The cybercrime operators behind the infamous TrickBot malware have when all over again upped the ante by wonderful-tuning its methods by including many levels of protection to slip previous antimalware products and solutions.
“As element of that escalation, malware injections have been equipped with included defense to hold researchers out and get as a result of security controls,” IBM Trusteer explained in a report. “In most situations, these excess protections have been utilized to injections employed in the method of on-line banking fraud — TrickBot’s main action given that its inception immediately after the Dyre Trojan’s demise.”
TrickBot, which commenced out as a banking trojan, has evolved into a multi-purpose crimeware-as-a-company (CaaS) that’s employed by a wide range of actors to provide added payloads this sort of as ransomware. More than 100 variants of TrickBot have been identified to day, a person of which is a “Trickboot” module that can modify the UEFI firmware of a compromised unit.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

In the slide of 2020, Microsoft along with a handful of U.S. government agencies and non-public security businesses teamed up to tackle the TrickBot botnet, taking down considerably of its infrastructure across the globe in a bid to stymie its functions.
But TrickBot has demonstrated to be impervious to takedown tries, what with the operators quickly modifying their procedures to propagate multi-stage malware via phishing and malspam attacks, not to point out expand their distribution channels by partnering with other affiliates like Shathak (aka TA551) to boost scale and drive earnings.
Additional not long ago, malware campaigns involving Emotet have piggybacked on TrickBot as a “shipping and delivery provider,” triggering an infection chain that drops the Cobalt Strike publish-exploitation device immediately on to compromised programs. As of December 2021, an estimated 140,000 victims throughout 149 countries have been infected by TrickBot.
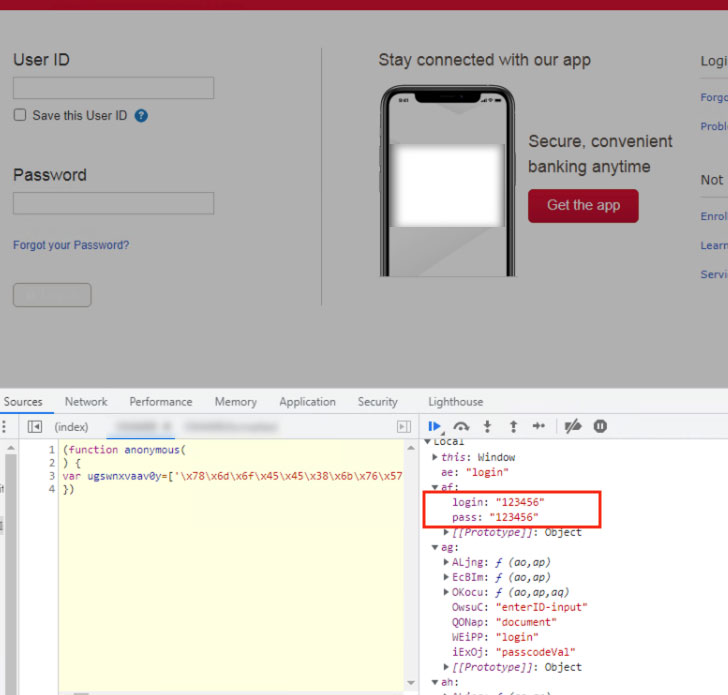
The new updates noticed by IBM Trusteer relate to the actual-time web injections made use of to steal banking credentials and browser cookies. This includes steering victims to duplicate domains when making an attempt to navigate to a banking portal as section of what is termed a male-in-the-browser (MitB) attack.
Also place to use is a server-aspect injection mechanism that intercepts the reaction from a bank’s server and redirects it to an attacker-managed server, which, in switch, inserts added code into the webpage before it is relayed back again to the customer.
“To facilitate fetching the appropriate injection at the correct instant, the resident TrickBot malware makes use of a downloader or a JavaScript (JS) loader to connect with its inject server,” mentioned Michael Gal, a security web researcher at IBM.
Other lines of protection adopted the latest model of TrickBot demonstrates the use of encrypted HTTPS communications with the command-and-regulate (C2) server for fetching injections an anti-debugging system to thwart investigation and new ways to obfuscate and hide the web inject, such as the addition of redundant code and incorporation of hex representation for initializing variables.
Specifically, upon detecting any attempt produced to beautify code, TrickBot’s anti-debugging characteristic triggers a memory overload that would crash the site, effectively protecting against any examination of the malware.
“The TrickBot Trojan and the gang that operates it have been a cyber crime staple considering the fact that they took more than when a predecessor, Dyre, went bust in 2016,” Gal mentioned. “TrickBot has not rested a day. Involving takedown attempts and a world wide pandemic, it has been diversifying its monetization products and growing more robust.”
Observed this posting interesting? Comply with THN on Facebook, Twitter and LinkedIn to go through more exclusive content material we article.
Some parts of this posting are sourced from:
thehackernews.com


 UK’s first government cyber strategy aims to bolster public sector defences
UK’s first government cyber strategy aims to bolster public sector defences