Near to 14 million Linux-centered programs are right exposed to the Internet, producing them a profitable focus on for an array of real-earth attacks that could result in the deployment of malicious web shells, coin miners, ransomware, and other trojans.
Which is according to an in-depth glance at the Linux threat landscape published by U.S.-Japanese cybersecurity agency Craze Micro, detailing the top rated threats and vulnerabilities impacting the working process in the initially half of 2021, based on info amassed from honeypots, sensors, and anonymized telemetry.
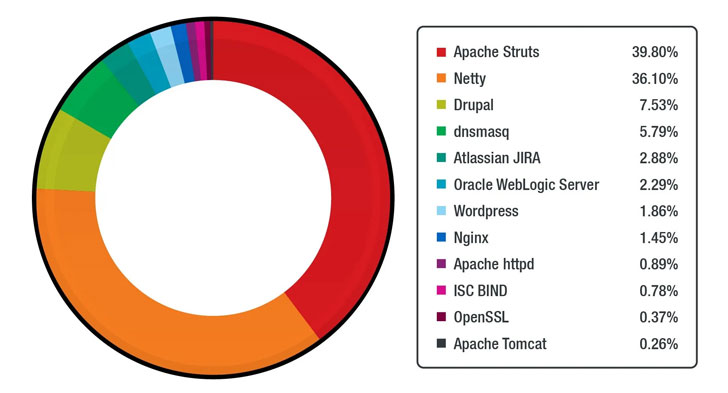
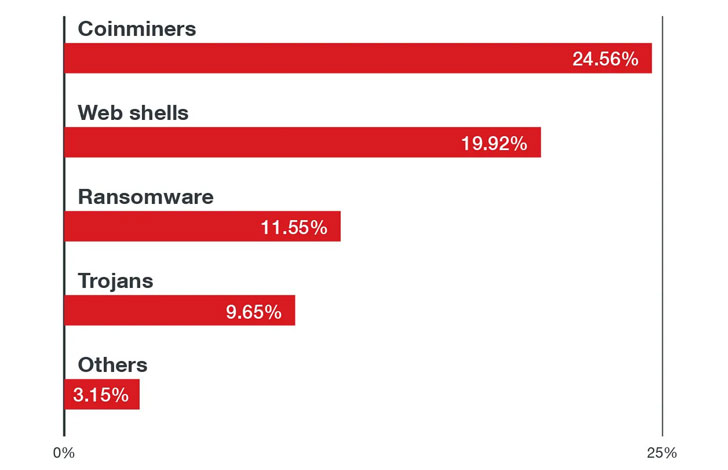
The enterprise, which detected nearly 15 million malware activities aimed at Linux-dependent cloud environments, found coin miners and ransomware to make up 54% of all malware, with web shells accounting for a 29% share.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In addition, by dissecting about 50 million events claimed from 100,000 special Linux hosts through the identical time time period, the scientists discovered 15 different security weaknesses that are identified to be actively exploited in the wild or have a evidence of concept (PoC) —
- CVE-2017-5638 (CVSS score: 10.) – Apache Struts 2 remote code execution (RCE) vulnerability
- CVE-2017-9805 (CVSS rating: 8.1) – Apache Struts 2 Rest plugin XStream RCE vulnerability
- CVE-2018-7600 (CVSS score: 9.8) – Drupal Main RCE vulnerability
- CVE-2020-14750 (CVSS score: 9.8) – Oracle WebLogic Server RCE vulnerability
- CVE-2020-25213 (CVSS rating: 10.) – WordPress File Supervisor (wp-file-manager) plugin RCE vulnerability
- CVE-2020-17496 (CVSS rating: 9.8) – vBulletin ‘subwidgetConfig’ unauthenticated RCE vulnerability
- CVE-2020-11651 (CVSS rating: 9.8) – SaltStack Salt authorization weak spot vulnerability
- CVE-2017-12611 (CVSS score: 9.8) – Apache Struts OGNL expression RCE vulnerability
- CVE-2017-7657 (CVSS rating: 9.8) – Eclipse Jetty chunk size parsing integer overflow vulnerability
- CVE-2021-29441 (CVSS score: 9.8) – Alibaba Nacos AuthFilter authentication bypass vulnerability
- CVE-2020-14179 (CVSS rating: 5.3) – Atlassian Jira details disclosure vulnerability
- CVE-2013-4547 (CVSS rating: 8.) – Nginx crafted URI string managing entry restriction bypass vulnerability
- CVE-2019-0230 (CVSS score: 9.8) – Apache Struts 2 RCE vulnerability
- CVE-2018-11776 (CVSS rating: 8.1) – Apache Struts OGNL expression RCE vulnerability
- CVE-2020-7961 (CVSS score: 9.8) – Liferay Portal untrusted deserialization vulnerability
Even additional troublingly, the 15 most generally made use of Docker photographs on the official Docker Hub repository has been discovered to harbor hundreds of vulnerabilities spanning throughout python, node, wordpress, golang, nginx, postgres, influxdb, httpd, mysql, debian, memcached, redis, mongo, centos, and rabbitmq, underscoring the need to protected containers from a huge vary of prospective threats at each individual stage of the progress pipeline.
“Consumers and companies need to often utilize security finest techniques, which include using the security by style and design technique, deploying multilayered digital patching or vulnerability shielding, using the theory of the very least privilege, and adhering to the shared obligation product,” the scientists concluded.
Uncovered this article exciting? Stick to THN on Fb, Twitter and LinkedIn to study much more special content we post.
Some parts of this write-up are sourced from:
thehackernews.com


 Modified PRISM backdoor used in new attacks
Modified PRISM backdoor used in new attacks