Cybersecurity scientists have opened the lid on the ongoing resurgence of the insidious TrickBot malware, generating it very clear that the Russia-primarily based transnational cybercrime group is doing work powering the scenes to revamp its attack infrastructure in response to latest counter attempts from law enforcement.
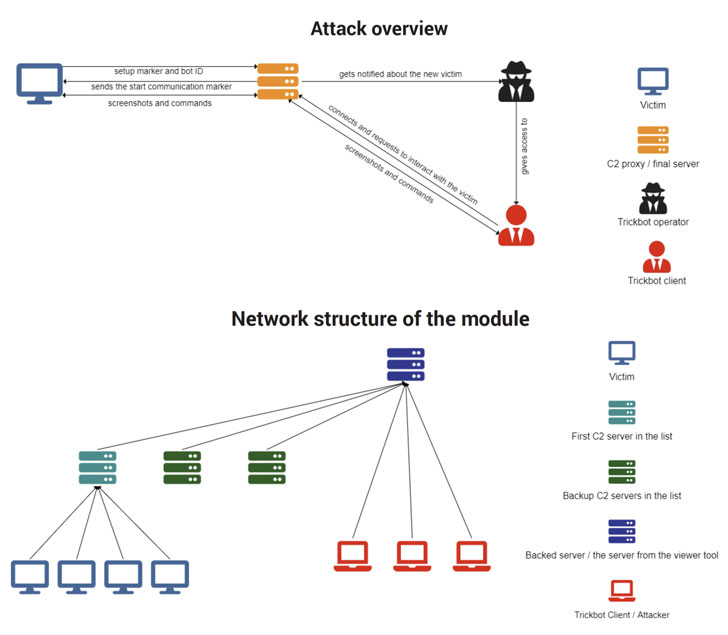
“The new capabilities learned are utilised to observe and get intelligence on victims, working with a personalized conversation protocol to conceal details transmissions in between [command-and-control] servers and victims — producing attacks difficult to place,” Bitdefender explained in a technical generate-up posted Monday, suggesting an enhance in sophistication of the group’s methods.
“Trickbot reveals no indicator of slowing down,” the scientists noted.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Botnets are shaped when hundreds or thousands of hacked devices are enlisted into a network run by felony operators, which are normally then used to launch denial-of-network attacks to pummel organizations and critical infrastructure with bogus site visitors with the aim of knocking them offline. But with command of these devices, destructive actors can also use botnets to spread malware and spam, or to deploy file-encrypting ransomware on the infected computer systems.
TrickBot is no distinct. The infamous cybercrime gang behind the operation — dubbed Wizard Spider — has a monitor record of exploiting the infected devices to steal sensitive data, pivot laterally throughout a network, and even turn out to be a loader for other malware, these types of as ransomware, whilst constantly improving their infection chains by incorporating modules with new performance to maximize its performance.
“TrickBot has advanced to use a sophisticated infrastructure that compromises 3rd-party servers and utilizes them to host malware,” Lumen’s Black Lotus Labs disclosed previous October. “It also infects purchaser appliances such as DSL routers, and its prison operators frequently rotate their IP addresses and infected hosts to make disruption of their criminal offense as tough as possible.”
The botnet has given that survived two takedown tries by Microsoft and the U.S. Cyber Command, with the operators developing firmware meddling components that could let the hackers to plant a backdoor in the Unified Extensible Firmware Interface (UEFI), enabling it to evade antivirus detection, software updates, or even a full wipe and reinstallation of the computer’s working method.

Now according to Bitdefender, the risk actor has been located actively acquiring an current model of a module named “vncDll” that it employs against pick substantial-profile targets for checking and intelligence accumulating. The new version has been named “tvncDll.”
The new module is built to converse with just one of the 9 command-and-control (C2) servers defined in its configuration file, making use of it to retrieve a set of attack commands, down load much more malware payloads, and exfiltrate collected from the equipment back again to the server. Also, the scientists stated they identified a “viewer instrument,” which the attackers use to interact with the victims via the C2 servers.
Even though initiatives to squash the gang’s operations may perhaps not have been solely prosperous, Microsoft explained to The Daily Beast that it labored with internet services vendors (ISPs) to go doorway-to-doorway replacing routers compromised with the Trickbot malware in Brazil and Latin The us, and that it properly pulled the plug on Trickbot infrastructure in Afghanistan.
Located this write-up intriguing? Comply with THN on Fb, Twitter and LinkedIn to browse far more unique content we publish.
Some sections of this short article are sourced from:
thehackernews.com

 Critical RCE Flaw in ForgeRock Access Manager Under Active Attack
Critical RCE Flaw in ForgeRock Access Manager Under Active Attack