The Wi-Fi network name bug that was discovered to totally disable an iPhone’s networking performance experienced distant code execution abilities and was silently preset by Apple before this calendar year, according to new investigation.
The denial-of-services vulnerability, which came to light-weight previous thirty day period, stemmed from the way iOS taken care of string formats connected with the SSID input, triggering a crash on any up-to-date iPhone that related to any wireless access factors with per cent symbols in their names these types of as “%p%s%s%s%s%n.”
Even though the issue is remediable by resetting the network configurations (Options > General > Reset > Reset Network Settings), Apple is predicted to force a patch for the bug in its iOS 14.7 update, which is now out there to developers and general public beta testers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

But in what could have experienced significantly-reaching implications, researchers from cell security automation company ZecOps uncovered that the same bug could be exploited to obtain remote code execution (RCE) on focused devices by attaching the string pattern “%@” to the Wi-Fi hotspot’s title.
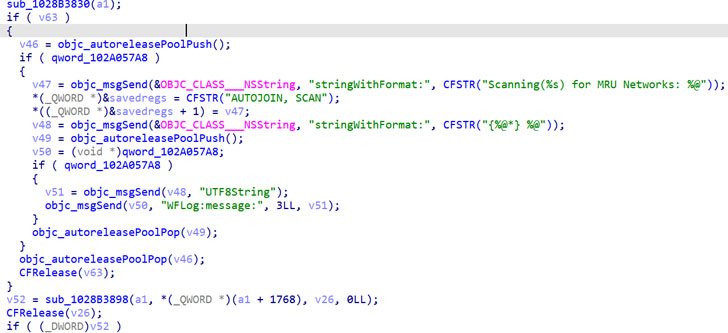
ZecOps nicknamed the issue “WiFiDemon.” It’s also a zero-click vulnerability in that it lets the danger actor to infect a gadget with out necessitating any person interaction, although it demands that the setting to routinely sign up for Wi-Fi networks is enabled (which it is, by default).
“As very long as the WiFi is turned on this vulnerability can be brought on,” the scientists pointed out. “If the consumer is related to an existing WiFi network, an attacker can start a different attack to disconnect/de-associate the gadget and then launch this -click attack.”

“This -simply click vulnerability is potent: if the malicious obtain level has password protection and the user never joins the wifi, absolutely nothing will be saved to the disk,” the firm extra. “Immediately after turning off the destructive accessibility point, the user’s WIFI perform will be normal. A consumer could barely observe if they have been attacked.”
All iOS versions starting with iOS 14. and prior to iOS 14.3 have been discovered to be vulnerable to the RCE variant, with Apple “silently” patching the issue in January 2021 as aspect of its iOS 14.4 update. No CVE identifier was assigned to the flaw.
Presented the exploitable character of the bug, it is really remarkably proposed that iPhone and iPad consumers update their devices to the newest iOS variation to mitigate the risk related with the vulnerability.
Uncovered this write-up fascinating? Comply with THN on Fb, Twitter and LinkedIn to browse extra distinctive content material we publish.
Some areas of this posting are sourced from:
thehackernews.com


 More customers, more threats?
More customers, more threats?