In what is however a different occasion of source chain attack concentrating on open up-source computer software repositories, two well-known NPM packages with cumulative weekly downloads of almost 22 million were identified to be compromised with destructive code by getting unauthorized obtain to the respective developer’s accounts.
The two libraries in issue are “coa,” a parser for command-line alternatives, and “rc,” a configuration loader, each of which ended up tampered by an unidentified menace actor to contain “equivalent” password-stealing malware.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
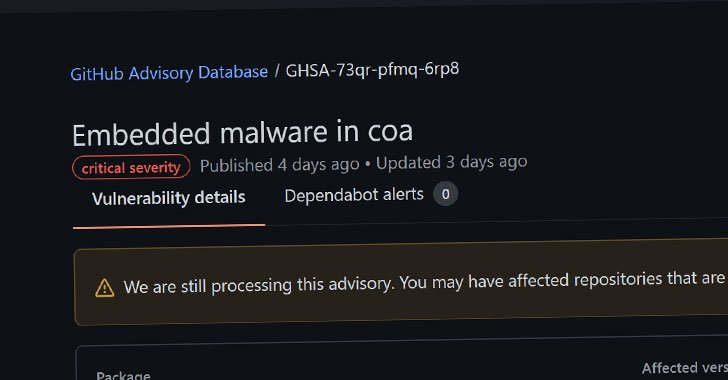
All variations of coa starting off with 2..3 and earlier mentioned — 2..3, 2..4, 2.1.1, 2.1.3, 3..1, and 3.1.3 — are impacted, and customers of the influenced versions are suggested to downgrade to 2..2 as soon as achievable and check their devices for suspicious action, in accordance to a GitHub advisory published on November 4. In a equivalent vein, versions 1.2.9, 1.3.9, and 2.3.9 of rc have been observed laced with malware, with an impartial alert urging buyers to downgrade to edition 1.2.8.
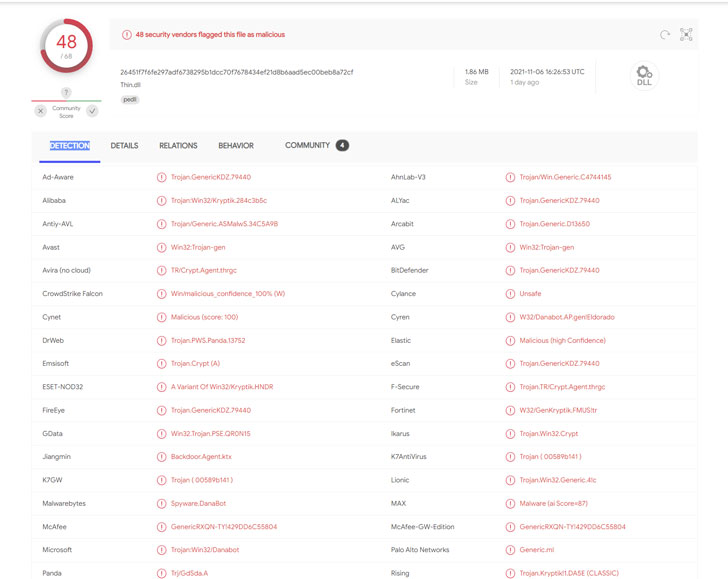
Extra investigation of the dropped malware samples present it be a DanaBot variant which is a Windows malware for thieving qualifications and passwords, echoing two related incidents from final thirty day period that resulted in the compromise of UAParser.js as very well as the publishing of rogue, typosquatted Roblox NPM libraries.

“To protect your accounts and deals from comparable attacks, we highly advise enabling [two-factor authentication] on your NPM account,” NPM mentioned in a tweet.
Found this posting intriguing? Comply with THN on Facebook, Twitter and LinkedIn to browse more special material we write-up.
Some elements of this write-up are sourced from:
thehackernews.com

 Ohio Schools Get New Cybersecurity Resource
Ohio Schools Get New Cybersecurity Resource