackle the shortcoming pursuing dependable disclosure from Look at Level scientists.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

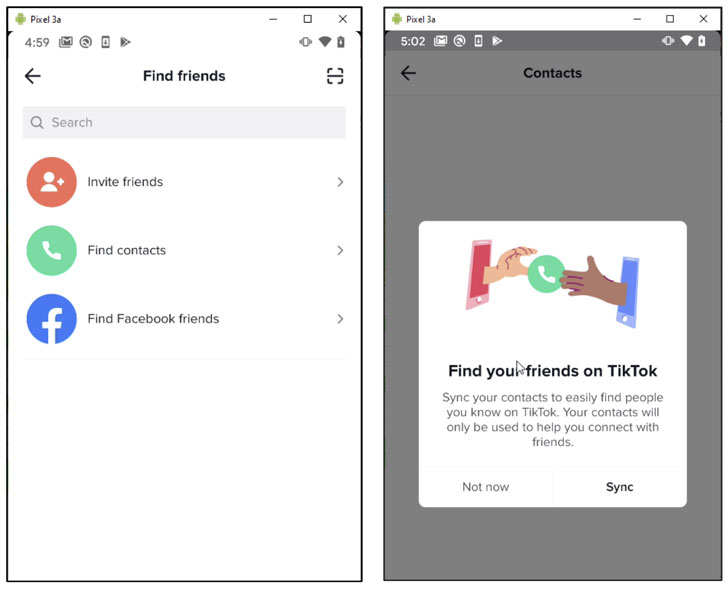
The newly learned bug resides in TikTok’s “Discover buddies” element that allows customers to sync their contacts with the support to determine prospective folks to abide by.
The contacts are uploaded to TikTok by way of an HTTP request in the sort of a checklist that is made up of hashed get hold of names and the corresponding phone figures.
The application, in the upcoming action, sends out a next HTTP ask for that retrieves the TikTok profiles related to the phone figures sent in the previous ask for. This reaction involves profile names, phone quantities, images, and other profile related details.
Whilst the add and sync contact requests are confined to 500 contacts for every working day, for each person, and for each system, Verify Stage scientists found a way to get close to the limitation by having keep of the device identifier, session cookies established by the server, a special token named “X-Tt-Token” that’s established when logging into the account with SMS and simulate the complete process from an emulator working Android 6..1.
It is really value noting that in get to request info from the TikTok software server, the HTTP requests ought to include X-Gorgon and X-Khronos headers for server verification, which makes sure that the messages are not tampered with.
But by modifying the HTTP requests — the selection of contacts the attacker desires to sync — and re-signing them with an updated concept signature, the flaw manufactured it achievable to automate the method of uploading and syncing contacts on a huge scale and create a databases of connected accounts and their related phone figures.
This is considerably from the to start with time the preferred video-sharing application has been discovered to comprise security weaknesses.
In January 2020, Examine Level researchers found various vulnerabilities within the TikTok application that could have been exploited to get hold of consumer accounts and manipulate their information, like deleting movies, uploading unauthorized films, generating non-public “concealed” video clips public, and revealing own info saved on the account.
Then in April, security researchers Talal Haj Bakry and Tommy Mysk exposed flaws in TikTok that made it doable for attackers to display forged movies, together with all those from verified accounts, by redirecting the application to a pretend server hosting a assortment of phony films.
Ultimately, TikTok introduced a bug bounty partnership with HackerOne last October to aid end users or security experts flag technical considerations with the system. Critical vulnerabilities (CVSS score 9 – 10) are suitable for payouts between $6,900 to $14,800, in accordance to the program.
“Our principal drive, this time all-around, was to check out the privacy of TikTok,” claimed Oded Vanunu, head of solutions vulnerabilities investigate at Look at Level. “We were being curious if the TikTok system could be made use of to achieve personal person info. It turns out that the solution was sure, as we have been ready to bypass numerous security mechanisms of TikTok that direct to privacy violation.”
“An attacker with that diploma of delicate details could carry out a vary of malicious things to do, this sort of as spear phishing or other legal steps.”
Located this article exciting? Stick to THN on Fb, Twitter and LinkedIn to read through extra exclusive information we submit.
Some pieces of this report are sourced from:
thehackernews.com


 Cook County Leaks 320,000 Court Records
Cook County Leaks 320,000 Court Records