TrickBot, a person of the most notorious and adaptable malware botnets in the world, is growing its toolset to established its sights on firmware vulnerabilities to probably deploy bootkits and choose finish regulate of an infected program.
The new performance, dubbed “TrickBoot” by State-of-the-art Intelligence (AdvIntel) and Eclypsium, can make use of conveniently offered tools to check out gadgets for well-identified vulnerabilities that can permit attackers to inject malicious code in the UEFI/BIOS firmware of a system, granting the attackers an successful mechanism of persistent malware storage.
“This marks a significant phase in the evolution of TrickBot as UEFI amount implants are the deepest, most potent, and stealthy variety of bootkits,” the scientists claimed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“By introducing the potential to canvas sufferer units for unique UEFI/BIOS firmware vulnerabilities, TrickBot actors are equipped to focus on particular victims with firmware-level persistence that survives re-imaging or even gadget bricking capability.”
UEFI is a firmware interface and a alternative for BIOS that increases security, ensuring that no malware has tampered with the boot method. Because UEFI facilitates the loading of the operating process alone, this sort of bacterial infections are resistant to OS reinstallation or alternative of the tricky push.
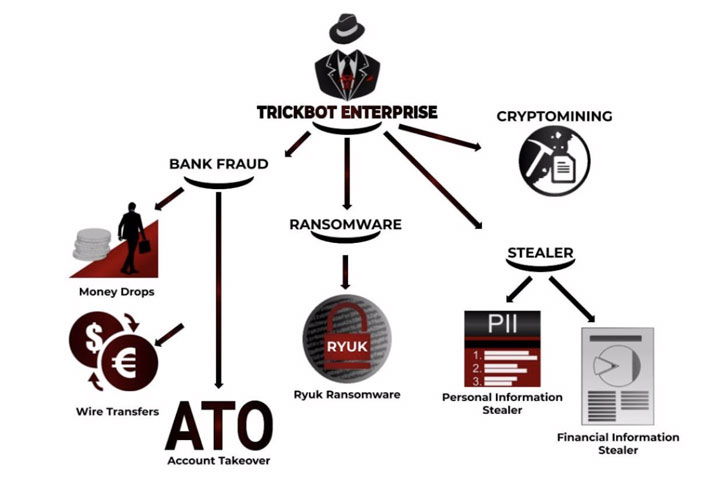
TrickBot emerged in 2016 as a banking trojan but has considering that progressed into a multi-objective malware-as-a-assistance (MaaS) that infects techniques with other destructive payloads created to steal credentials, email, money info, and unfold file-encrypting ransomware this sort of as Conti and Ryuk.
Its modularity and flexibility have designed it an excellent instrument for a diverse established of risk actors inspite of tries by cyber sellers to choose the infrastructure down. It has also been observed in conjunction with Emotet strategies to deploy Ryuk ransomware.
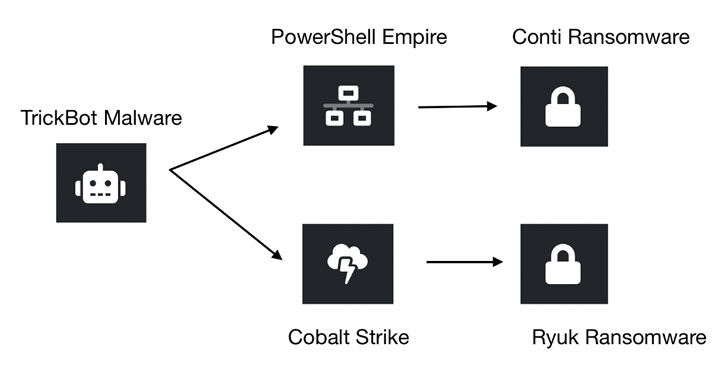
“Their most common attack chain mostly commences by using Emotet malspam campaigns, which then hundreds TrickBot and/or other loaders, and moves to attack equipment like PowerShell Empire or Cobalt Strike to carry out goals relative to the victim corporation underneath attack,” the researchers explained. “Usually, at the stop of the get rid of-chain, both Conti or Ryuk ransomware is deployed.”
To date, the botnet has infected much more than a million computer systems, in accordance to Microsoft and its companions at Symantec, ESET, FS-ISAC, and Lumen.
From a Reconnaissance Module to an Attack Function
The latest addition to their arsenal suggests that TrickBot can not only be employed to goal methods en masse with ransomware and UEFI attacks but also deliver legal actors even much more leverage during ransom negotiation by leaving a covert UEFI bootkit on the program for later on use.
The progress is also nevertheless one more indication that adversaries are extending their target further than the operating procedure of the product to decreased layers to steer clear of detection and carry out damaging or espionage-focused campaigns.
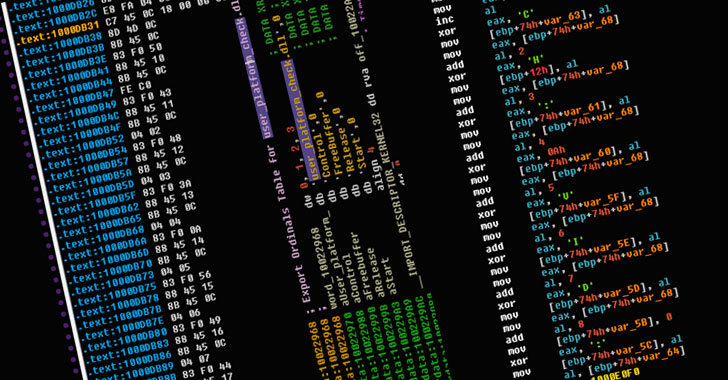
The scientists uncovered that TrickBot exclusively targets the SPI flash chip that houses the UEFI/BIOS firmware, utilizing an obfuscated duplicate of RWEverything tool’s RwDrv.sys driver to look at if the BIOS command register is unlocked and the contents of the BIOS region can be modified.
Whilst the activity is confined to reconnaissance so much, it would not be a stretch if this ability is extended to create malicious code to the technique firmware, thus guaranteeing that attacker code executes just before the running procedure and paving the way for the installation of backdoors, or even the destruction of a focused unit.
What is additional, specified the measurement and scope of the TrickBot, an attack of this type can have extreme consequences.
“TrickBoot is only just one line of code absent from getting equipped to brick any system it finds to be vulnerable,” the scientists pointed out. “The nationwide security implications arising from a widespread malware campaign able of bricking devices is monumental.”
With UEFI persistence, “TrickBot operators can disable any OS level security controls they want, which then permits them to re-floor to a modified OS with neutered endpoint protections and have out objectives with unhurried time on their side.”
To mitigate this kind of threats, it really is encouraged that the firmware is kept up-to-date, BIOS generate protections are enabled, and firmware integrity is verified to safeguard towards unauthorized modifications.
Found this write-up exciting? Adhere to THN on Facebook, Twitter and LinkedIn to read much more distinctive content material we article.
Some parts of this short article are sourced from:
thehackernews.com

 Philly Food Bank Loses $1m in BEC Scam
Philly Food Bank Loses $1m in BEC Scam