The operators of TrickBot trojan are collaborating with the Shathak danger group to distribute their wares, ultimately main to the deployment of Conti ransomware on infected devices.
“The implementation of TrickBot has evolved about the years, with new variations of TrickBot applying malware-loading abilities,” Cybereason security analysts Aleksandar Milenkoski and Eli Salem said in a report analysing latest malware distribution strategies undertaken by the team. “TrickBot has performed a big job in many attack campaigns performed by unique danger actors, from common cybercriminals to nation-state actors.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The newest report builds on a report from IBM X-Drive past thirty day period, which unveiled TrickBot’s partnerships with other cybercrime gangs, such as Shathak, to provide proprietary malware. Also tracked under the moniker TA551, Shathak is a complex cybercrime actor focusing on end-customers on a world-wide scale, performing as a malware distributor by leveraging password-guarded ZIP archives that contains macro-enabled Business office documents.
The TrickBot gang, known as ITG23 or Wizard Spider, is also accountable for building and retaining the Conti ransomware, in addition to leasing accessibility to the malicious application to affiliate marketers by means of a ransomware-as-a-services (RaaS) model.
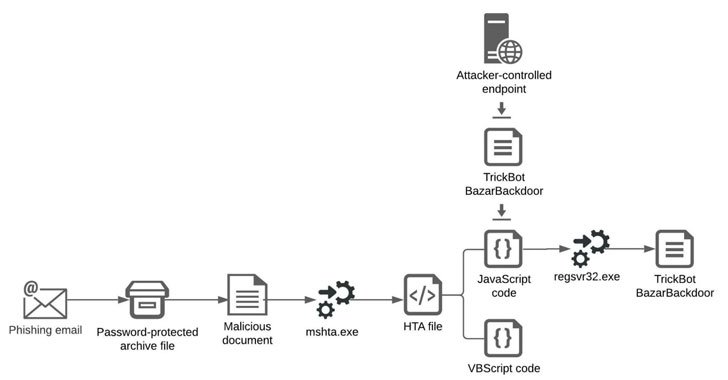
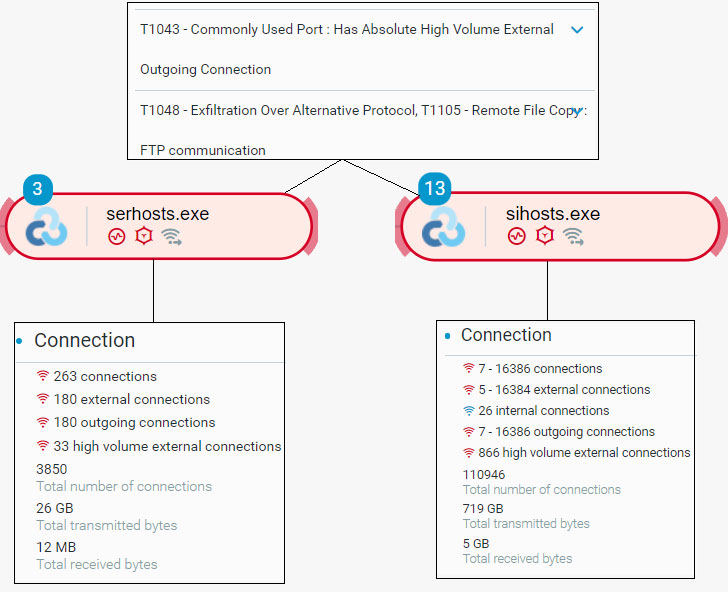
An infection chains involving Shathak generally require sending phishing e-mail that appear embedded with malware-laced Phrase files that finally lead to the deployment of TrickBot or BazarBackdoor malware, which is then utilized as a conduit to deploy Cobalt Strike beacons as effectively as the ransomware, but not right before conducting reconnaissance, lateral motion, credential theft, and information exfiltration actions.

Cybereason scientists mentioned they observed an average Time-to-Ransom (TTR) of two days submit the compromises, denoting the total of time from when the threat actor gains initial accessibility into a network to the time the threat actor truly deploys the ransomware.
The conclusions also arrive as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) claimed that no much less than 400 Conti ransomware attacks had taken place focusing on U.S. and global corporations as of September 2021.
To secure programs against Conti ransomware, the agencies advocate implementing a assortment of mitigation measures, like “demanding multi-factor authentication (MFA), utilizing network segmentation, and keeping operating programs and software package up to day.”
Discovered this post intriguing? Comply with THN on Fb, Twitter and LinkedIn to go through extra special content material we put up.
Some elements of this posting are sourced from:
thehackernews.com

 Researchers Uncover Prolific Hacker-for-Hire Group
Researchers Uncover Prolific Hacker-for-Hire Group