Transportation market and governing administration organizations associated to the sector are the victims of an ongoing campaign since July 2020 by a subtle and well-outfitted cyberespionage group in what seems to be nevertheless an additional uptick in malicious routines that are “just the suggestion of the iceberg.”
“The team tried out to obtain some inside paperwork (this kind of as flight schedules and paperwork for economical plans) and private information on the compromised hosts (these as search histories),” Development Micro scientists Nick Dai, Ted Lee, and Vickie Su stated in a report released final 7 days.
Earth Centaur, also recognised by the monikers Pirate Panda and Tropic Trooper, is a very long-functioning danger team concentrated on info theft and espionage that has led targeted strategies against govt, healthcare, transportation, and superior-tech industries in Taiwan, the Philippines, and Hong Kong dating all the way back again to 2011.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The hostile agents, considered to be a Chinese-speaking actor, are identified for their use of spear-phishing e-mail with weaponized attachments to exploit recognised vulnerabilities, when simultaneously advancing their destructive resources with obfuscation, stealthiness, and hanging electric power.
“This menace group is proficient at pink teamwork,” the scientists elaborated. “The team understands how to bypass security options and keep its procedure unobstructive. The use of the open up-supply frameworks also permits the group to build new backdoor variants successfully.”
In Could 2020, the operators were observed high-quality-tuning their attack methods with new behaviors by deploying a USB trojan dubbed USBFerry to strike bodily isolated networks belonging to governing administration institutions and armed service entities in Taiwan and the Philippines in a bid to siphon sensitive details by means of detachable flash drives.
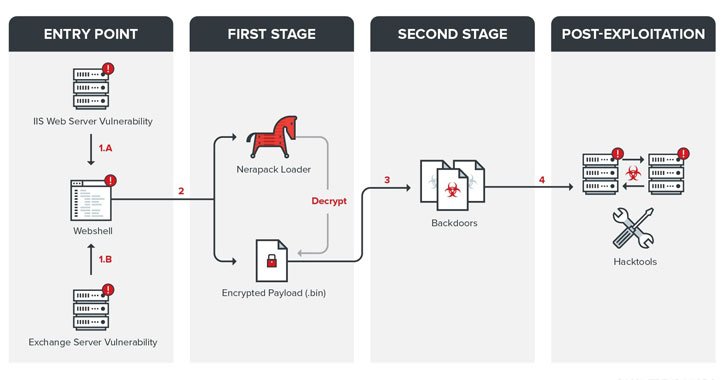
The most up-to-date multi-stage intrusion sequence in-depth by Pattern Micro includes the group turning to exploit vulnerable Internet Info Providers (IIS) servers and Trade server flaws as entry details to install a web shell that’s then leveraged to supply a .NET-based mostly Nerapack loader and a initial-phase backdoor identified as Quasar on the compromised program.
From there, the attackers abide by it up by dropping an arsenal of second-phase implants like ChiserClient, SmileSvr, ChiserClient, HTShell, and bespoke variations of Lilith RAT and Gh0st RAT relying on the victim to retrieve additional recommendations from a remote server, download more payloads, carry out file operations, execute arbitrary instructions, and exfiltrate effects again to the server.
It won’t close there. Immediately after thriving exploitation of the system, Tropic Trooper also tries to breach the intranet, dump qualifications, and wipe out celebration logs from the contaminated machines using a precise established of resources. Also place to use is a command-line method named Rclone that permits the actor to copy harvested data to unique cloud storage providers.
“Currently, we have not found substantial damage to these victims as brought about by the menace team,” Craze Micro’s analysts explained. “Nevertheless, we think that it will carry on accumulating interior information from the compromised victims and that it is basically ready for an opportunity to use this details.”
The findings are noteworthy mainly because of the measures the innovative persistent menace (APT) usually takes to avoid detection and the critical nature of the focused entities, not to mention the new capabilities designed for their destructive computer software to linger on contaminated hosts and keep away from detection.
“The team can map their target’s network infrastructure and bypass firewalls,” the researchers explained. “It employs backdoors with diverse protocols, which are deployed depending on the target. It also has the ability to acquire custom made equipment to evade security monitoring in distinct environments, and it exploits susceptible internet sites and uses them as [command-and-control] servers.”
Identified this post attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to browse extra exceptional content we publish.
Some pieces of this post are sourced from:
thehackernews.com


 T-Mobile: Scam calls hit an all-time high in 2021
T-Mobile: Scam calls hit an all-time high in 2021